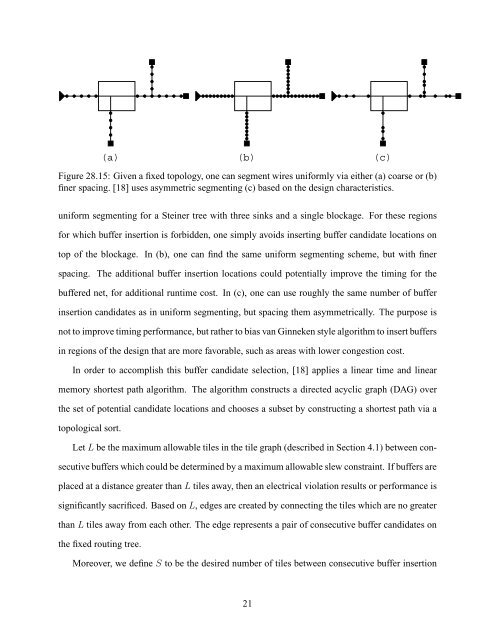
For Critical Nets, <strong>the</strong> cost impact of <strong>the</strong> environment is immaterial. We seek <strong>the</strong> absolutelybest possible slack. When a net is optimally buffered (assum<strong>in</strong>g no obstacles), its delay is a l<strong>in</strong>earfunction of its length [19]. Hence, <strong>in</strong> order to m<strong>in</strong>imize delay, we simply m<strong>in</strong>imize <strong>the</strong> number oftiles to <strong>the</strong> most critical s<strong>in</strong>k, which results <strong>in</strong> a unit cost def<strong>in</strong>ed for each tile. When merg<strong>in</strong>g <strong>the</strong>branches, we pick <strong>the</strong> branch with worst slack, so <strong>the</strong> merged cost is <strong>the</strong> maximum of both costs.The costs at s<strong>in</strong>ks are <strong>in</strong>itialized based on <strong>the</strong> s<strong>in</strong>k criticality. The more critical a s<strong>in</strong>k, <strong>the</strong> higherits <strong>in</strong>itial cost. F<strong>in</strong>ally, <strong>the</strong> objective is to m<strong>in</strong>imize cost at <strong>the</strong> source.The algorithm is able to <strong>the</strong> trade-off between <strong>the</strong> critical and non-critical cost functions dur<strong>in</strong>g<strong>the</strong> maze rout<strong>in</strong>g procedure. Let 0 ≤ K ≤ 1 be <strong>the</strong> trade-off parameter, where K = 1 correspondsto a non-critical net and K = 0 corresponds to a critical net. Based on <strong>the</strong> previously def<strong>in</strong>edcost functions for non-critical and critical nets, <strong>the</strong> cost function for a tile g i is <strong>the</strong>n 1 + K · e(g i ).For critical nets, merg<strong>in</strong>g branches is a maximization function, while it is an additive function fornon-critical nets. These ideas can be comb<strong>in</strong>ed while <strong>the</strong> merg<strong>in</strong>g cost of two children g i and g jbecomes max(cost(g i ), cost(g j )) + K · m<strong>in</strong>(cost(g i ), cost(g j )).It has been demonstrated that K can be used to trade off <strong>the</strong> cost function, <strong>the</strong> merg<strong>in</strong>g operation,and even s<strong>in</strong>k <strong>in</strong>itialization. In practice, we can first optimize all nets that need buffer<strong>in</strong>g withK = 1, which limits <strong>the</strong> use of scarce resources. After perform<strong>in</strong>g a tim<strong>in</strong>g analysis, those netsthat still have negative slack can be re-optimized with a smaller value of K, e.g., 0.7. This processof re-optimiz<strong>in</strong>g and gradually reduc<strong>in</strong>g can cont<strong>in</strong>ue until, say, K = 0.1.5.4 Relat<strong>in</strong>g <strong>Buffer<strong>in</strong>g</strong> Candidate Locations to <strong>Layout</strong> <strong>Environment</strong>While <strong>the</strong> previous algorithms are consider<strong>in</strong>g <strong>the</strong> rout<strong>in</strong>g tree adjustment, <strong>the</strong> follow<strong>in</strong>g algorithmfocuses on buffer <strong>in</strong>sertion candidate selection for congestion reduction.Van G<strong>in</strong>neken style algorithm assumes that a set of buffer <strong>in</strong>sertion candidate locations arepredeterm<strong>in</strong>ed for <strong>the</strong> given topology. The most common method for select<strong>in</strong>g <strong>in</strong>sertion po<strong>in</strong>ts is tochoose <strong>the</strong>m at regular <strong>in</strong>tervals. Alpert et al. [15] show how <strong>the</strong> quality of results is affected by <strong>the</strong>degree of wire segment<strong>in</strong>g that is performed on <strong>the</strong> topology. For example, Figure 28.15(a) shows20
(a)(b)Figure 28.15: Given a fixed topology, one can segment wires uniformly via ei<strong>the</strong>r (a) coarse or (b)f<strong>in</strong>er spac<strong>in</strong>g. [18] uses asymmetric segment<strong>in</strong>g (c) based on <strong>the</strong> design characteristics.(c)uniform segment<strong>in</strong>g for a Ste<strong>in</strong>er tree with three s<strong>in</strong>ks and a s<strong>in</strong>gle blockage. For <strong>the</strong>se regionsfor which buffer <strong>in</strong>sertion is forbidden, one simply avoids <strong>in</strong>sert<strong>in</strong>g buffer candidate locations ontop of <strong>the</strong> blockage. In (b), one can f<strong>in</strong>d <strong>the</strong> same uniform segment<strong>in</strong>g scheme, but with f<strong>in</strong>erspac<strong>in</strong>g. The additional buffer <strong>in</strong>sertion locations could potentially improve <strong>the</strong> tim<strong>in</strong>g for <strong>the</strong>buffered net, for additional runtime cost. In (c), one can use roughly <strong>the</strong> same number of buffer<strong>in</strong>sertion candidates as <strong>in</strong> uniform segment<strong>in</strong>g, but spac<strong>in</strong>g <strong>the</strong>m asymmetrically. The purpose isnot to improve tim<strong>in</strong>g performance, but ra<strong>the</strong>r to bias van G<strong>in</strong>neken style algorithm to <strong>in</strong>sert buffers<strong>in</strong> regions of <strong>the</strong> design that are more favorable, such as areas with lower congestion cost.In order to accomplish this buffer candidate selection, [18] applies a l<strong>in</strong>ear time and l<strong>in</strong>earmemory shortest path algorithm. The algorithm constructs a directed acyclic graph (DAG) over<strong>the</strong> set of potential candidate locations and chooses a subset by construct<strong>in</strong>g a shortest path via atopological sort.Let L be <strong>the</strong> maximum allowable tiles <strong>in</strong> <strong>the</strong> tile graph (described <strong>in</strong> Section 4.1) between consecutivebuffers which could be determ<strong>in</strong>ed by a maximum allowable slew constra<strong>in</strong>t. If buffers areplaced at a distance greater than L tiles away, <strong>the</strong>n an electrical violation results or performance issignificantly sacrificed. Based on L, edges are created by connect<strong>in</strong>g <strong>the</strong> tiles which are no greaterthan L tiles away from each o<strong>the</strong>r. The edge represents a pair of consecutive buffer candidates on<strong>the</strong> fixed rout<strong>in</strong>g tree.Moreover, we def<strong>in</strong>e S to be <strong>the</strong> desired number of tiles between consecutive buffer <strong>in</strong>sertion21