A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
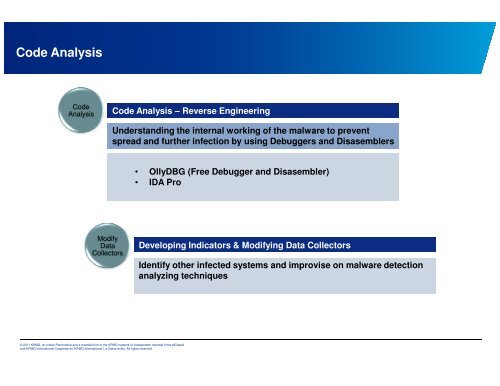
Code Analysis<br />
Code<br />
Analysis<br />
Modify<br />
Data<br />
Collectors<br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.<br />
Code Analysis – <strong>Reverse</strong> <strong>Engineering</strong><br />
Understanding the internal working of the malware to prevent<br />
spread and further infecti<strong>on</strong> by using Debuggers and Disasemblers<br />
• OllyDBG (Free Debugger and Disasembler)<br />
• IDA Pro<br />
Developing Indicators & Modifying Data Collectors<br />
Identify other infected systems and improvise <strong>on</strong> malware detecti<strong>on</strong><br />
analyzing techniques