B.<strong>Tech</strong>. <strong>Computer</strong> <strong>Science</strong> & <strong>Engineering</strong> (Regular)randomness; signatures; simple cryptographicprotocols.3. SOFTWARE SECURITY: What is softwaresecurity?; Common software vulnerabilities: lack ofinput validation (buffer overflows, SQL injections,race conditions, access control, etc.; flaws: designflaws, implementation flaws; deployment flaws;case studies; Language level security: typing;tainting input data; untrusted code security;application level security: runtime monitoring; staticanalysis; verification; JML, Spec; softwareevaluation; case studies.4. VERIFICATION OF SECURITY PROTOCOLS:Modelling of black box security protocols; intrudermodel; security requirements; BAN logics andother security protocol logics; process algebraicapproach to security protocol verification; modelchecking; Spi calculus; strand spaces; operationalmodels; security protocols in action.5. SECURITY IN ORGANISATIONS: Securitypolicies; Roles; Classifications; Assets and threats;Risk, vulnerability; control; attack; damage; Riskanalysis; Methods/tools for risk analysis; CERTs;Risk assessment and risk management6. INFORMATION SECURITY STANDARDS: Codeof Practice for Information Security (BS7799 andISO 27001); evaluation of information security, likeITSEC and the Common Criteria; Security plan;attack trees; business continuity planning/incidentrecovery; Legal issues: patents and copyright.7. NETWORK SECURITY: Principles behind networksecurity; their main protocols as well as networksecurity mechanisms and techniques; wired andwireless networks: IP security, Email security, Websecurity, secure management, Intruders, Viruses,Firewalls and Privacy.TEXT BOOKWilliam Stallings, “Network Security Essentials -Applications and Standards”, 2nd Edition, Prentice Hall,ISBN 0-13-120271-5REFERENCE BOOKS1. Anderson R. J., “Security <strong>Engineering</strong>: A guide toBuilding Dependable Distributed Systems”, JohnWiley & Sons Inc, New York, 2001, ISBN 0-471-38922-62. van Tilborg H. C. A., “Fundamentals of Cryptology:A Professional Reference and Interactive Tutorial”,Kluwer Academic Publishers, 2000.3. Kurose James F. and Ross Keith W., “<strong>Computer</strong>Networking: A Top-Down Approach Featuring theInternet”, Addison Wesley, 2005, ISBN 0-321-26976-4WEB REFERENCES1. https://www.securityforum.org2. www.freetechbooks.com/information-securityf52.html3. csrc.nist.gov/4. www.infsec.ethz.chIT-443INFORMATION STORAGE & L T P CrMANAGEMENT 5 0 0 3OBJECTIVEUsing a “building block” approach, the ISM curriculumprovides a core understanding of storage technologiesand progresses into system architectures, introductionto networked storage, and introduction to informationavailability. The course provides a comprehensiveintroduction to data storage technology fundamentals.Students will gain knowledge of the core logical andphysical components that make up a storage systemsinfrastructure.PRE-REQUISITESKnowledge of computer networks1. INTRODUCTION: Meeting today's data storageneeds - data creation; data creation: individuals,business; categories of data; data storage models;common data storage media and solutions - tapestorage systems, optical data storage, disk basedstorage2. DATA CENTER INFRASTRUCTURE: Example;key requirements of storage systems managementactivities3. STORAGE SYSTEMS ARCHITECTURE: Storagesystem environment; components of a host;connectivity; physical disks; RAID array; diskstorage systems; data flow exercise4. NETWORKED STORAGE: Direct AttachedStorage (DAS), Network Attached Storage (NAS),Fiber Channel Storage Area Network (FC SAN), IPStorage Area Network (IP SAN), ContentAddressed Storage (CAS)5. BUSINESS CONTINUITY: Introduction, overview,backup and recovery, local replication, remotereplication.6. MONITORING AND MANAGING THE DATACENTER: Areas of the data center to monitor;considerations for monitoring the data center;techniques for managing the data center.7. SECURING STORAGE AND STORAGEVIRTUALIZATION: Securing the storageinfrastructure; virtualization technologies.TEXT BOOKOsborne Marc Farley, “Building Storage Networks”,Tata McGraw HillREFERENCE BOOKS1. Spalding Robert, “Storage Networks: TheComplete Reference“, Tata McGraw Hill2. Gupta Meeta, “Storage Area NetworkFundamentals”, Pearson Education Limited3. Kowalski Gerald J. and Maybury Mark T.,“Information Storage & Retrieval Systems Theory& Implementation”, BS Publications4. Thejendra B. S., “Disaster Recovery & BusinessContinuity”, Shroff Publishers & Distributors, EMC– Students Kit.WEB REFERENCES1. http://www.cs.cmu.edu/~fp/courses/03-312/handouts/18-storage.pdf2. http://www.freedownloadscenter.com/Information_Management/64
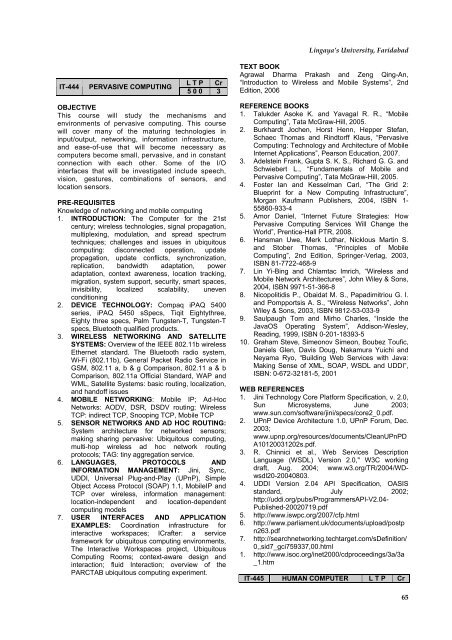
Lingaya’s University, FaridabadIT-444PERVASIVE COMPUTINGL T P Cr5 0 0 3TEXT BOOKAgrawal Dharma Prakash and Zeng Qing-An,“Introduction to Wireless and Mobile Systems”, 2ndEdition, 2006OBJECTIVEThis course will study the mechanisms andenvironments of pervasive computing. This coursewill cover many of the maturing technologies ininput/output, networking, information infrastructure,and ease-of-use that will become necessary ascomputers become small, pervasive, and in constantconnection with each other. Some of the I/Ointerfaces that will be investigated include speech,vision, gestures, combinations of sensors, andlocation sensors.PRE-REQUISITESKnowledge of networking and mobile computing1. INTRODUCTION: The <strong>Computer</strong> for the 21stcentury; wireless technologies, signal propagation,multiplexing, modulation, and spread spectrumtechniques; challenges and issues in ubiquitouscomputing: disconnected operation, updatepropagation, update conflicts, synchronization,replication, bandwidth adaptation, poweradaptation, context awareness, location tracking,migration, system support, security, smart spaces,invisibility, localized scalability, unevenconditioning2. DEVICE TECHNOLOGY: Compaq iPAQ 5400series, iPAQ 5450 sSpecs, Tiqit Eightythree,Eighty three specs, Palm Tungsten-T, Tungsten-Tspecs, Bluetooth qualified products.3. WIRELESS NETWORKING AND SATELLITESYSTEMS: Overview of the IEEE 802.11b wirelessEthernet standard. The Bluetooth radio system,Wi-Fi (802.11b), General Packet Radio Service inGSM, 802.11 a, b & g Comparison, 802.11 a & bComparison, 802.11a Official Standard, WAP andWML, Satellite Systems: basic routing, localization,and handoff issues4. MOBILE NETWORKING: Mobile IP; Ad-HocNetworks: AODV, DSR, DSDV routing; WirelessTCP: indirect TCP, Snooping TCP, Mobile TCP5. SENSOR NETWORKS AND AD HOC ROUTING:System architecture for networked sensors;making sharing pervasive: Ubiquitous computing,multi-hop wireless ad hoc network routingprotocols; TAG: tiny aggregation service.6. LANGUAGES, PROTOCOLS ANDINFORMATION MANAGEMENT: Jini, Sync,UDDI, Universal Plug-and-Play (UPnP), SimpleObject Access Protocol (SOAP) 1.1, MobileIP andTCP over wireless, information management:location-independent and location-dependentcomputing models7. USER INTERFACES AND APPLICATIONEXAMPLES: Coordination infrastructure forinteractive workspaces; ICrafter: a serviceframework for ubiquitous computing environments,The Interactive Workspaces project, UbiquitousComputing Rooms; context-aware design andinteraction; fluid Interaction; overview of thePARCTAB ubiquitous computing experiment.REFERENCE BOOKS1. Talukder Asoke K. and Yavagal R. R., “MobileComputing”, Tata McGraw-Hill, 2005.2. Burkhardt Jochen, Horst Henn, Hepper Stefan,Schaec Thomas and Rindtorff Klaus, “PervasiveComputing: <strong>Tech</strong>nology and Architecture of MobileInternet Applications”, Pearson Education, 2007.3. Adelstein Frank, Gupta S. K. S., Richard G. G. andSchwiebert L., “Fundamentals of Mobile andPervasive Computing”, Tata McGraw-Hill, 2005.4. Foster Ian and Kesselman Carl, “The Grid 2:Blueprint for a New Computing Infrastructure”,Morgan Kaufmann Publishers, 2004, ISBN 1-55860-933-45. Amor Daniel, “Internet Future Strategies: HowPervasive Computing Services Will Change theWorld”, Prentice-Hall PTR, 2008.6. Hansman Uwe, Merk Lothar, Nicklous Martin S.and Stober Thomas, “Principles of MobileComputing”, 2nd Edition, Springer-Verlag, 2003,ISBN 81-7722-468-97. Lin Yi-Bing and Chlamtac Imrich, “Wireless andMobile Network Architectures”, John Wiley & Sons,2004, ISBN 9971-51-366-88. Nicopolitidis P., Obaidat M. S., Papadimitriou G. I.and Pompportsis A. S., “Wireless Networks”, JohnWiley & Sons, 2003, ISBN 9812-53-033-99. Saulpaugh Tom and Mirho Charles, “Inside theJavaOS Operating System”, Addison-Wesley,Reading, 1999, ISBN 0-201-18393-510. Graham Steve, Simeonov Simeon, Boubez Toufic,Daniels Glen, Davis Doug, Nakamura Yuichi andNeyama Ryo, “Building Web Services with Java:Making Sense of XML, SOAP, WSDL and UDDI”,ISBN: 0-672-32181-5, 2001WEB REFERENCES1. Jini <strong>Tech</strong>nology Core Platform Specification, v. 2.0,Sun Microsystems, June 2003;www.sun.com/software/jini/specs/core2_0.pdf.2. UPnP Device Architecture 1.0, UPnP Forum, Dec.2003;www.upnp.org/resources/documents/CleanUPnPDA10120031202s.pdf.3. R. Chinnici et al., Web Services DescriptionLanguage (WSDL) Version 2.0," W3C workingdraft, Aug. 2004; www.w3.org/TR/2004/WDwsdl20-20040803.4. UDDI Version 2.04 API Specification, OASISstandard, July 2002;http://uddi.org/pubs/<strong>Programme</strong>rsAPI-V2.04-Published-20020719.pdf5. http://www.iswpc.org/2007/cfp.html6. http://www.parliament.uk/documents/upload/postpn263.pdf7. http://searchnetworking.techtarget.com/sDefinition/0,,sid7_gci759337,00.html1. http://www.isoc.org/inet2000/cdproceedings/3a/3a_1.htmIT-445 HUMAN COMPUTER L T P Cr65
- Page 1:
B.Tech. Degree ProgrammeComputer Sc
- Page 6 and 7:
B.Tech. Computer Science & Engineer
- Page 8 and 9:
B.Tech. Computer Science & Engineer
- Page 10 and 11:
B.Tech. Computer Science & Engineer
- Page 12 and 13:
B.Tech. Computer Science & Engineer
- Page 14 and 15:
B.Tech. Computer Science & Engineer
- Page 16 and 17:
B.Tech. Computer Science & Engineer
- Page 18 and 19: B.Tech. Computer Science & Engineer
- Page 20 and 21: B.Tech. Computer Science & Engineer
- Page 22 and 23: B.Tech. Computer Science & Engineer
- Page 24 and 25: B.Tech. Computer Science & Engineer
- Page 26 and 27: B.Tech. Computer Science & Engineer
- Page 28 and 29: B.Tech. Computer Science & Engineer
- Page 31 and 32: Lingaya’s University, FaridabadCH
- Page 33 and 34: Lingaya’s University, FaridabadWE
- Page 35 and 36: Lingaya’s University, FaridabadCS
- Page 37 and 38: Lingaya’s University, Faridabad2.
- Page 39 and 40: Lingaya’s University, Faridabadpe
- Page 41 and 42: Lingaya’s University, Faridabad3.
- Page 43 and 44: Lingaya’s University, FaridabadPR
- Page 45 and 46: Lingaya’s University, Faridabadco
- Page 47 and 48: Lingaya’s University, Faridabadar
- Page 49 and 50: Lingaya’s University, Faridabadex
- Page 51 and 52: Lingaya’s University, Faridabad1.
- Page 53 and 54: Lingaya’s University, Faridabad1.
- Page 55 and 56: Lingaya’s University, FaridabadRE
- Page 57 and 58: Lingaya’s University, Faridabad1.
- Page 61 and 62: Lingaya’s University, Faridabad9.
- Page 64 and 65: B.Tech. Computer Science & Engineer
- Page 66 and 67: B.Tech. Computer Science & Engineer
- Page 70 and 71: B.Tech. Computer Science & Engineer
- Page 72 and 73: B.Tech. Computer Science & Engineer
- Page 74 and 75: B.Tech. Computer Science & Engineer
- Page 76 and 77: B.Tech. Computer Science & Engineer
- Page 78 and 79: B.Tech. Computer Science & Engineer
- Page 80 and 81: B.Tech. Computer Science & Engineer
- Page 82 and 83: B.Tech. Computer Science & Engineer
- Page 84 and 85: B.Tech. Computer Science & Engineer
- Page 86 and 87: B.Tech. Computer Science & Engineer
- Page 88 and 89: B.Tech. Computer Science & Engineer
- Page 90 and 91: B.Tech. Computer Science & Engineer
- Page 92 and 93: B.Tech. Computer Science & Engineer
- Page 94 and 95: B.Tech. Computer Science & Engineer
- Page 96 and 97: B.Tech. Computer Science & Engineer
- Page 98 and 99: B.Tech. Computer Science & Engineer
- Page 100 and 101: B.Tech. Computer Science & Engineer
- Page 102 and 103: B.Tech. Computer Science & Engineer