ABI-ONE ghc program v14.indd - Grace Hopper Celebration of ...
ABI-ONE ghc program v14.indd - Grace Hopper Celebration of ...
ABI-ONE ghc program v14.indd - Grace Hopper Celebration of ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
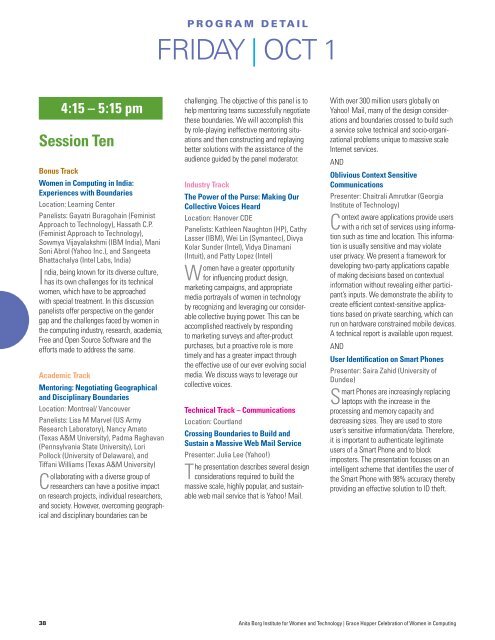
4:15 – 5:15 pm<br />
Session Ten<br />
Bonus Track<br />
Women in Computing in India:<br />
Experiences with Boundaries<br />
Location: Learning Center<br />
Panelists: Gayatri Buragohain (Feminist<br />
Approach to Technology), Hassath C.P.<br />
(Feminist Approach to Technology),<br />
Sowmya Vijayalakshmi (IBM India), Mani<br />
Soni Abrol (Yahoo Inc.), and Sangeeta<br />
Bhattachalya (Intel Labs, India)<br />
India, being known for its diverse culture,<br />
has its own challenges for its technical<br />
women, which have to be approached<br />
with special treatment. In this discussion<br />
panelists <strong>of</strong>fer perspective on the gender<br />
gap and the challenges faced by women in<br />
the computing industry, research, academia,<br />
Free and Open Source S<strong>of</strong>tware and the<br />
efforts made to address the same.<br />
Academic Track<br />
Mentoring: Negotiating Geographical<br />
and Disciplinary Boundaries<br />
Location: Montreal/ Vancouver<br />
Panelists: Lisa M Marvel (US Army<br />
Research Laboratory), Nancy Amato<br />
(Texas A&M University), Padma Raghavan<br />
(Pennsylvania State University), Lori<br />
Pollock (University <strong>of</strong> Delaware), and<br />
Tiffani Williams (Texas A&M University)<br />
Collaborating with a diverse group <strong>of</strong><br />
researchers can have a positive impact<br />
on research projects, individual researchers,<br />
and society. However, overcoming geographical<br />
and disciplinary boundaries can be<br />
p r O G r a m d e Ta i L<br />
FRIDAY | OCT 1<br />
challenging. The objective <strong>of</strong> this panel is to<br />
help mentoring teams successfully negotiate<br />
these boundaries. We will accomplish this<br />
by role-playing ineffective mentoring situations<br />
and then constructing and replaying<br />
better solutions with the assistance <strong>of</strong> the<br />
audience guided by the panel moderator.<br />
Industry Track<br />
The Power <strong>of</strong> the Purse: Making Our<br />
Collective Voices Heard<br />
Location: Hanover CDE<br />
Panelists: Kathleen Naughton (HP), Cathy<br />
Lasser (IBM), Wei Lin (Symantec), Divya<br />
Kolar Sunder (Intel), Vidya Dinamani<br />
(Intuit), and Patty Lopez (Intel)<br />
Women have a greater opportunity<br />
for influencing product design,<br />
marketing campaigns, and appropriate<br />
media portrayals <strong>of</strong> women in technology<br />
by recognizing and leveraging our considerable<br />
collective buying power. This can be<br />
accomplished reactively by responding<br />
to marketing surveys and after-product<br />
purchases, but a proactive role is more<br />
timely and has a greater impact through<br />
the effective use <strong>of</strong> our ever evolving social<br />
media. We discuss ways to leverage our<br />
collective voices.<br />
Technical Track – Communications<br />
Location: Courtland<br />
Crossing Boundaries to Build and<br />
Sustain a Massive Web Mail Service<br />
Presenter: Julia Lee (Yahoo!)<br />
The presentation describes several design<br />
considerations required to build the<br />
massive scale, highly popular, and sustainable<br />
web mail service that is Yahoo! Mail.<br />
With over 300 million users globally on<br />
Yahoo! Mail, many <strong>of</strong> the design considerations<br />
and boundaries crossed to build such<br />
a service solve technical and socio-organizational<br />
problems unique to massive scale<br />
Internet services.<br />
AND<br />
Oblivious Context Sensitive<br />
Communications<br />
Presenter: Chaitrali Amrutkar (Georgia<br />
Institute <strong>of</strong> Technology)<br />
Context aware applications provide users<br />
with a rich set <strong>of</strong> services using information<br />
such as time and location. This information<br />
is usually sensitive and may violate<br />
user privacy. We present a framework for<br />
developing two-party applications capable<br />
<strong>of</strong> making decisions based on contextual<br />
information without revealing either participant’s<br />
inputs. We demonstrate the ability to<br />
create efficient context-sensitive applications<br />
based on private searching, which can<br />
run on hardware constrained mobile devices.<br />
A technical report is available upon request.<br />
AND<br />
User Identification on Smart Phones<br />
Presenter: Saira Zahid (University <strong>of</strong><br />
Dundee)<br />
Smart Phones are increasingly replacing<br />
laptops with the increase in the<br />
processing and memory capacity and<br />
decreasing sizes. They are used to store<br />
user’s sensitive information/data. Therefore,<br />
it is important to authenticate legitimate<br />
users <strong>of</strong> a Smart Phone and to block<br />
imposters. The presentation focuses on an<br />
intelligent scheme that identifies the user <strong>of</strong><br />
the Smart Phone with 98% accuracy thereby<br />
providing an effective solution to ID theft.<br />
38 Anita Borg Institute for Women and Technology | <strong>Grace</strong> <strong>Hopper</strong> <strong>Celebration</strong> <strong>of</strong> Women in Computing