1BO4r2U
1BO4r2U
1BO4r2U
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
39 40<br />
Web Application Penetration Testing<br />
Web Application Penetration Testing<br />
WhatWeb<br />
Website: http:/www.morningstarsecurity.com/research/whatweb<br />
Currently one of the best fingerprinting tools on the market. Included<br />
in a default Kali Linux build. Language: Ruby Matches for fingerprinting<br />
are made with:<br />
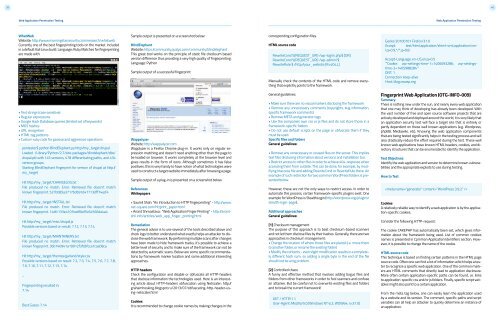
Sample output is presented on a screenshot below:<br />
BlindElephant<br />
Website: https:/community.qualys.com/community/blindelephant<br />
This great tool works on the principle of static file checksum based<br />
version difference thus providing a very high quality of fingerprinting.<br />
Language: Python<br />
Sample output of a successful fingerprint:<br />
corresponding configuration files.<br />
HTML source code<br />
RewriteCond %{REQUEST_URI} /wp-login\.php$ [OR]<br />
RewriteCond %{REQUEST_URI} /wp-admin/$<br />
RewriteRule $ /http:/your_website [R=404,L]<br />
Manually check the contents of the HTML code and remove everything<br />
that explicitly points to the framework.<br />
Gecko/20100101 Firefox/31.0<br />
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8<br />
Accept-Language: en-US,en;q=0.5<br />
‘’’Cookie: wp-settings-time-1=1406093286; wp-settingstime-2=1405988284’’’<br />
DNT: 1<br />
Connection: keep-alive<br />
Host: blog.owasp.org<br />
• Text strings (case sensitive)<br />
• Regular expressions<br />
• Google Hack Database queries (limited set of keywords)<br />
• MD5 hashes<br />
• URL recognition<br />
• HTML tag patterns<br />
• Custom ruby code for passive and aggressive operations<br />
pentester$ python BlindElephant.py http:/my_target drupal<br />
Loaded /Library/Python/2.7/site-packages/blindelephant/dbs/<br />
drupal.pkl with 145 versions, 478 differentiating paths, and 434<br />
version groups.<br />
Starting BlindElephant fingerprint for version of drupal at http:/<br />
my_target<br />
Hit http:/my_target/CHANGELOG.txt<br />
File produced no match. Error: Retrieved file doesn’t match<br />
known fingerprint. 527b085a3717bd691d47713dff74acf4<br />
Hit http:/my_target/INSTALL.txt<br />
File produced no match. Error: Retrieved file doesn’t match<br />
known fingerprint. 14dfc133e4101be6f0ef5c64566da4a4<br />
Hit http:/my_target/misc/drupal.js<br />
Possible versions based on result: 7.12, 7.13, 7.14<br />
Hit http:/my_target/MAINTAINERS.txt<br />
File produced no match. Error: Retrieved file doesn’t match<br />
known fingerprint. 36b740941a19912f3fdbfcca7caa08ca<br />
Hit http:/my_target/themes/garland/style.css<br />
Possible versions based on result: 7.2, 7.3, 7.4, 7.5, 7.6, 7.7, 7.8,<br />
7.9, 7.10, 7.11, 7.12, 7.13, 7.14<br />
...<br />
Fingerprinting resulted in:<br />
7.14<br />
Best Guess: 7.14<br />
Wappalyzer<br />
Website: http:/wappalyzer.com<br />
Wapplyzer is a Firefox Chrome plug-in. It works only on regular expression<br />
matching and doesn’t need anything other than the page to<br />
be loaded on browser. It works completely at the browser level and<br />
gives results in the form of icons. Although sometimes it has false<br />
positives, this is very handy to have notion of what technologies were<br />
used to construct a target website immediately after browsing a page.<br />
Sample output of a plug-in is presented on a screenshot below.<br />
References<br />
Whitepapers<br />
• Saumil Shah: “An Introduction to HTTP fingerprinting” - http:/www.<br />
net-square.com/httprint_paper.html<br />
• Anant Shrivastava : “Web Application Finger Printing” - http:/anantshri.info/articles/web_app_finger_printing.html<br />
Remediation<br />
The general advice is to use several of the tools described above and<br />
check logs to better understand what exactly helps an attacker to disclose<br />
the web framework. By performing multiple scans after changes<br />
have been made to hide framework tracks, it’s possible to achieve a<br />
better level of security and to make sure of the framework can not be<br />
detected by automatic scans. Below are some specific recommendations<br />
by framework marker location and some additional interesting<br />
approaches.<br />
HTTP headers<br />
Check the configuration and disable or obfuscate all HTTP-headers<br />
that disclose information the technologies used. Here is an interesting<br />
article about HTTP-headers obfuscation using Netscaler: http:/<br />
grahamhosking.blogspot.ru/2013/07/obfuscating-http-header-using-netscaler.html<br />
Cookies<br />
It is recommended to change cookie names by making changes in the<br />
General guidelines:<br />
• Make sure there are no visual markers disclosing the framework<br />
• Remove any unnecessary comments (copyrights, bug information,<br />
specific framework comments)<br />
• Remove META and generator tags<br />
• Use the companies own css or js files and do not store those in a<br />
framework-specific folders<br />
• Do not use default scripts on the page or obfuscate them if they<br />
must be used.<br />
Specific files and folders<br />
General guidelines:<br />
• Remove any unnecessary or unused files on the server. This implies<br />
text files disclosing information about versions and installation too.<br />
• Restrict access to other files in order to achieve 404-response when<br />
accessing them from outside. This can be done, for example, by modifying<br />
htaccess file and adding RewriteCond or RewriteRule there. An<br />
example of such restriction for two common WordPress folders is presented<br />
below.<br />
However, these are not the only ways to restrict access. In order to<br />
automate this process, certain framework-specific plugins exist. One<br />
example for WordPress is StealthLogin (http:/wordpress.org/plugins/<br />
stealth-login-page).<br />
Additional approaches<br />
General guidelines:<br />
[1] Checksum management<br />
The purpose of this approach is to beat checksum-based scanners<br />
and not let them disclose files by their hashes. Generally, there are two<br />
approaches in checksum management:<br />
• Change the location of where those files are placed (i.e. move them<br />
to another folder, or rename the existing folder)<br />
• Modify the contents - even slight modification results in a completely<br />
different hash sum, so adding a single byte in the end of the file<br />
should not be a big problem.<br />
[2] Controlled chaos<br />
A funny and effective method that involves adding bogus files and<br />
folders from other frameworks in order to fool scanners and confuse<br />
an attacker. But be careful not to overwrite existing files and folders<br />
and to break the current framework!<br />
GET / HTTP/1.1<br />
User-Agent: Mozilla/5.0 (Windows NT 6.2; WOW64; rv:31.0)<br />
Fingerprint Web Application (OTG-INFO-009)<br />
Summary<br />
There is nothing new under the sun, and nearly every web application<br />
that one may think of developing has already been developed. With<br />
the vast number of free and open source software projects that are<br />
actively developed and deployed around the world, it is very likely that<br />
an application security test will face a target site that is entirely or<br />
partly dependent on these well known applications (e.g. Wordpress,<br />
phpBB, Mediawiki, etc). Knowing the web application components<br />
that are being tested significantly helps in the testing process and will<br />
also drastically reduce the effort required during the test. These well<br />
known web applications have known HTML headers, cookies, and directory<br />
structures that can be enumerated to identify the application.<br />
Test Objectives<br />
Identify the web application and version to determine known vulnerabilities<br />
and the appropriate exploits to use during testing.<br />
How to Test<br />
<br />
Cookies<br />
A relatively reliable way to identify a web application is by the application-specific<br />
cookies.<br />
Consider the following HTTP-request:<br />
The cookie CAKEPHP has automatically been set, which gives information<br />
about the framework being used. List of common cookies<br />
names is presented in Cpmmon Application Identifiers section. However,<br />
it is possible to change the name of the cookie.<br />
HTML source code<br />
This technique is based on finding certain patterns in the HTML page<br />
source code. Often one can find a lot of information which helps a tester<br />
to recognize a specific web application. One of the common markers<br />
are HTML comments that directly lead to application disclosure.<br />
More often certain application-specific paths can be found, i.e. links<br />
to application-specific css and/or js folders. Finally, specific script variables<br />
might also point to a certain application.<br />
From the meta tag below, one can easily learn the application used<br />
by a website and its version. The comment, specific paths and script<br />
variables can all help an attacker to quickly determine an instance of<br />
an application.