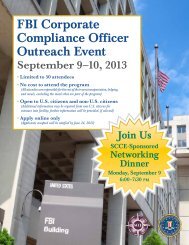
FeatureCompanies also need to be alert to therisks <strong>of</strong> money laundering through gift <strong>and</strong>stored-value cards. Increasingly, explainedDouglas Leff, Supervisory Special Agent inthe Asset Forfeiture & Money LaunderingUnit, criminals are taking advantage <strong>of</strong>this virtually untraceable means <strong>of</strong> movingmoney. Companies, particularly retailers,need to be wary <strong>of</strong> unusually high volumes<strong>of</strong> transactions using these instruments.Businesses may also want to consider monitoringemployee expenses which reflectgift card purchases. These purchases maybe innocent, but they may be an indicator<strong>of</strong> a Foreign Corrupt Practices Act(FCPA) violation.every three months, making it difficult toprove who the sender <strong>of</strong> an email was.He also warned companies to be aware <strong>of</strong>the risks <strong>of</strong> cloud computing. The distributedstorage model makes it much more difficultfor law enforcement to identify a criminalafter an intrusion.The day ended with a heated discussion<strong>of</strong> the FCPA. It featured a panel consisting <strong>of</strong>Paula Ebersole, Supervisory Special Agent<strong>of</strong> the FBI’s Washington Field Office; ChrisFavro, a retired FBI agent <strong>and</strong> now SeniorCounsel, <strong>Compliance</strong> <strong>and</strong> Business Conductfor 3M; <strong>and</strong> Charles Duross, Assistant Chief <strong>of</strong>the US Department <strong>of</strong> Justice’s Fraud Section.The conversation included a discussion <strong>of</strong> thedesire <strong>of</strong> the <strong>Compliance</strong> community for theDepartment <strong>of</strong> Justice to provide more informationabout how companies can earn creditfor their compliance programs.Roy Snell, CEO <strong>of</strong> SCCE <strong>and</strong> the HealthCare <strong>Compliance</strong> Association, pointed out,“This is exactly the kind <strong>of</strong> data we need todemonstrate to CEOs <strong>and</strong> boards the valuethat compliance programs can bring to theirorganizations.”<strong>Compliance</strong> & <strong>Ethics</strong> Pr<strong>of</strong>essional May/June 2012Another emerging risk area is socialmedia. Michael Kolessar, Supervisory SpecialAgent in the Cyber Unit, reported an increasein incidents <strong>of</strong> extortion using social media.He recounted a case in which a disaffectedcustomer threatened to unleash a torrent <strong>of</strong>online complaints about a company unlessit agreed to his dem<strong>and</strong>s. Kolessar urgedcompanies to report these dem<strong>and</strong>s to lawenforcement promptly while the data is readilyaccessible. Contrary to the belief that digitalcommunications last forever, he explained thatmany Internet providers purge their recordsDay Two <strong>of</strong> the program took place at theFBI’s training facility in Quantico, Virginia.The tour included the Memorial Wall, whichhonors agents killed in the line <strong>of</strong> duty, <strong>and</strong>famed Hogan’s Alley, a few Hollywood-builtcity blocks designed to give agents the opportunityto train in “real life” settings.The training in enforcement for recruitsalso includes 40 hours <strong>of</strong> legal education,the group learned. Lisa Baker, Chief <strong>of</strong> theLegal Instruction Unit, shared a portion <strong>of</strong>the training on the protection <strong>of</strong> civil rights.This program helps recruits underst<strong>and</strong> thesource <strong>of</strong> their authority, as well as the limits<strong>of</strong> it, <strong>and</strong> the value <strong>of</strong> adhering to thoselimits. This portion <strong>of</strong> the training beginswith the U.S. Constitution <strong>and</strong> Bill <strong>of</strong> Rights,16 www.corporatecompliance.org +1 952 933 4977 or 888 277 4977
Featurea copy <strong>of</strong> which is provided to each recruit.To drive the lessons home, the trainingincludes examples <strong>of</strong> the risks that can occurwhen those Constitutional boundaries arebreached.COINTELPRO, a program from severaldecades ago that monitored people the FBIhad deemed a potential threat to the nation,is one <strong>of</strong> the incidents studies. This programonce included a list <strong>of</strong> more than 26,000Americans to be “rounded up” in case <strong>of</strong>a national emergency. The investigation <strong>of</strong>COINTELPRO led to significant changeswithin the FBI, including a set <strong>of</strong> guidelinesfor the FBI that would form the basis <strong>of</strong> itscompliance program.Baker explained that the policy environmentfor domestic operations is now basedon the Constitution, federal statutes, <strong>and</strong>Executive Orders, plus the Attorney GeneralGuidelines, the FBI Domestic Investigation<strong>and</strong> Operational Guide, as well as BureauProgram Policy Implementation Guides.Together these are used to direct the FBI’soperations <strong>and</strong> ensure they comply with thelaw <strong>and</strong> the Bureau’s own st<strong>and</strong>ards.In addition, the FBI operates under aset <strong>of</strong> core values, Patrick Kelley explained.These are:··Rigorous obedience to the Constitution <strong>of</strong>the United States··Respect for the dignity <strong>of</strong> all thosewe protect··Compassion··Fairness··Uncompromising personal <strong>and</strong>institutional integrity··Accountability by accepting responsibilityfor our actions <strong>and</strong> decisions <strong>and</strong> theirconsequences··Leadership, by example, both personal<strong>and</strong> pr<strong>of</strong>essionalThese values help define how the FBIviews itself. For example, according to theFBI’s internal ethics manual: “It is our policyto comply fully with all laws, regulations,<strong>and</strong> rules governing our operations, programs<strong>and</strong> activities…Public service is apublic trust. Those <strong>of</strong> us lucky enough toserve the public in <strong>and</strong> through this greatorganization must adhere to that principle ineverything we do.”The day concluded with a fascinating <strong>and</strong>fun peek into how agents are trained to takethose values <strong>and</strong> the law, <strong>and</strong> apply themwhen facing a scenario in which deadly forcemay be used.<strong>Compliance</strong> & <strong>Ethics</strong> Pr<strong>of</strong>essional May/June 2012+1 952 933 4977 or 888 277 4977 | www.corporatecompliance.org 17