ADMIN
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Nuts and bolts<br />
ModSecurity<br />
<br />
SecRule &ARGS "!@eq 1"<br />
SecRule ARGS_NAMES "!^statid$"<br />
SecRule ARGS:statID "!^\d{1,3}$"<br />
<br />
Three lines embedded in an Apache<br />
location container state that valid<br />
user requests for the statements_<br />
full.asp file are only allowed to<br />
have one argument (first rule) called<br />
statid (second rule) with numbers<br />
of one to three digits (third rule) as<br />
their parameters. Any requests that<br />
do not follow this pattern are cleaned<br />
up by the default action, as defined in<br />
SecDefaultAction. This would effectively<br />
prevent an attacker exploiting<br />
the SQL injection vulnerability.<br />
No Inside Information<br />
ModSecurity also filters outgoing<br />
data, especially server responses to<br />
incoming requests. The PHP programming<br />
language throws error messages<br />
such as this:<br />
Fatal error: Connecting to MySQL server<br />
'dbserv.example.com' failed<br />
Although you can disable PHP error<br />
messages in responses, Google still<br />
lists a bunch of websites where PHP<br />
error messages reveal many juicy details<br />
of applications. This information<br />
is very useful to an attacker, because<br />
it can help them understand the internal<br />
workings and structure of a web<br />
application and attack it in a more<br />
targeted way. To tell ModSecurity to<br />
catch PHP error messages and prevent<br />
them from being sent to users,<br />
you can define a rule like this:<br />
SecRule RESPONSE_BODY "Fatal error:"<br />
RESPONSE_BODY refers to the content<br />
of the server response to the client,<br />
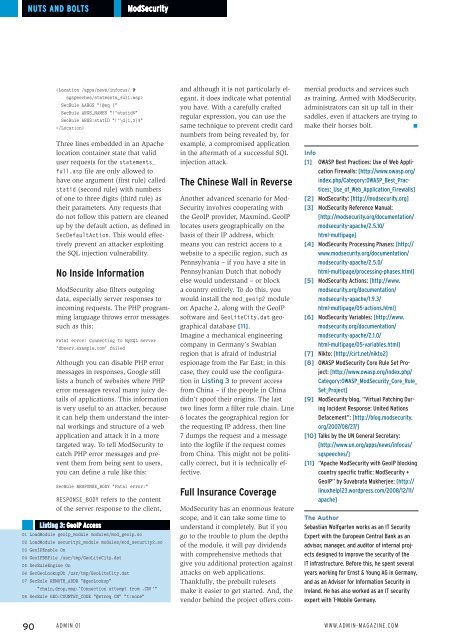
Listing 3: GeoIP Access<br />
01 LoadModule geoip_module modules/mod_geoip.so<br />
02 LoadModule security2_module modules/mod_security2.so<br />
03 GeoIPEnable On<br />
04 GeoIPDBFile /usr/tmp/GeoLiteCity.dat<br />
05 SecRuleEngine On<br />
06 SecGeoLookupDb /usr/tmp/GeoLiteCity.dat<br />
07 SecRule REMOTE_ADDR "@geoLookup"<br />
"chain,drop,msg:'Connection attempt from .CN!'"<br />
08 SecRule GEO:COUNTRY_CODE "@streq CN" "t:none"<br />
and although it is not particularly elegant,<br />
it does indicate what potential<br />
you have. With a carefully crafted<br />
regular expression, you can use the<br />
same technique to prevent credit card<br />
numbers from being revealed by, for<br />
example, a compromised application<br />
in the aftermath of a successful SQL<br />
injection attack.<br />
The Chinese Wall in Reverse<br />
Another advanced scenario for Mod-<br />
Security involves cooperating with<br />
the GeoIP provider, Maxmind. GeoIP<br />
locates users geographically on the<br />
basis of their IP address, which<br />
means you can restrict access to a<br />
website to a specific region, such as<br />
Pennsylvania – if you have a site in<br />
Pennsylvanian Dutch that nobody<br />
else would understand – or block<br />
a country entirely. To do this, you<br />
would install the mod_geoip2 module<br />
on Apache 2, along with the GeoIP<br />
software and GeoLiteCity.dat geographical<br />
database [11].<br />
Imagine a mechanical engineering<br />
company in Germany’s Swabian<br />
region that is afraid of industrial<br />
espionage from the Far East; in this<br />
case, they could use the configuration<br />
in Listing 3 to prevent access<br />
from China – if the people in China<br />
didn’t spoof their origins. The last<br />
two lines form a filter rule chain. Line<br />
6 locates the geographical region for<br />
the requesting IP address, then line<br />
7 dumps the request and a message<br />
into the logfile if the request comes<br />
from China. This might not be politically<br />
correct, but it is technically effective.<br />
Full Insurance Coverage<br />
ModSecurity has an enormous feature<br />
scope, and it can take some time to<br />
understand it completely. But if you<br />
go to the trouble to plum the depths<br />
of the module, it will pay dividends<br />
with comprehensive methods that<br />
give you additional protection against<br />
attacks on web applications.<br />
Thankfully, the prebuilt rulesets<br />
make it easier to get started. And, the<br />
vendor behind the project offers commercial<br />
products and services such<br />
as training. Armed with ModSecurity,<br />
administrators can sit up tall in their<br />
saddles, even if attackers are trying to<br />
make their horses bolt.<br />
n<br />
Info<br />
[1] OWASP Best Practices: Use of Web Application<br />
Firewalls: [http:// www. owasp. org/<br />
index. php/ Category:OWASP_Best_Practices:_Use_of_Web_Application_Firewalls]<br />
[2] ModSecurity: [http:// modsecurity. org]<br />
[3] ModSecurity Reference Manual:<br />
[http:// modsecurity. org/ documentation/<br />
modsecurity‐apache/ 2. 5. 10/<br />
html‐multipage]<br />
[4] ModSecurity Processing Phases: [http://<br />
www. modsecurity. org/ documentation/<br />
modsecurity‐apache/ 2. 5. 0/<br />
html‐multipage/ processing‐phases. html]<br />
[5] ModSecurity Actions: [http:// www.<br />
modsecurity. org/ documentation/<br />
modsecurity‐apache/ 1. 9. 3/<br />
html‐multipage/ 05‐actions. html]<br />
[6] ModSecurity Variables: [http:// www.<br />
modsecurity. org/ documentation/<br />
modsecurity‐apache/ 2. 1. 0/<br />
html‐multipage/ 05‐variables. html]<br />
[7] Nikto: [http:// cirt. net/ nikto2]<br />
[8] OWASP ModSecurity Core Rule Set Project:<br />
[http:// www. owasp. org/ index. php/<br />
Category:OWASP_ModSecurity_Core_Rule_<br />
Set_Project]<br />
[9] ModSecurity blog, “Virtual Patching During<br />
Incident Response: United Nations<br />
Defacement”: [http:// blog. modsecurity.<br />
org/ 2007/ 08/ 27/]<br />
[10] Talks by the UN General Secretary:<br />
[http:// www. un. org/ apps/ news/ infocus/<br />
sgspeeches/]<br />
[11] “Apache ModSecurity with GeoIP blocking<br />
country specific traffic: ModSecurity +<br />
GeoIP” by Suvabrata Mukherjee: [http://<br />
linuxhelp123. wordpress. com/ 2008/ 12/ 11/<br />
apache]<br />
The Author<br />
Sebastian Wolfgarten works as an IT Security<br />
Expert with the European Central Bank as an<br />
advisor, manager, and auditor of internal projects<br />
designed to improve the security of the<br />
IT infrastructure. Before this, he spent several<br />
years working for Ernst & Young AG in Germany,<br />
and as an Advisor for Information Security in<br />
Ireland. He has also worked as an IT security<br />
expert with T-Mobile Germany.<br />
90 Admin 01 www.admin-magazine.com