1BO4r2U
1BO4r2U
1BO4r2U
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
161 162<br />
Web Application Penetration Testing<br />
Web Application Penetration Testing<br />
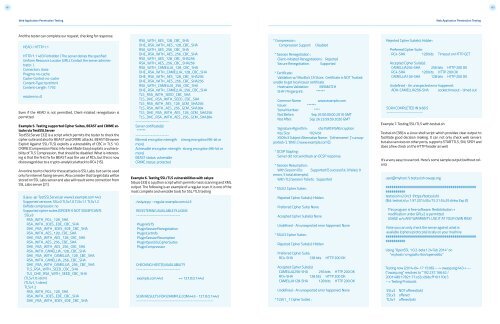
And the tester can complete our request, checking for response.<br />
HEAD / HTTP/1.1<br />
HTTP/1.1 403 Forbidden ( The server denies the specified<br />
Uniform Resource Locator (URL). Contact the server administrator.<br />
)<br />
Connection: close<br />
Pragma: no-cache<br />
Cache-Control: no-cache<br />
Content-Type: text/html<br />
Content-Length: 1792<br />
read:errno=0<br />
Even if the HEAD is not permitted, Client-intiated renegotiaion is<br />
permitted.<br />
Example 5. Testing supported Cipher Suites, BEAST and CRIME attacks<br />
via TestSSLServer<br />
TestSSLServer [32] is a script which permits the tester to check the<br />
cipher suite and also for BEAST and CRIME attacks. BEAST (Browser<br />
Exploit Against SSL/TLS) exploits a vulnerability of CBC in TLS 1.0.<br />
CRIME (Compression Ratio Info-leak Made Easy) exploits a vulnerability<br />
of TLS Compression, that should be disabled. What is interesting<br />
is that the first fix for BEAST was the use of RC4, but this is now<br />
discouraged due to a crypto-analytical attack to RC4 [15].<br />
An online tool to check for these attacks is SSL Labs, but can be used<br />
only for internet facing servers. Also consider that target data will be<br />
stored on SSL Labs server and also will result some connection from<br />
SSL Labs server [21].<br />
$ java -jar TestSSLServer.jar www3.example.com 443<br />
Supported versions: SSLv3 TLSv1.0 TLSv1.1 TLSv1.2<br />
Deflate compression: no<br />
Supported cipher suites (ORDER IS NOT SIGNIFICANT):<br />
SSLv3<br />
RSA_WITH_RC4_128_SHA<br />
RSA_WITH_3DES_EDE_CBC_SHA<br />
DHE_RSA_WITH_3DES_EDE_CBC_SHA<br />
RSA_WITH_AES_128_CBC_SHA<br />
DHE_RSA_WITH_AES_128_CBC_SHA<br />
RSA_WITH_AES_256_CBC_SHA<br />
DHE_RSA_WITH_AES_256_CBC_SHA<br />
RSA_WITH_CAMELLIA_128_CBC_SHA<br />
DHE_RSA_WITH_CAMELLIA_128_CBC_SHA<br />
RSA_WITH_CAMELLIA_256_CBC_SHA<br />
DHE_RSA_WITH_CAMELLIA_256_CBC_SHA<br />
TLS_RSA_WITH_SEED_CBC_SHA<br />
TLS_DHE_RSA_WITH_SEED_CBC_SHA<br />
(TLSv1.0: idem)<br />
(TLSv1.1: idem)<br />
TLSv1.2<br />
RSA_WITH_RC4_128_SHA<br />
RSA_WITH_3DES_EDE_CBC_SHA<br />
DHE_RSA_WITH_3DES_EDE_CBC_SHA<br />
RSA_WITH_AES_128_CBC_SHA<br />
DHE_RSA_WITH_AES_128_CBC_SHA<br />
RSA_WITH_AES_256_CBC_SHA<br />
DHE_RSA_WITH_AES_256_CBC_SHA<br />
RSA_WITH_AES_128_CBC_SHA256<br />
RSA_WITH_AES_256_CBC_SHA256<br />
RSA_WITH_CAMELLIA_128_CBC_SHA<br />
DHE_RSA_WITH_CAMELLIA_128_CBC_SHA<br />
DHE_RSA_WITH_AES_128_CBC_SHA256<br />
DHE_RSA_WITH_AES_256_CBC_SHA256<br />
RSA_WITH_CAMELLIA_256_CBC_SHA<br />
DHE_RSA_WITH_CAMELLIA_256_CBC_SHA<br />
TLS_RSA_WITH_SEED_CBC_SHA<br />
TLS_DHE_RSA_WITH_SEED_CBC_SHA<br />
TLS_RSA_WITH_AES_128_GCM_SHA256<br />
TLS_RSA_WITH_AES_256_GCM_SHA384<br />
TLS_DHE_RSA_WITH_AES_128_GCM_SHA256<br />
TLS_DHE_RSA_WITH_AES_256_GCM_SHA384<br />
----------------------<br />
Server certificate(s):<br />
******<br />
----------------------<br />
Minimal encryption strength: strong encryption (96-bit or<br />
more)<br />
Achievable encryption strength: strong encryption (96-bit or<br />
more)<br />
BEAST status: vulnerable<br />
CRIME status: protected<br />
Example 6. Testing SSL/TLS vulnerabilities with sslyze<br />
Sslyze [33] is a python script which permits mass scanning and XML<br />
output. The following is an example of a regular scan. It is one of the<br />
most complete and versatile tools for SSL/TLS testing<br />
./sslyze.py --regular example.com:443<br />
REGISTERING AVAILABLE PLUGINS<br />
-----------------------------<br />
PluginHSTS<br />
PluginSessionRenegotiation<br />
PluginCertInfo<br />
PluginSessionResumption<br />
PluginOpenSSLCipherSuites<br />
PluginCompression<br />
CHECKING HOST(S) AVAILABILITY<br />
-----------------------------<br />
example.com:443 => 127.0.0.1:443<br />
SCAN RESULTS FOR EXAMPLE.COM:443 - 127.0.0.1:443<br />
---------------------------------------------------<br />
* Compression :<br />
Compression Support:<br />
Disabled<br />
* Session Renegotiation :<br />
Client-initiated Renegotiations: Rejected<br />
Secure Renegotiation: Supported<br />
* Certificate :<br />
Validation w/ Mozilla’s CA Store: Certificate is NOT Trusted:<br />
unable to get local issuer certificate<br />
Hostname Validation: MISMATCH<br />
SHA1 Fingerprint: ******<br />
Common Name:<br />
www.example.com<br />
Issuer: ******<br />
Serial Number: ****<br />
Not Before:<br />
Sep 26 00:00:00 2010 GMT<br />
Not After:<br />
Sep 26 23:59:59 2020 GMT<br />
Signature Algorithm: sha1WithRSAEncryption<br />
Key Size:<br />
1024 bit<br />
X509v3 Subject Alternative Name: {‘othername’: [‘’],<br />
‘DNS’: [‘www.example.com’]}<br />
* OCSP Stapling :<br />
Server did not send back an OCSP response.<br />
* Session Resumption :<br />
With Session IDs: Supported (5 successful, 0 failed, 0<br />
errors, 5 total attempts).<br />
With TLS Session Tickets: Supported<br />
* SSLV2 Cipher Suites :<br />
Rejected Cipher Suite(s): Hidden<br />
Preferred Cipher Suite: None<br />
Accepted Cipher Suite(s): None<br />
Undefined - An unexpected error happened: None<br />
* SSLV3 Cipher Suites :<br />
Rejected Cipher Suite(s): Hidden<br />
Preferred Cipher Suite:<br />
RC4-SHA 128 bits HTTP 200 OK<br />
Accepted Cipher Suite(s):<br />
CAMELLIA256-SHA 256 bits HTTP 200 OK<br />
RC4-SHA 128 bits HTTP 200 OK<br />
CAMELLIA128-SHA 128 bits HTTP 200 OK<br />
Undefined - An unexpected error happened: None<br />
* TLSV1_1 Cipher Suites :<br />
Rejected Cipher Suite(s): Hidden<br />
Preferred Cipher Suite:<br />
RC4-SHA 128 bits Timeout on HTTP GET<br />
Accepted Cipher Suite(s):<br />
CAMELLIA256-SHA 256 bits HTTP 200 OK<br />
RC4-SHA 128 bits HTTP 200 OK<br />
CAMELLIA128-SHA 128 bits HTTP 200 OK<br />
Undefined - An unexpected error happened:<br />
ADH-CAMELLIA256-SHA socket.timeout - timed out<br />
SCAN COMPLETED IN 9.68 S<br />
------------------------<br />
Example 7. Testing SSL/TLS with testssl.sh<br />
Testssl.sh [38] is a Linux shell script which provides clear output to<br />
facilitate good decision making. It can not only check web servers<br />
but also services on other ports, supports STARTTLS, SNI, SPDY and<br />
does a few check on the HTTP header as well.<br />
It’s a very easy to use tool. Here’s some sample output (without colors):<br />
user@myhost: % testssl.sh owasp.org<br />
##############################################<br />
##########<br />
testssl.sh v2.0rc3 (https:/testssl.sh)<br />
($Id: testssl.sh,v 1.97 2014/04/15 21:54:29 dirkw Exp $)<br />
This program is free software. Redistribution +<br />
modification under GPLv2 is permitted.<br />
USAGE w/o ANY WARRANTY. USE IT AT YOUR OWN RISK!<br />
Note you can only check the server against what is<br />
available (ciphers/protocols) locally on your machine<br />
##############################################<br />
##########<br />
Using “OpenSSL 1.0.2-beta1 24 Feb 2014” on<br />
“myhost://bin/openssl64”<br />
Testing now (2014-04-17 15:06) ---> owasp.org:443 Testing Protocols<br />
SSLv2<br />
SSLv3<br />
TLSv1<br />
NOT offered (ok)<br />
offered<br />
offered (ok)