You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
@<strong>PC</strong>PRO<br />
FACEBOOK.COM/<strong>PC</strong>PRO<br />
get interesting. Your PIN<br />
code must be at least<br />
seven digits, and can<br />
stretch to 15. You can’t<br />
use sequential numbering<br />
for your code or all<br />
repeating numbers, for<br />
that matter. I’d change<br />
the factory default admin<br />
PIN of 11223344 sharpish,<br />
though; that’s just asking<br />
for trouble!<br />
That aside, rather than<br />
be restricted to 0 to 9, the<br />
Shift key when used in<br />
conjunction with any<br />
number registers that as<br />
a separate value, making<br />
guessing a PIN much<br />
harder. Guessing isn’t a<br />
good idea anyway, as a<br />
total of 15 wrong attempts kicks the<br />
drive into self-destruct mode.<br />
Actually, it’s better than that<br />
sounds. The 15 attempts are split<br />
into three groups of five under a<br />
brute-force protection umbrella. Five<br />
wrong guesses and the drive freezes,<br />
requiring physical reconnection<br />
before the next five goes are allowed.<br />
Get them wrong and it freezes again,<br />
but this time requires some Shift key<br />
jiggery-pokery while plugging it back<br />
in and a special code entering before<br />
offering one last batch of guesses. If<br />
those fail then the admin user PINs are<br />
reset and the encryption keys deleted,<br />
along with the data upon it. There’s<br />
also an admin self-destruct option<br />
that does the same thing, but using a<br />
data-exploding PIN code for want of<br />
a better term. That same PIN is then<br />
used as the new user PIN, and the<br />
drive will need repartitioning and<br />
reformatting to be usable again.<br />
Fine, you say, but what if some<br />
clever tech guys have permanent<br />
physical possession of the drive –<br />
surely that’s game-over for your<br />
data privacy? Usually, I’d agree,<br />
depending upon who is doing the<br />
holding of course. However, even<br />
in this worst-case scenario it isn’t<br />
straightforward to get at the data. I’d<br />
go so far as to say that pretty much all<br />
the access techniques I know about –<br />
including laser attack and fault<br />
injecting, which can compromise<br />
most storage devices – fail here.<br />
External tamper controls are<br />
impressive. In fact, with any attempt<br />
to physically dismantle the device<br />
being met by the internal components<br />
encased in layers of ultra-tough epoxy<br />
resin, it would almost certainly break<br />
those components during the attack<br />
process. This “tamper-evident” design<br />
is important: it’s good to see that<br />
someone has attempted an attack,<br />
even if they’ve failed. The activeshield<br />
violation protection also means<br />
that any attack on the microprocessor<br />
would initiate a deadlock state for<br />
the drive and require a power<br />
cycle to continue. Indeed, all the<br />
authentication parameters are<br />
encrypted and protected by the<br />
microprocessors’ memory encryption<br />
and access control schemes.<br />
You also get protection from<br />
“stupid user syndrome”, whereby<br />
the drive will go into lockdown if left<br />
unattended for a specified period of<br />
time (5 to 99 minutes), requiring PIN<br />
entry to start up again. The drive also<br />
does this when ejected from any host,<br />
or when the lock button is pressed on<br />
the keypad.<br />
Is being ultra-secure worth the<br />
premium that the device costs?<br />
That isn’t easy to answer, and will<br />
depend upon your data protection<br />
and regulatory compliance<br />
requirements. Maybe it’s better put<br />
the other way: can your organisation<br />
afford not to invest in truly secure<br />
data portability technology?<br />
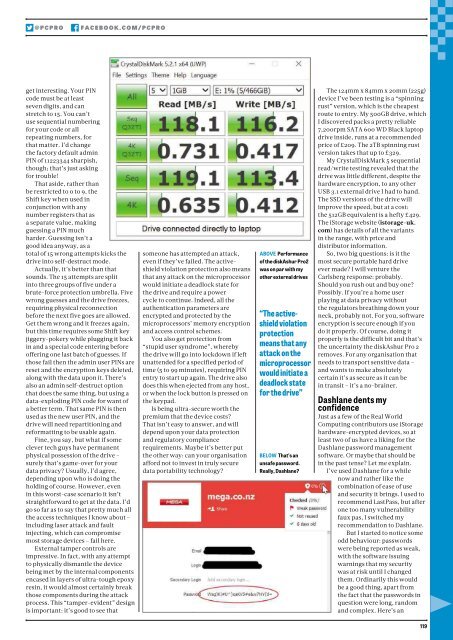
ABOVE Performance<br />
of the diskAshur <strong>Pro</strong>2<br />
was on par with my<br />
other external drives<br />
“The activeshield<br />
violation<br />
protection<br />
means that any<br />
attack on the<br />
microprocessor<br />
would initiate a<br />
deadlock state<br />
for the drive”<br />
BELOW That’s an<br />
unsafe password.<br />
Really, Dashlane?<br />
The 124mm x 84mm x 20mm (225g)<br />
device I’ve been testing is a “spinning<br />
rust” version, which is the cheapest<br />
route to entry. My 500GB drive, which<br />
I discovered packs a pretty reliable<br />
7,200rpm SATA 600 WD Black laptop<br />
drive inside, runs at a recommended<br />
price of £209. The 2TB spinning rust<br />
version takes that up to £329.<br />
My CrystalDiskMark 5 sequential<br />
read/write testing revealed that the<br />
drive was little different, despite the<br />
hardware encryption, to any other<br />
USB 3.1 external drive I had to hand.<br />
The SSD versions of the drive will<br />
improve the speed, but at a cost:<br />
the 512GB equivalent is a hefty £429.<br />
The iStorage website (istorage-uk.<br />
com) has details of all the variants<br />
in the range, with price and<br />
distributor information.<br />
So, two big questions: is it the<br />
most secure portable hard drive<br />
ever made? I will venture the<br />
Carlsberg response: probably.<br />
Should you rush out and buy one?<br />
Possibly. If you’re a home user<br />
playing at data privacy without<br />
the regulators breathing down your<br />
neck, probably not. For you, software<br />
encryption is secure enough if you<br />
do it properly. Of course, doing it<br />
properly is the difficult bit and that’s<br />
the uncertainty the diskAshur <strong>Pro</strong> 2<br />
removes. For any organisation that<br />
needs to transport sensitive data –<br />
and wants to make absolutely<br />
certain it’s as secure as it can be<br />
in transit – it’s a no-brainer.<br />
Dashlane dents my<br />
confidence<br />
Just as a few of the Real World<br />
Computing contributors use iStorage<br />
hardware-encrypted devices, so at<br />
least two of us have a liking for the<br />
Dashlane password management<br />
software. Or maybe that should be<br />
in the past tense? Let me explain.<br />
I’ve used Dashlane for a while<br />
now and rather like the<br />
combination of ease of use<br />
and security it brings. I used to<br />
recommend LastPass, but after<br />
one too many vulnerability<br />
faux pas, I switched my<br />
recommendation to Dashlane.<br />
But I started to notice some<br />
odd behaviour: passwords<br />
were being reported as weak,<br />
with the software issuing<br />
warnings that my security<br />
was at risk until I changed<br />
them. Ordinarily this would<br />
be a good thing, apart from<br />
the fact that the passwords in<br />
question were long, random<br />
and complex. Here’s an<br />
119