A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
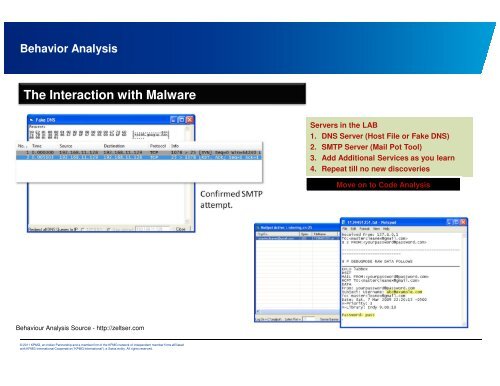
Behavior Analysis<br />
The Interacti<strong>on</strong> with Malware<br />
Behaviour Analysis Source - http://zeltser.com<br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.<br />
Servers in the LAB<br />
1. DNS Server (Host File or Fake DNS)<br />
2. SMTP Server (Mail Pot Tool)<br />
3. Add Additi<strong>on</strong>al Services as you learn<br />
4. Repeat till no new discoveries<br />
Move <strong>on</strong> to Code Analysis