A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
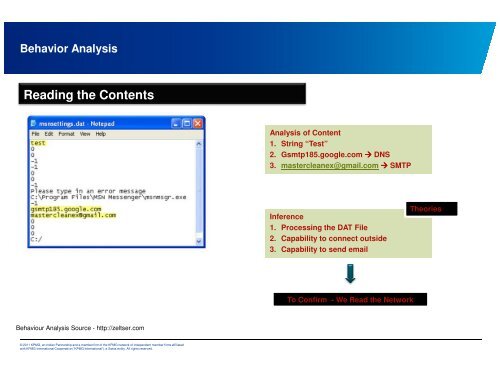
Behavior Analysis<br />
Reading the C<strong>on</strong>tents<br />
Behaviour Analysis Source - http://zeltser.com<br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.<br />
Analysis of C<strong>on</strong>tent<br />
1. String “Test”<br />
2. Gsmtp185.google.com ���� DNS<br />
3. mastercleanex@gmail.com ���� SMTP<br />
Inference<br />
1. Processing the DAT File<br />
2. Capability to c<strong>on</strong>nect outside<br />
3. Capability to send email<br />
To C<strong>on</strong>firm - We Read the Network<br />
Theories