A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
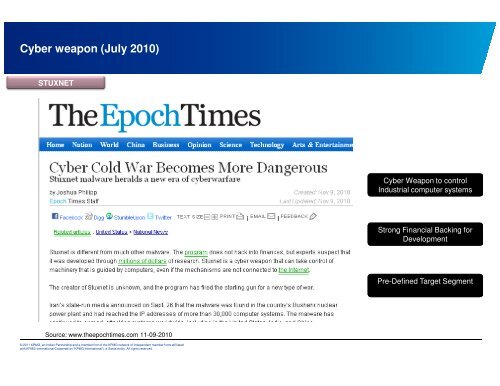
Cyber weap<strong>on</strong> (July 2010)<br />
STUXNET<br />
Source: www.theepochtimes.com 11-09-2010<br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.<br />
Cyber Weap<strong>on</strong> to c<strong>on</strong>trol<br />
Industrial computer systems<br />
Str<strong>on</strong>g Financial Backing for<br />
Development<br />
Pre-Defined Target Segment