A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
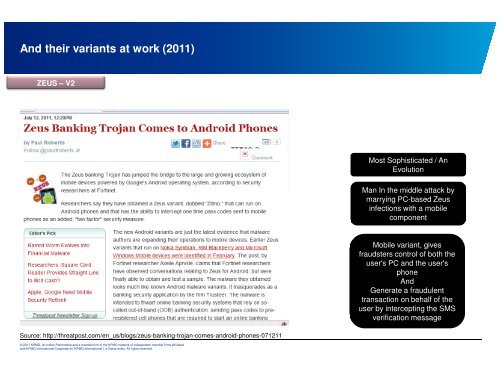
And their variants at work (2011)<br />
ZEUS – V2<br />
Source: http://threatpost.com/en_us/blogs/zeus-banking-trojan-comes-android-ph<strong>on</strong>es-071211<br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.<br />
Most Sophisticated / An<br />
Evoluti<strong>on</strong><br />
Man In the middle attack by<br />
marrying PC-based Zeus<br />
infecti<strong>on</strong>s with a mobile<br />
comp<strong>on</strong>ent<br />
Mobile variant, gives<br />
fraudsters c<strong>on</strong>trol of both the<br />
user's PC and the user's<br />
ph<strong>on</strong>e<br />
And<br />
Generate a fraudulent<br />
transacti<strong>on</strong> <strong>on</strong> behalf of the<br />
user by intercepting the SMS<br />
verificati<strong>on</strong> message