A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
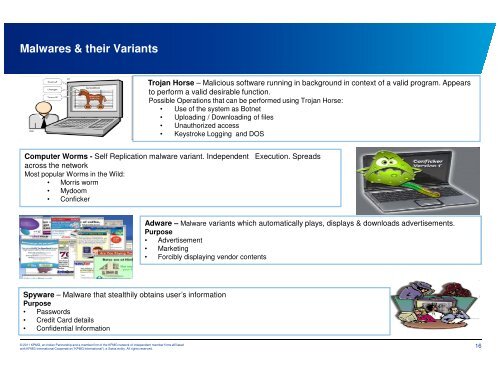
<strong>Malwares</strong> & their Variants<br />
Trojan Horse – Malicious software running in background in c<strong>on</strong>text of a valid program. Appears<br />
to perform a valid desirable functi<strong>on</strong>.<br />
Possible Operati<strong>on</strong>s that can be performed using Trojan Horse:<br />
• Use of the system as Botnet<br />
• Uploading / Downloading of files<br />
• Unauthorized access<br />
• Keystroke Logging and DOS<br />
Computer Worms - Self Replicati<strong>on</strong> malware variant. Independent Executi<strong>on</strong>. Spreads<br />
across the network<br />
Most popular Worms in the Wild:<br />
• Morris worm<br />
• Mydoom<br />
• C<strong>on</strong>ficker<br />
Spyware – Malware that stealthily obtains user’s informati<strong>on</strong><br />
Purpose<br />
• Passwords<br />
• Credit Card details<br />
• C<strong>on</strong>fidential Informati<strong>on</strong><br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.<br />
Computer Worms<br />
Adware – Malware variants which automatically plays, displays & downloads advertisements.<br />
Purpose<br />
• Advertisement<br />
• Marketing<br />
• Forcibly displaying vendor c<strong>on</strong>tents<br />
16