B.<strong>Tech</strong>. <strong>Computer</strong> <strong>Science</strong> & <strong>Engineering</strong> (Regular)Linkers, Macros, Compilers, Software tools: Texteditors, Interpreters, program generators, Testingsoftware, Programming environment (such asIntegrated Development Editors)2. SYSTEM SOFTWARE SPECIFICS: Compiler:Brief overview of compilation process, Incrementalcompiler, structure of compiler: its different phases,Compiler construction tools. Assembler: Problemstatement, single phase and two phase assembler,symbol table; Loader schemes, compile and goLoader, general loader schemes, absolute loader,Subroutine linkage, Reallocating loader, Directlinkage Loader, Binders, Linking loader, overlays3. LEXICAL AND SYNTAX ANALYSIS: Role oflexical analyzer, design of lexical analyzer, regularexpressions, Specification and recognition oftokens, input buffering, a language specifyinglexical analyzer. Finite automata, conversion fromregular expression to finite automata, and viceversa, minimizing number of states of DFA,Implementation of lexical analyzer. SyntaxAnalysis: Role of parsers, context free grammars,definition of parsing4. PARSING TECHNIQUE: Shift- reduce parsing,operator precedence parsing, top down parsing,predictive parsing. LR parsers, SLR, LALR andCanonical LR parser5. SYNTAX DIRECTED TRANSLATIONS: Syntaxdirected definition, construction of syntax trees,syntax directed translation scheme,implementation of syntax directed translation, threeaddress code, quadruples and triples6. SYMBOL TABLE & ERROR DETECTION ANDRECOVERY: Symbol tables, its contents and datastructure for symbol tables; trees, arrays, linkedlists, hash tables. Errors, lexical phase error,syntactic phase error, semantic error7. CODE OPTIMIZATION AND CODEGENERATION: Code generation, forms of objectscode, machine dependent code, optimization,register allocation for temporary and user definedvariablesTEXT BOOKAlfred V. Aho, Ravi Sethi & J.D. Ullman, “CompilersPrinciple, <strong>Tech</strong>niques & Tools”, Addison Wesley, 1998REFERENCE BOOKS1. Kakde O. G., “Compiler Design”, LaxmiPublications, 19952. Dhamdhere, “System Software”, McGraw Hill,19863. Trembley and Sorenson, “Theory and Practice ofCompiler Writing”, McGraw Hill, 19854. Aho Alfred V. And Ullman Jeffrey D “Principles ofCompiler Design”, Narosa Publication, 1989.WEB REFERENCES1. www.onesmartclick.com/engineering/compilerdesign.html2. www.cse.iitd.ernet.in/~sak/courses/cdp/slides.pdf3. www.holub.com/software/compiler.design.in.c.docs.pdf4. en.wikipedia.org/wiki/Principles_of_Compiler_Design5. www.holub.com/software/compiler.design.in.c.htmlCS-422CRYPTOGRAPHY AND L T P CrDATA COMPRESSION 5 0 0 3OBJECTIVEThe course will attempt to dispel some of the manymyths that surround the idea of cryptography.Cryptography is (and will continue to be) anincreasingly important area of IT and it is important thatpractitioners are aware of the realities of the subject.The course will provide a down-to-earth overview ofcryptographic techniques applicable in an ITenvironment, and outline the constraints and limitationsof realistic secure systems. A running theme is thetradeoff between usability and security of a system.Also covered are a number of compression techniques- data compression and data encryption are, in somerespects, closely related. A working knowledge of C isassumed and essential.PRE-REQUISITESKnowledge of cryptography, analysis & designalgorithms and mathematics1. INTRODUCTION: Basics of cryptography; history;usefulness of compression techniques2. COMPRESSION: Packing, Huffman coding, Runlength encoding, Lempel-Ziv-Welch, PKZIP, Deltamodulation, JPEG; latest compression techniques3. ERROR DETECTION AND CORRECTION: Parity,1, 2, n-dimensions; Hamming codes; p-out-of-qcodes4. CRYPTOGRAPHY: vocabulary; history;steganography - visual textual, cipher hiding, falseerrors; public key cryptography - authentication,signatures, deniability5. MATHEMATICS: Information; confusion; diffusion;modular arithmetic; inverses; Fermats littletheorem; Chinese remainder theorem; factoring;prime numbers; discrete logarithms6. ALGORITHMS: DES; AES (Rijndael); IDEA; Onetime pad; Secret sharing and splitting; RSA; Ellipticcurves; Modes; Random numbers7. ATTACKING SYSTEMS: Recognition; destroyingdata; cryptanalysis: differential cryptanalysis,cracking desTEXT BOOKSchneier B., “Applied Cryptography: Protocols,Algorithms and Source Code in C”, 2nd edition, Wiley,1996.REFERENCE BOOKS1. Desai Suhas, “Security in Computing”, PearsonsEducation 20102. “Integration of Data Compression andCryptography: Another Way to Increase theInformation Security”, IEEE <strong>Computer</strong> SocietyVolume 2 ,20073. Trappe W. and Washington L., “Introduction toCryptography”, 2nd edition, Pearson Education,2006WEB REFERENCES1. http://www.data-compression.com/index.shtml2. http://www.webopedia.com/TERM/D/data_compression.html36
Lingaya’s University, Faridabad3. http://en.wikipedia.org/wiki/Data_compression4. http://www.debugmode.com/imagecmp/CS-431ADVANCED COMPUTER L T P CrARCHITECTURE 5 0 0 3OBJECTIVETo introduce various technological aspects aboutparallelism in super computing, microprocessorssupporting such high scale computing, other hardwarearchitectures, ultimately leading to high performancecomputing through grid computing.PRE-REQUISITESKnowledge of digital electronics, digital system design,computer networks and computer organization &architecture1. PARALLEL COMPUTER MODELS: The state ofcomputing, multiprocessors and multicomputers;multi-vector and SIMD computers; architecturaldevelopment tracks.2. PROGRAM AND NETWORK PROPERTIES:Conditions of parallelism; data and resourcedependences; hardware and software parallelism;program partitioning and scheduling; grain sizeand latency; program flow mechanisms; controlflow versus data flow, data flow architecture;demand driven mechanisms; comparisons of flowmechanisms3. SYSTEMS INTERCONNECT ARCHITECTURES:Network properties and routing, staticinterconnection networks; dynamic interconnectionnetworks; multiprocessor system interconnects;hierarchical bus systems; crossbar switch andmultiport memory; multistage and combiningnetwork.4. PROCESSORS AND MEMORY HIERARCHY:Advanced processor technology; instruction-setarchitectures; CISC scalar processors; RISC scalarprocessors; superscalar processors, VLIWarchitectures; vector and symbolic processorsmemory technology: hierarchical memorytechnology, inclusion, coherence and locality,memory capacity planning, virtual memorytechnology5. BACKPLANE BUS SYSTEM: Backplane busspecification; addressing and timing protocols;arbitration transaction and interrupt; cacheaddressing models; direct mapping andassociative caches.6. PIPELINING: Linear pipeline processor; nonlinearpipeline processor; instruction pipeline design;mechanisms for instruction pipelining; dynamicinstruction scheduling; branch handlingtechniques; arithmetic pipeline design; computerarithmetic principles; static arithmetic pipeline,multifunctional arithmetic pipelines.7. VECTOR PROCESSING PRINCIPLES: Vectorinstruction types; vector-access memory schemes;synchronous parallel processing: SIMDarchitecture and programming principles; SIMDparallel algorithms; SIMD computers andperformance enhancementTEXT BOOKHwang Kai and Briggs A., “Advanced <strong>Computer</strong>Architecture”, Tata McGraw Hill, 2008REFERENCE BOOKS1. Hennessy John L. and Patterson David A.,“<strong>Computer</strong> Architecture: A Quantitative Approach”,3rd edition, 20022. Flynn Michael J., “Pipelined and Parallel ProcessorDesign”, Narosa Publications, Reprint 20093. Hwang Kai and Briggs A., “<strong>Computer</strong>Architecture and Parallel Processing”, McGraw-Hill, 19904. Sima Dezso, Fountain Terence and Kacsuk Peter,“Advanced <strong>Computer</strong> Architectures”, PearsonEducationWEB REFERENCES1. http://www.doc.ic.ac.uk/~phjk/AdvancedCompArchitecture/Lectures/2. http://www.ecs.syr.edu/faculty/ercanli/cse661/3. http://cs.binghamton.edu/~nael/classes/cs325/CS-432NATURAL LANGUAGE L T P CrPROCESSING 5 0 0 3OBJECTIVETo motivate understanding of issues related to naturallanguage understanding, generation and translation,which ultimately linked to machine learning, computervision and expert systems. This course provides anintroduction to the field of computational linguistics,also called natural language processing (NLP) - thecreation of computer programs that can understandand generate natural languages (such as English).Natural language understanding as a vehicle will beused to introduce the three major subfields of NLP:syntax (which concerns itself with determining thestructure of an utterance), semantics (which concernsitself with determining the explicit truth-functionalmeaning of a single utterance), and pragmatics (whichconcerns itself with deriving the context-dependentmeaning of an utterance when it is used in a specificdiscourse context). The course will introduce bothknowledge-based and statistical approaches to NLP,illustrate the use of NLP techniques and tools in avariety of application areas, and provide insight intomany open research problems.PRE-REQUISITESKnowledge of theory of computations1. INTRODUCTION TO NATURAL LANGUAGEUNDERSTANDING: The study of language;applications of NLP; evaluating languageunderstanding systems; different levels oflanguage analysis; representations andunderstanding; organization of natural languageunderstanding systems; linguistic background: anoutline of English syntax.2. GRAMMARS AND PARSING: Grammars andsentence structure; top-down and bottom-upparsers; transition network grammars; top-downchart parsing; feature systems and augmentedgrammars: basic feature system for English37
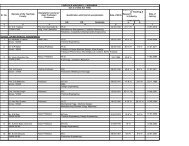
- Page 1: B.Tech. Degree ProgrammeComputer Sc
- Page 6 and 7: B.Tech. Computer Science & Engineer
- Page 8 and 9: B.Tech. Computer Science & Engineer
- Page 10 and 11: B.Tech. Computer Science & Engineer
- Page 12 and 13: B.Tech. Computer Science & Engineer
- Page 14 and 15: B.Tech. Computer Science & Engineer
- Page 16 and 17: B.Tech. Computer Science & Engineer
- Page 18 and 19: B.Tech. Computer Science & Engineer
- Page 20 and 21: B.Tech. Computer Science & Engineer
- Page 22 and 23: B.Tech. Computer Science & Engineer
- Page 24 and 25: B.Tech. Computer Science & Engineer
- Page 26 and 27: B.Tech. Computer Science & Engineer
- Page 28 and 29: B.Tech. Computer Science & Engineer
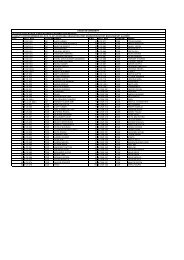
- Page 31 and 32: Lingaya’s University, FaridabadCH
- Page 33 and 34: Lingaya’s University, FaridabadWE
- Page 35 and 36: Lingaya’s University, FaridabadCS
- Page 37 and 38: Lingaya’s University, Faridabad2.
- Page 39: Lingaya’s University, Faridabadpe
- Page 43 and 44: Lingaya’s University, FaridabadPR
- Page 45 and 46: Lingaya’s University, Faridabadco
- Page 47 and 48: Lingaya’s University, Faridabadar
- Page 49 and 50: Lingaya’s University, Faridabadex
- Page 51 and 52: Lingaya’s University, Faridabad1.
- Page 53 and 54: Lingaya’s University, Faridabad1.
- Page 55 and 56: Lingaya’s University, FaridabadRE
- Page 57 and 58: Lingaya’s University, Faridabad1.
- Page 61 and 62: Lingaya’s University, Faridabad9.
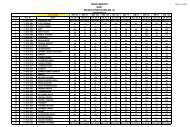
- Page 64 and 65: B.Tech. Computer Science & Engineer
- Page 66 and 67: B.Tech. Computer Science & Engineer
- Page 68 and 69: B.Tech. Computer Science & Engineer
- Page 70 and 71: B.Tech. Computer Science & Engineer
- Page 72 and 73: B.Tech. Computer Science & Engineer
- Page 74 and 75: B.Tech. Computer Science & Engineer
- Page 76 and 77: B.Tech. Computer Science & Engineer
- Page 78 and 79: B.Tech. Computer Science & Engineer
- Page 80 and 81: B.Tech. Computer Science & Engineer
- Page 82 and 83: B.Tech. Computer Science & Engineer
- Page 84 and 85: B.Tech. Computer Science & Engineer
- Page 86 and 87: B.Tech. Computer Science & Engineer
- Page 88 and 89: B.Tech. Computer Science & Engineer
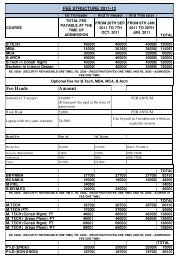
- Page 90 and 91:
B.Tech. Computer Science & Engineer
- Page 92 and 93:
B.Tech. Computer Science & Engineer
- Page 94 and 95:
B.Tech. Computer Science & Engineer
- Page 96 and 97:
B.Tech. Computer Science & Engineer
- Page 98 and 99:
B.Tech. Computer Science & Engineer
- Page 100 and 101:
B.Tech. Computer Science & Engineer
- Page 102 and 103:
B.Tech. Computer Science & Engineer