ADMIN
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
VPns with SSTP<br />
nuTS And BoLTS<br />
Handshake<br />
Microsoft’s SSTP is basically another proprietary implementation of an<br />
SSL VPN. SSTP relies on standards such as SSL and TLS for encryption<br />
and authentication, but Microsoft has modified the tried-and-trusted<br />
SSL handshake by introducing proprietary extensions that bind the proprietary<br />
PPP protocol. If you look at the basic handshake, SSTP at first<br />
keeps to the standard SSL handshake procedure:<br />
1. The client opens a connection to TCP port 443 on the server.<br />
2. The client sends an “SSL Session Setup Message” to indicate that it<br />
wants to set up an SSL connection to the server.<br />
3. The server sends an SSL certificate to the client.<br />
4. The client validates the server certificate, identifies the correct encryption<br />
method for the SSL session, and creates a session key, which it<br />
encrypts using the public key from the server certificate.<br />
5. The client sends the encrypted SSL session key to the server.<br />
6. The server decrypts the client’s SSL session key using its own private<br />
key and encrypts the communications with the session key. Up to this<br />
point, the procedure is no different from standard SSL communication.<br />
However, Microsoft then implements additional handshake steps that<br />
build on what has happened thus far.<br />
7. The client sends an HTTP-over-SSL request message to the server and<br />
negotiates an SSTP tunnel with the server.<br />
8. After this, the client negotiates a PPP connection with the SSTP<br />
server, which includes authenticating the user’s login credentials with<br />
a PPP authentication method and configuring the settings for the data<br />
traffic.<br />
9. The client starts to transfer data via the PPP connection.<br />
L2TP, or PPTP, but use SSL to handle<br />
the data transfer. Because SSTP encapsulates<br />
complete IP packets, the<br />
connections act just like a PPTP or<br />
IPsec tunnel on the client side. According<br />
to the Microsoft definition,<br />
SSTP is a protocol mainly intended<br />
for dialup connections in the application<br />
layer that guarantees the confidentiality,<br />
authenticity, and integrity<br />
of the data to be transferred. A public<br />
key infrastructure (PKI) is used for<br />
authentication purposes. Microsoft introduced<br />
SSTP with Windows Server<br />
2008 and Vista SP1. Today, Windows<br />
Server 2008 R2 and Windows 7 also<br />
support SSTP [1]. But what does SSTP<br />
offer the administrator, and how do<br />
you set up a VPN server with SSTP?<br />
Sample Scenario<br />
In this example, I am using Windows<br />
Server 2008 R2 to provide an SSTPbased<br />
VPN server behind a NAT<br />
device. The server is configured as<br />
the domain controller and needs two<br />
network cards for the VPN setup. At<br />
least one card (preferably both) needs<br />
a static IP address. The client will be<br />
MS Windows 7.<br />
The server and clients are both members<br />
of an Active Directory (AD)<br />
domain. Additionally, the server and<br />
clients should have all the current<br />
updates in place, such as the current<br />
Service Pack 2 for Windows Server<br />
2008 R2. After installing a Windows<br />
server, you need to install the Active<br />
Directory Domain Services to<br />
make the server a domain controller.<br />
The easiest way to do this is to run<br />
dcpromo at the command line and<br />
then follow the wizard.<br />
The server also needs to provide<br />
DNS, DHCP, and certificate services,<br />
which you can achieve by configuring<br />
the matching server roles in the role<br />
wizard. VPN functionality is also provided<br />
via a server role Network policy<br />
and access services.<br />
PKI<br />
Because SSTP uses HTTPS (port 443)<br />
to handle all the data traffic, there is<br />
no alternative to configuring a public<br />
key infrastructure. At a minimum,<br />
this means installing at least one certificate<br />
on the SSTP server and a root<br />
certificate authority certificate on all<br />
SSTP VPN clients. You might have<br />
to modify the packet filter rules, too,<br />
even though SSTP doesn’t actually<br />
need any additional NAT configuration<br />
because port 443 is typically<br />
open. The “Port Customizer” box explains<br />
how you can use a port other<br />
than 443 for SSTP.<br />
Next, you’ll need to configure an<br />
Active Directory-integrated root certification<br />
authority on the domain controller.<br />
In combination with a group<br />
policy, this causes clients that are domain<br />
members to request certificates<br />
automatically when they open a connection.<br />
Certificates are then issued<br />
Port customizer<br />
SSTP normally uses TCP port 443, which is<br />
open in most router and NAT configurations.<br />
Security-conscious Windows administrators<br />
might prefer to modify the standard port<br />
used by SSTP. To do so, you need to edit the<br />
following registry key<br />
HKEY_LOCAL_MACHINE\SYSTEM\ U<br />
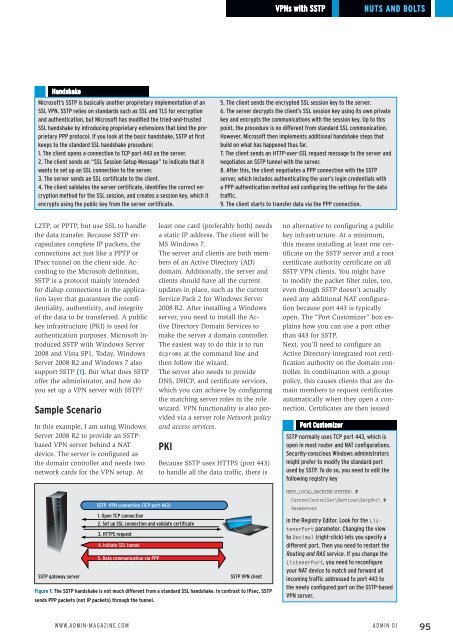
SSTP gateway server<br />
SSTP VPN connection (TCP port 443)<br />
1. Open TCP connection<br />
2. Set up SSL connection and validate certificate<br />
3. HTTPS request<br />
4. Initiate SSL tunnel<br />
5. Data communication via PPP<br />
SSTP VPN client<br />
Figure 1: The SSTP handshake is not much different from a standard SSL handshake. In contrast to IPsec, SSTP<br />
sends PPP packets (not IP packets) through the tunnel.<br />
CurrentControlSet\Services\SstpSvc\ U<br />
Parameters<br />
in the Registry Editor. Look for the ListenerPort<br />
parameter. Changing the view<br />
to Decimal (right-click) lets you specify a<br />
different port. Then you need to restart the<br />
Routing and RAS service. If you change the<br />
ListenerPort, you need to reconfigure<br />
your NAT device to match and forward all<br />
incoming traffic addressed to port 443 to<br />
the newly configured port on the SSTP-based<br />
VPN server.<br />
www.Admin-mAgAzine.com<br />
Admin 01<br />
95