A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
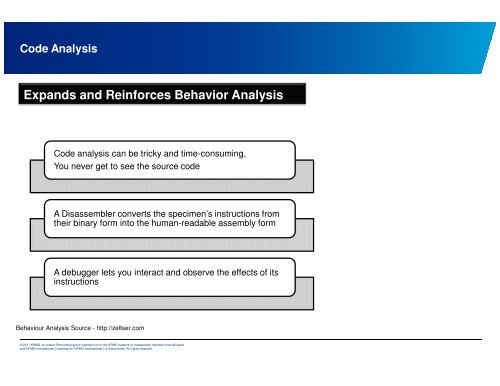
Code Analysis<br />
Expands and Reinforces Behavior Analysis<br />
Code analysis can be tricky and time-c<strong>on</strong>suming,<br />
You never get to see the source code<br />
A Disassembler c<strong>on</strong>verts the specimen’s instructi<strong>on</strong>s from<br />
their binary form into the human-readable assembly form<br />
A debugger lets you interact and observe the effects of its<br />
instructi<strong>on</strong>s<br />
Behaviour Analysis Source - http://zeltser.com<br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.