2016–2017 2016–2017
2016-2017-graduate-catalog
2016-2017-graduate-catalog
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
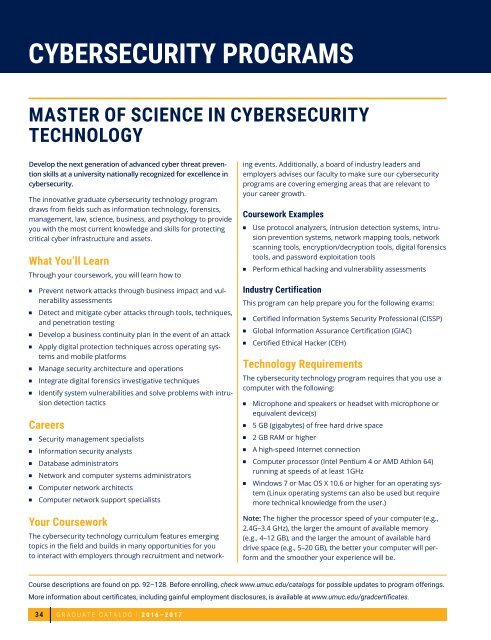
CYBERSECURITY PROGRAMS<br />
MASTER OF SCIENCE IN CYBERSECURITY<br />
TECHNOLOGY<br />
Develop the next generation of advanced cyber threat prevention<br />
skills at a university nationally recognized for excellence in<br />
cybersecurity.<br />
The innovative graduate cybersecurity technology program<br />
draws from fields such as information technology, forensics,<br />
management, law, science, business, and psychology to provide<br />
you with the most current knowledge and skills for protecting<br />
critical cyber infrastructure and assets.<br />
What You’ll Learn<br />
Through your coursework, you will learn how to<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
Prevent network attacks through business impact and vulnerability<br />
assessments<br />
Detect and mitigate cyber attacks through tools, techniques,<br />
and penetration testing<br />
Develop a business continuity plan in the event of an attack<br />
Apply digital protection techniques across operating systems<br />
and mobile platforms<br />
Manage security architecture and operations<br />
Integrate digital forensics investigative techniques<br />
Identify system vulnerabilities and solve problems with intrusion<br />
detection tactics<br />
Careers<br />
<br />
<br />
<br />
<br />
<br />
<br />
Security management specialists<br />
Information security analysts<br />
Database administrators<br />
Network and computer systems administrators<br />
Computer network architects<br />
Computer network support specialists<br />
The cybersecurity technology curriculum features emerging<br />
topics in the field and builds in many opportunities for you<br />
to interact with employers through recruitment and networking<br />
events. Additionally, a board of industry leaders and<br />
employers advises our faculty to make sure our cybersecurity<br />
programs are covering emerging areas that are relevant to<br />
your career growth.<br />
Coursework Examples<br />
<br />
<br />
Use protocol analyzers, intrusion detection systems, intrusion<br />
prevention systems, network mapping tools, network<br />
scanning tools, encryption/decryption tools, digital forensics<br />
tools, and password exploitation tools<br />
Perform ethical hacking and vulnerability assessments<br />
Industry Certification<br />
This program can help prepare you for the following exams:<br />
<br />
<br />
<br />
Certified Information Systems Security Professional (CISSP)<br />
Global Information Assurance Certification (GIAC)<br />
Certified Ethical Hacker (CEH)<br />
Technology Requirements<br />
The cybersecurity technology program requires that you use a<br />
computer with the following:<br />
<br />
<br />
<br />
<br />
Microphone and speakers or headset with microphone or<br />
equivalent device(s)<br />
5 GB (gigabytes) of free hard drive space<br />
2 GB RAM or higher<br />
A high-speed Internet connection<br />
<br />
Computer processor (Intel Pentium 4 or AMD Athlon 64)<br />
running at speeds of at least 1GHz<br />
<br />
Windows 7 or Mac OS X 10.6 or higher for an operating system<br />
(Linux operating systems can also be used but require<br />
more technical knowledge from the user.)<br />
Your Coursework<br />
Note: The higher the processor speed of your computer (e.g.,<br />
2.4G–3.4 GHz), the larger the amount of available memory<br />
(e.g., 4–12 GB), and the larger the amount of available hard<br />
drive space (e.g., 5–20 GB), the better your computer will perform<br />
and the smoother your experience will be.<br />
Course descriptions are found on pp. 92–128. Before enrolling, check www.umuc.edu/catalogs for possible updates to program offerings.<br />
More information about certificates, including gainful employment disclosures, is available at <br />
34<br />
GRADUATE CATALOG | <strong>2016–2017</strong>