A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
A Primer on Reverse Engineering Malwares
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
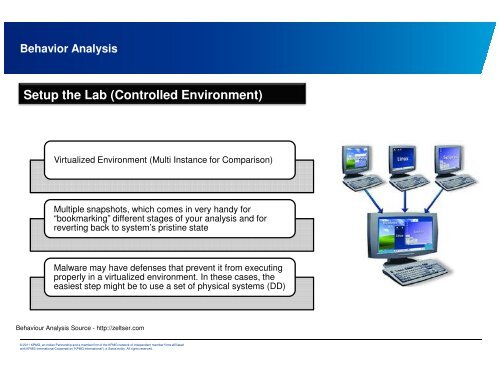
Behavior Analysis<br />
Setup the Lab (C<strong>on</strong>trolled Envir<strong>on</strong>ment)<br />
Virtualized Envir<strong>on</strong>ment (Multi Instance for Comparis<strong>on</strong>)<br />
Multiple snapshots, which comes in very handy for<br />
“bookmarking” different stages of your analysis and for<br />
reverting back to system’s pristine state<br />
Malware may have defenses that prevent it from executing<br />
properly in a virtualized envir<strong>on</strong>ment. In these cases, the<br />
easiest step might be to use a set of physical systems (DD)<br />
Behaviour Analysis Source - http://zeltser.com<br />
© 2011 KPMG, an Indian Partnership and a member firm of the KPMG network of independent member firms affiliated<br />
with KPMG Internati<strong>on</strong>al Cooperative (“KPMG Internati<strong>on</strong>al”), a Swiss entity. All rights reserved.