A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
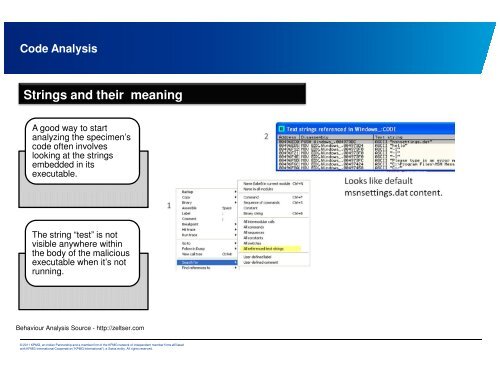
Code Analysis<br />
Strings and their meaning<br />
A good way to start<br />
analyzing the specimen’s<br />
code often involves<br />
looking at the strings<br />
embedded in its<br />
executable.<br />
The string “test” is not<br />
visible anywhere within<br />
the body of the malicious<br />
executable when it’s not<br />
running.<br />
Behaviour Analysis Source - http://zeltser.com<br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.