ADMIN
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Nuts and Bolts<br />
PAM and Hardware<br />
Next, you still need to add the PAM<br />
pam_pkcs11 library to the correct<br />
PAM configuration file – that is, /etc/<br />
pam.d/login or /etc/pam.d/gdm. You<br />
can edit the file manually or use the<br />
system‐config‐authentication tool<br />
referred to previously.<br />
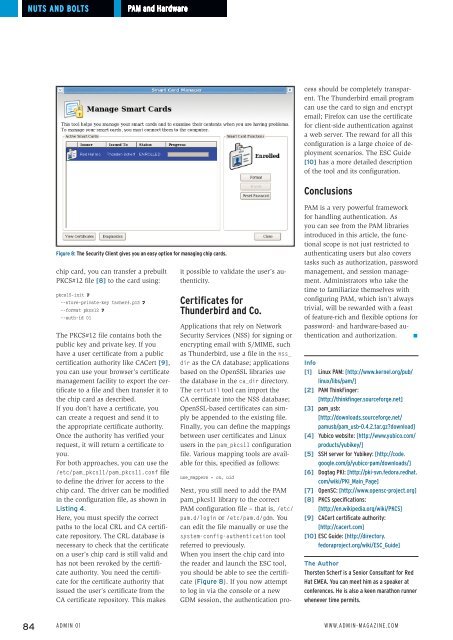
When you insert the chip card into<br />
the reader and launch the ESC tool,<br />
you should be able to see the certificate<br />
(Figure 8). If you now attempt<br />
to log in via the console or a new<br />
GDM session, the authentication process<br />
should be completely transparent.<br />
The Thunderbird email program<br />
can use the card to sign and encrypt<br />
email; Firefox can use the certificate<br />
for client-side authentication against<br />
a web server. The reward for all this<br />
configuration is a large choice of deployment<br />
scenarios. The ESC Guide<br />
[10] has a more detailed description<br />
of the tool and its configuration.<br />
Conclusions<br />
Figure 8: The Security Client gives you an easy option for managing chip cards.<br />
chip card, you can transfer a prebuilt<br />
PKCS#12 file [8] to the card using:<br />
pkcs15‐init U<br />
‐‐store‐private‐key tscherf.p12 U<br />
‐‐format pkcs12 U<br />
‐‐auth‐id 01<br />
The PKCS#12 file contains both the<br />
public key and private key. If you<br />
have a user certificate from a public<br />
certification authority like CACert [9],<br />
you can use your browser’s certificate<br />
management facility to export the certificate<br />
to a file and then transfer it to<br />
the chip card as described.<br />
If you don’t have a certificate, you<br />
can create a request and send it to<br />
the appropriate certificate authority.<br />
Once the authority has verified your<br />
request, it will return a certificate to<br />
you.<br />
For both approaches, you can use the<br />
/etc/pam_pkcs11/pam_pkcs11.conf file<br />
to define the driver for access to the<br />
chip card. The driver can be modified<br />
in the configuration file, as shown in<br />
Listing 4.<br />
Here, you must specify the correct<br />
paths to the local CRL and CA certificate<br />
repository. The CRL database is<br />
necessary to check that the certificate<br />
on a user’s chip card is still valid and<br />
has not been revoked by the certificate<br />
authority. You need the certificate<br />
for the certificate authority that<br />
issued the user’s certificate from the<br />
CA certificate repository. This makes<br />
it possible to validate the user’s authenticity.<br />
Certificates for<br />
Thunderbird and Co.<br />
Applications that rely on Network<br />
Security Services (NSS) for signing or<br />
encrypting email with S/MIME, such<br />
as Thunderbird, use a file in the nss_<br />
dir as the CA database; applications<br />
based on the OpenSSL libraries use<br />
the database in the ca_dir directory.<br />
The certutil tool can import the<br />
CA certificate into the NSS database;<br />
OpenSSL-based certificates can simply<br />
be appended to the existing file.<br />
Finally, you can define the mappings<br />
between user certificates and Linux<br />
users in the pam_pkcs11 configuration<br />
file. Various mapping tools are available<br />
for this, specified as follows:<br />
use_mappers = cn, uid<br />
PAM is a very powerful framework<br />
for handling authentication. As<br />
you can see from the PAM libraries<br />
introduced in this article, the functional<br />
scope is not just restricted to<br />
authenticating users but also covers<br />
tasks such as authorization, password<br />
management, and session management.<br />
Administrators who take the<br />
time to familiarize themselves with<br />
configuring PAM, which isn’t always<br />
trivial, will be rewarded with a feast<br />
of feature-rich and flexible options for<br />
password- and hardware-based authentication<br />
and authorization. n<br />
Info<br />
[1] Linux PAM: [http:// www. kernel. org/ pub/<br />
linux/ libs/ pam/]<br />
[2] PAM ThinkFinger:<br />
[http:// thinkfinger. sourceforge. net]<br />
[3] pam_usb:<br />
[http:// downloads. sourceforge. net/<br />
pamusb/ pam_usb‐0. 4. 2. tar. gz? download]<br />
[4] Yubico website: [http:// www. yubico. com/<br />
products/ yubikey/]<br />
[5] SSH server for Yubikey: [http:// code.<br />
google. com/ p/ yubico‐pam/ downloads/]<br />
[6] Dogtag PKI: [http:// pki‐svn. fedora. redhat.<br />
com/ wiki/ PKI_Main_Page]<br />
[7] OpenSC: [http:// www. opensc‐project. org]<br />
[8] PKCS specifications:<br />
[http:// en. wikipedia. org/ wiki/ PKCS]<br />
[9] CACert certificate authority:<br />
[http:// cacert. com]<br />
[10] ESC Guide: [http:// directory.<br />
fedoraproject. org/ wiki/ ESC_Guide]<br />
The Author<br />
Thorsten Scherf is a Senior Consultant for Red<br />
Hat EMEA. You can meet him as a speaker at<br />
conferences. He is also a keen marathon runner<br />
whenever time permits.<br />
84 Admin 01 www.admin-magazine.com