ADMIN
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Nuts and bolts<br />
ModSecurity<br />
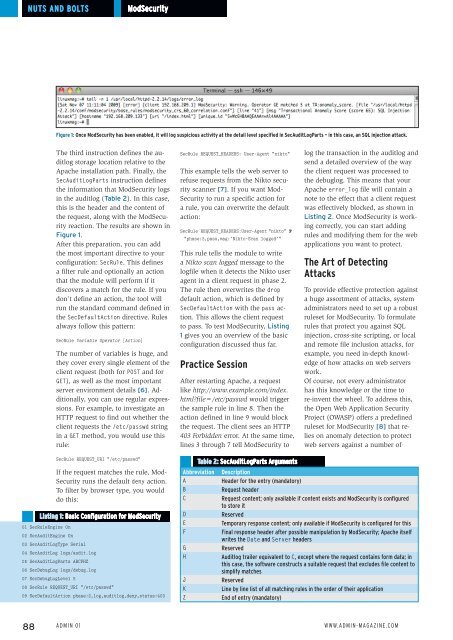
Figure 1: Once ModSecurity has been enabled, it will log suspicious activity at the detail level specified in SecAuditLogParts – in this case, an SQL injection attack.<br />
The third instruction defines the auditlog<br />
storage location relative to the<br />
Apache installation path. Finally, the<br />
SecAuditLogParts instruction defines<br />
the information that ModSecurity logs<br />
in the auditlog (Table 2). In this case,<br />
this is the header and the content of<br />
the request, along with the ModSecurity<br />
reaction. The results are shown in<br />
Figure 1.<br />
After this preparation, you can add<br />
the most important directive to your<br />
configuration: SecRule. This defines<br />
a filter rule and optionally an action<br />
that the module will perform if it<br />
discovers a match for the rule. If you<br />
don’t define an action, the tool will<br />
run the standard command defined in<br />
the SecDefaultAction directive. Rules<br />
always follow this pattern:<br />
SecRule Variable Operator [Action]<br />
The number of variables is huge, and<br />
they cover every single element of the<br />
client request (both for POST and for<br />
GET), as well as the most important<br />
server environment details [6]. Additionally,<br />
you can use regular expressions.<br />
For example, to investigate an<br />
HTTP request to find out whether the<br />
client requests the /etc/passwd string<br />
in a GET method, you would use this<br />
rule:<br />
SecRule REQUEST_HEADERS: User‐Agent "nikto"<br />
This example tells the web server to<br />
refuse requests from the Nikto security<br />
scanner [7]. If you want Mod-<br />
Security to run a specific action for<br />
a rule, you can overwrite the default<br />
action:<br />
SecRule REQUEST_HEADERS:User‐Agent "nikto" U<br />
"phase:2,pass,msg:'Nikto‐Scan logged'"<br />
This rule tells the module to write<br />
a Nikto scan logged message to the<br />
logfile when it detects the Nikto user<br />
agent in a client request in phase 2.<br />
The rule then overwrites the drop<br />
default action, which is defined by<br />
SecDefaultAction with the pass action.<br />
This allows the client request<br />
to pass. To test ModSecurity, Listing<br />
1 gives you an overview of the basic<br />
configuration discussed thus far.<br />
Practice Session<br />
After restarting Apache, a request<br />
like http://www.example.com/index.<br />
html?file=/etc/passwd would trigger<br />
the sample rule in line 8. Then the<br />
action defined in line 9 would block<br />
the request. The client sees an HTTP<br />
403 Forbidden error. At the same time,<br />
lines 3 through 7 tell ModSecurity to<br />
log the transaction in the auditlog and<br />
send a detailed overview of the way<br />
the client request was processed to<br />
the debuglog. This means that your<br />
Apache error_log file will contain a<br />
note to the effect that a client request<br />
was effectively blocked, as shown in<br />
Listing 2. Once ModSecurity is working<br />
correctly, you can start adding<br />
rules and modifying them for the web<br />
applications you want to protect.<br />
The Art of Detecting<br />
Attacks<br />
To provide effective protection against<br />
a huge assortment of attacks, system<br />
administrators need to set up a robust<br />
ruleset for ModSecurity. To formulate<br />
rules that protect you against SQL<br />
injection, cross-site scripting, or local<br />
and remote file inclusion attacks, for<br />
example, you need in-depth knowledge<br />
of how attacks on web servers<br />
work.<br />
Of course, not every administrator<br />
has this knowledge or the time to<br />
re-invent the wheel. To address this,<br />
the Open Web Application Security<br />
Project (OWASP) offers a predefined<br />
ruleset for ModSecurity [8] that relies<br />
on anomaly detection to protect<br />
web servers against a number of<br />
SecRule REQUEST_URI "/etc/passwd"<br />
If the request matches the rule, Mod-<br />
Security runs the default deny action.<br />
To filter by browser type, you would<br />
do this:<br />
Listing 1: Basic Configuration for ModSecurity<br />
01 SecRuleEngine On<br />
02 SecAuditEngine On<br />
03 SecAuditLogType Serial<br />
04 SecAuditLog logs/audit.log<br />
05 SecAuditLogParts ABCFHZ<br />
06 SecDebugLog logs/debug.log<br />
07 SecDebugLogLevel 5<br />
08 SecRule REQUEST_URI "/etc/passwd"<br />
09 SecDefaultAction phase:2,log,auditlog,deny,status:403<br />
Table 2: SecAuditLogParts Arguments<br />
Abbreviation<br />
A<br />
B<br />
C<br />
D<br />
E<br />
F<br />
G<br />
H<br />
J<br />
K<br />
Z<br />
Description<br />
Header for the entry (mandatory)<br />
Request header<br />
Request content; only available if content exists and ModSecurity is configured<br />
to store it<br />
Reserved<br />
Temporary response content; only available if ModSecurity is configured for this<br />
Final response header after possible manipulation by ModSecurity; Apache itself<br />
writes the Date and Server headers<br />
Reserved<br />
Auditlog trailer equivalent to C, except where the request contains form data; in<br />
this case, the software constructs a suitable request that excludes file content to<br />
simplify matches<br />
Reserved<br />
Line by line list of all matching rules in the order of their application<br />
End of entry (mandatory)<br />
88 Admin 01 www.admin-magazine.com