You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Expert Opinion | Information Technology<br />
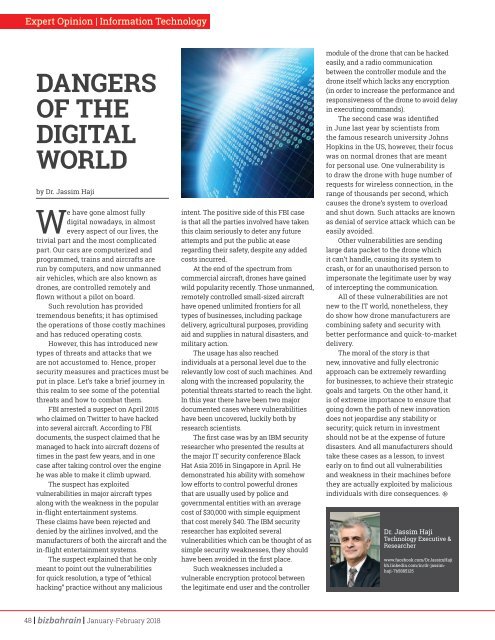
DANGERS<br />
OF THE<br />
DIGITAL<br />
WORLD<br />
by Dr. Jassim Haji<br />
We have gone almost fully<br />
digital nowadays, in almost<br />
every aspect of our lives, the<br />
trivial part and the most complicated<br />
part. Our cars are computerized and<br />
programmed, trains and aircrafts are<br />
run by computers, and now unmanned<br />
air vehicles, which are also known as<br />
drones, are controlled remotely and<br />
flown without a pilot on board.<br />
Such revolution has provided<br />
tremendous benefits; it has optimised<br />
the operations of those costly machines<br />
and has reduced operating costs.<br />
However, this has introduced new<br />
types of threats and attacks that we<br />
are not accustomed to. Hence, proper<br />
security measures and practices must be<br />
put in place. Let’s take a brief journey in<br />
this realm to see some of the potential<br />
threats and how to combat them.<br />
FBI arrested a suspect on April 2015<br />
who claimed on Twitter to have hacked<br />
into several aircraft. According to FBI<br />
documents, the suspect claimed that he<br />
managed to hack into aircraft dozens of<br />
times in the past few years, and in one<br />
case after taking control over the engine<br />
he was able to make it climb upward.<br />
The suspect has exploited<br />
vulnerabilities in major aircraft types<br />
along with the weakness in the popular<br />
in-flight entertainment systems.<br />
These claims have been rejected and<br />
denied by the airlines involved, and the<br />
manufacturers of both the aircraft and the<br />
in-flight entertainment systems.<br />
The suspect explained that he only<br />
meant to point out the vulnerabilities<br />
for quick resolution, a type of “ethical<br />
hacking” practice without any malicious<br />
intent. The positive side of this FBI case<br />
is that all the parties involved have taken<br />
this claim seriously to deter any future<br />
attempts and put the public at ease<br />
regarding their safety, despite any added<br />
costs incurred.<br />
At the end of the spectrum from<br />
commercial aircraft, drones have gained<br />
wild popularity recently. Those unmanned,<br />
remotely controlled small-sized aircraft<br />
have opened unlimited frontiers for all<br />
types of businesses, including package<br />
delivery, agricultural purposes, providing<br />
aid and supplies in natural disasters, and<br />
military action.<br />
The usage has also reached<br />
individuals at a personal level due to the<br />
relevantly low cost of such machines. And<br />
along with the increased popularity, the<br />
potential threats started to reach the light.<br />
In this year there have been two major<br />
documented cases where vulnerabilities<br />
have been uncovered, luckily both by<br />
research scientists.<br />
The first case was by an IBM security<br />
researcher who presented the results at<br />
the major IT security conference Black<br />
Hat Asia 2016 in Singapore in April. He<br />
demonstrated his ability with somehow<br />
low efforts to control powerful drones<br />
that are usually used by police and<br />
governmental entities with an average<br />
cost of $30,000 with simple equipment<br />
that cost merely $40. The IBM security<br />
researcher has exploited several<br />
vulnerabilities which can be thought of as<br />
simple security weaknesses, they should<br />
have been avoided in the first place.<br />
Such weaknesses included a<br />
vulnerable encryption protocol between<br />
the legitimate end user and the controller<br />
module of the drone that can be hacked<br />
easily, and a radio communication<br />
between the controller module and the<br />
drone itself which lacks any encryption<br />
(in order to increase the performance and<br />
responsiveness of the drone to avoid delay<br />
in executing commands).<br />
The second case was identified<br />
in June last year by scientists from<br />
the famous research university Johns<br />
Hopkins in the US, however, their focus<br />
was on normal drones that are meant<br />
for personal use. One vulnerability is<br />
to draw the drone with huge number of<br />
requests for wireless connection, in the<br />
range of thousands per second, which<br />
causes the drone’s system to overload<br />
and shut down. Such attacks are known<br />
as denial of service attack which can be<br />
easily avoided.<br />
Other vulnerabilities are sending<br />
large data packet to the drone which<br />
it can’t handle, causing its system to<br />
crash, or for an unauthorised person to<br />
impersonate the legitimate user by way<br />
of intercepting the communication.<br />
All of these vulnerabilities are not<br />
new to the IT world, nonetheless, they<br />
do show how drone manufacturers are<br />
combining safety and security with<br />
better performance and quick-to-market<br />
delivery.<br />
The moral of the story is that<br />
new, innovative and fully electronic<br />
approach can be extremely rewarding<br />
for businesses, to achieve their strategic<br />
goals and targets. On the other hand, it<br />
is of extreme importance to ensure that<br />
going down the path of new innovation<br />
does not jeopardise any stability or<br />
security; quick return in investment<br />
should not be at the expense of future<br />
disasters. And all manufacturers should<br />
take these cases as a lesson, to invest<br />
early on to find out all vulnerabilities<br />
and weakness in their machines before<br />
they are actually exploited by malicious<br />
individuals with dire consequences.<br />
Dr. Jassim Haji<br />
Technology Executive &<br />
Researcher<br />
www.facebook.com/DrJassimHaji<br />
bh.linkedin.com/in/dr-jassimhaji-7b5885125<br />
48 January-February <strong>2018</strong>