B.<strong>Tech</strong>. <strong>Computer</strong> <strong>Science</strong> & <strong>Engineering</strong> (Regular)6. UML: Why we model, types of models, principlesof modelling, object oriented modelling, objectoriented concepts, UML notation, object orientedanalysis: use case diagrams, interaction diagrams,activity diagrams, object oriented design: classdiagrams, object diagrams, state diagrams,collaboration diagrams, post-testing: deploymentdiagrams, patterns, frameworks7. USING UML FOR OOD: UML object constraintlanguage, designing classes: the process, classvisibility, refining attributes, designing methods adprotocols, packages and managing classes,designing interface objects, view layer interfacedesign, macro and micro level interface designprocessTEXT BOOKJacobson Ivar, “Object Oriented Software <strong>Engineering</strong>”,Addison Wesley, 1997.REFERENCE BOOKS1. Bennett, “Object Oriented System Analysis andDesign using UML”, Tata McGraw Hill, 20092. Deacon,” Object Oriented Analysis and Design”,Pearson Education, 20093. Ali Bahrami, “Object Oriented SystemsDevelopment”, McGraw Hill, 19994. Rumbaugh et al, ”Object Oriented Modeling andDesign”, Prentice Hall of India, 20075. Booch Grady, “Object Oriented Analysis andDesign with applications”, 3rd edition, AddisonWesley, 20076. Mehta Subhash and Basandra Suresh K., “ObjectOriented Software <strong>Engineering</strong>”, GalgotiaPublications,1995WEB REFERENCES1. www.objectmentor.com/resources/articles/umlClassDiagrams.pdf2. uml-tutorials.trireme.com3. www.smartdraw.com/tutorials/software/oose/tutorial_01.htm4. www.iconixsw.com5. www.rspa.com/spi/analysismodeling.htmlIT-431BIOINFORMATICSL T P Cr5 0 0 3OBJECTIVEBioinformatics is a rapidly growing field that integratesmolecular biology, biophysics, statistics, and computerscience. Fundamentally it is a field focused oncomparison: how similar are two given proteins? Whatare the differences between various DNA sequences?How is the data from one microarray assay differentfrom another? Furthermore, bioinformatics is concernedwith quantifying the significance of these differences. Inany of the examples above, once a metric for similarityis obtained, it must also be statistically characterized todetermine the likelihood that such a relationship couldoccur by chance. In this course, you will learn many ofthe popular tools for performing bioinformatics analysisand you will be introduced to the thinking that drives thealgorithms.PRE-REQUISITESKnowledge of fundamentals of biology, genetics, datastructures and statistics1. INTRODUCTION TO MOLECULAR BIOLOGY:Gene structure and information content; molecularbiology tools, genomic information content2. COMPUTATIONAL BIOLOGY: Data searches andpairwise alignments; gaps; scoring matrices;Needleman and Wunsch algorithm; global andlocal alignments; database searches.3. PHYLOGENETICS: Molecular phylogenetics;phylogenetic trees; distance matrix methods;character-based methods of phylogenetics;parsimony.4. GENOMICS: Patterns of substitution within genes;estimating substitution numbers; molecular clocks;ancestral sequences; searches; consensus trees;tree confidence; genomics; prokaryotic genestructure; gene density; eukariotic genomes; geneexpression.5. PROTEOMICS: Protein and RNA structureprediction, polypeptic composition, secondary andtertiary structure; algorithms for modeling proteinfolding; structure prediction; proteomics; proteinclassification; experimental techniques; ligandscreening; post-translational modificationprediction.6. GENE EXPRESSION DATA: Microarrays andgene expression data; microarray design; analysisof data; application; microarray standards;clustering (SOM, PCA/SVD, k-means,hierarchical); classification (LVQ, SVM);processing gene expression data using decisiontree based methods (ID3, ASSISTANT, C5.0)7. NEW AREAS OF BIOINFORMATICS:Metabolmics: metabolic pathways; drug targetidentification; biological systems: systems ofmolecular network; eco-systems, elements ofsystems modeling; nutrigenomics;palenteoinformatics; toxicogenomics, systemsbiology; pharmacogenomics, synthetic biology, bioterrorism,biological and chemical warefare, datasecurity issues in bioinformatics, bio-ethics,cloning, transgenic organisms, bio-ethics inagriculture, ontology, standardsTEXT BOOKMount David, “Bioinformatics: Sequence and GenomeAnalysis”, 2008REFERENCE BOOKS1. Attwood T. K. and Parry-Smith D. J., “Introductionto Bioinformatics”, Pearson Education, 20032. Krane D. E. and Raymer M. L., “FundamentalConcepts of Bioinformatics”, Pearson Education,2003.3. Gibas Cynthia, Jambeck Per, “DevelopingBioinformatics Computing Skills”, O’Reilly, 20014. Zar J. H., “Biostatistical Analysis”, 4th edition,Pearson Education, 1999.5. Baldi Pierre and Brunak Søren, “Bioinformatics:The Machine Learning Approach”, 2nd edition, MITPress, 20016. Westhead D. R. et al, “Instant Notes Series:Bioinformatics”, Viva Books Pvt. Ltd., 200362
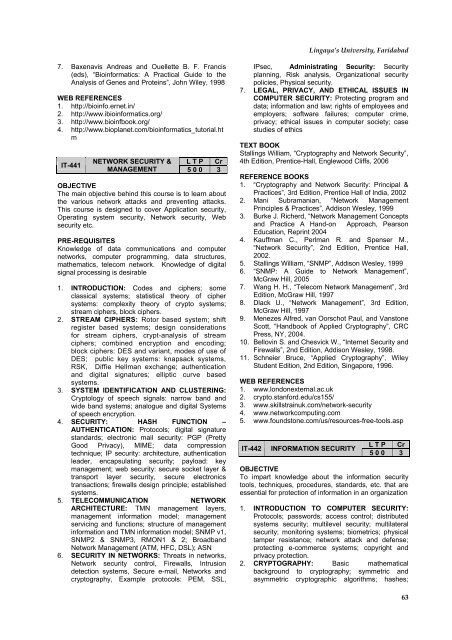
Lingaya’s University, Faridabad7. Baxenavis Andreas and Ouellette B. F. Francis(eds), “Bioinformatics: A Practical Guide to theAnalysis of Genes and Proteins”, John Wiley, 1998WEB REFERENCES1. http://bioinfo.ernet.in/2. http://www.ibioinformatics.org/3. http://www.bioinfbook.org/4. http://www.bioplanet.com/bioinformatics_tutorial.htmIT-441NETWORK SECURITY & L T P CrMANAGEMENT 5 0 0 3OBJECTIVEThe main objective behind this course is to learn aboutthe various network attacks and preventing attacks.This course is designed to cover Application security,Operating system security, Network security, Websecurity etc.PRE-REQUISITESKnowledge of data communications and computernetworks, computer programming, data structures,mathematics, telecom network. Knowledge of digitalsignal processing is desirable1. INTRODUCTION: Codes and ciphers; someclassical systems; statistical theory of ciphersystems: complexity theory of crypto systems;stream ciphers, block ciphers.2. STREAM CIPHERS: Rotor based system; shiftregister based systems; design considerationsfor stream ciphers, crypt-analysis of streamciphers; combined encryption and encoding;block ciphers: DES and variant, modes of use ofDES; public key systems: knapsack systems,RSK, Diffie Hellman exchange; authenticationand digital signatures; elliptic curve basedsystems.3. SYSTEM IDENTIFICATION AND CLUSTERING:Cryptology of speech signals: narrow band andwide band systems; analogue and digital Systemsof speech encryption.4. SECURITY: HASH FUNCTION –AUTHENTICATION: Protocols; digital signaturestandards; electronic mail security: PGP (PrettyGood Privacy), MIME; data compressiontechnique; IP security: architecture, authenticationleader, encapsulating security; payload: keymanagement; web security: secure socket layer &transport layer security, secure electronicstransactions; firewalls design principle; establishedsystems.5. TELECOMMUNICATION NETWORKARCHITECTURE: TMN management layers,management information model; managementservicing and functions; structure of managementinformation and TMN information model; SNMP v1,SNMP2 & SNMP3, RMON1 & 2; BroadbandNetwork Management (ATM, HFC, DSL); ASN6. SECURITY IN NETWORKS: Threats in networks,Network security control, Firewalls, Intrusiondetection systems, Secure e-mail, Networks andcryptography, Example protocols: PEM, SSL,IPsec, Administrating Security: Securityplanning, Risk analysis, Organizational securitypolicies, Physical security.7. LEGAL, PRIVACY, AND ETHICAL ISSUES INCOMPUTER SECURITY: Protecting program anddata; information and law; rights of employees andemployers; software failures; computer crime,privacy; ethical issues in computer society; casestudies of ethicsTEXT BOOKStallings William, “Cryptography and Network Security”,4th Edition, Prentice-Hall, Englewood Cliffs, 2006REFERENCE BOOKS1. “Cryptography and Network Security: Principal &Practices”, 3rd Edition, Prentice Hall of India, 20022. Mani Subramanian, “Network ManagementPrinciples & Practices”, Addison Wesley, 19993. Burke J. Richerd, “Network Management Conceptsand Practice A Hand-on Approach, PearsonEducation, Reprint 20044. Kauffman C., Perlman R. and Spenser M.,“Network Security”, 2nd Edition, Prentice Hall,2002.5. Stallings William, “SNMP”, Addison Wesley, 19996. “SNMP: A Guide to Network Management”,McGraw Hill, 20057. Wang H. H., “Telecom Network Management”, 3rdEdition, McGraw Hill, 19978. Dlack U., “Network Management”, 3rd Edition,McGraw Hill, 19979. Menezes Alfred, van Oorschot Paul, and VanstoneScott, “Handbook of Applied Cryptography”, CRCPress, NY, 2004.10. Bellovin S. and Chesvick W., “Internet Security andFirewalls”, 2nd Edition, Addison Wesley, 1998.11. Schneier Bruce, “Applied Cryptography”, WileyStudent Edition, 2nd Edition, Singapore, 1996.WEB REFERENCES1. www.londonexternal.ac.uk2. crypto.stanford.edu/cs155/3. www.skillstrainuk.com/network-security4. www.networkcomputing.com5. www.foundstone.com/us/resources-free-tools.aspIT-442INFORMATION SECURITYL T P Cr5 0 0 3OBJECTIVETo impart knowledge about the information securitytools, techniques, procedures, standards, etc. that areessential for protection of information in an organization1. INTRODUCTION TO COMPUTER SECURITY:Protocols; passwords; access control; distributedsystems security; multilevel security; multilateralsecurity; monitoring systems; biometrics; physicaltamper resistance; network attack and defense;protecting e-commerce systems; copyright andprivacy protection.2. CRYPTOGRAPHY: Basic mathematicalbackground to cryptography; symmetric andasymmetric cryptographic algorithms; hashes;63
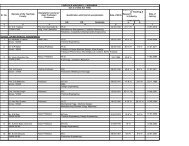
- Page 1:
B.Tech. Degree ProgrammeComputer Sc
- Page 6 and 7:
B.Tech. Computer Science & Engineer
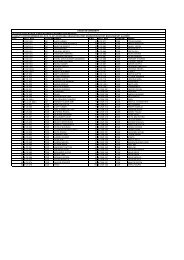
- Page 8 and 9:
B.Tech. Computer Science & Engineer
- Page 10 and 11:
B.Tech. Computer Science & Engineer
- Page 12 and 13:
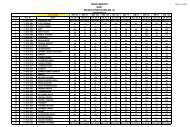
B.Tech. Computer Science & Engineer
- Page 14 and 15:
B.Tech. Computer Science & Engineer
- Page 16 and 17: B.Tech. Computer Science & Engineer
- Page 18 and 19: B.Tech. Computer Science & Engineer
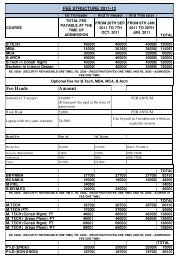
- Page 20 and 21: B.Tech. Computer Science & Engineer
- Page 22 and 23: B.Tech. Computer Science & Engineer
- Page 24 and 25: B.Tech. Computer Science & Engineer
- Page 26 and 27: B.Tech. Computer Science & Engineer
- Page 28 and 29: B.Tech. Computer Science & Engineer
- Page 31 and 32: Lingaya’s University, FaridabadCH
- Page 33 and 34: Lingaya’s University, FaridabadWE
- Page 35 and 36: Lingaya’s University, FaridabadCS
- Page 37 and 38: Lingaya’s University, Faridabad2.
- Page 39 and 40: Lingaya’s University, Faridabadpe
- Page 41 and 42: Lingaya’s University, Faridabad3.
- Page 43 and 44: Lingaya’s University, FaridabadPR
- Page 45 and 46: Lingaya’s University, Faridabadco
- Page 47 and 48: Lingaya’s University, Faridabadar
- Page 49 and 50: Lingaya’s University, Faridabadex
- Page 51 and 52: Lingaya’s University, Faridabad1.
- Page 53 and 54: Lingaya’s University, Faridabad1.
- Page 55 and 56: Lingaya’s University, FaridabadRE
- Page 57 and 58: Lingaya’s University, Faridabad1.
- Page 61 and 62: Lingaya’s University, Faridabad9.
- Page 64 and 65: B.Tech. Computer Science & Engineer
- Page 68 and 69: B.Tech. Computer Science & Engineer
- Page 70 and 71: B.Tech. Computer Science & Engineer
- Page 72 and 73: B.Tech. Computer Science & Engineer
- Page 74 and 75: B.Tech. Computer Science & Engineer
- Page 76 and 77: B.Tech. Computer Science & Engineer
- Page 78 and 79: B.Tech. Computer Science & Engineer
- Page 80 and 81: B.Tech. Computer Science & Engineer
- Page 82 and 83: B.Tech. Computer Science & Engineer
- Page 84 and 85: B.Tech. Computer Science & Engineer
- Page 86 and 87: B.Tech. Computer Science & Engineer
- Page 88 and 89: B.Tech. Computer Science & Engineer
- Page 90 and 91: B.Tech. Computer Science & Engineer
- Page 92 and 93: B.Tech. Computer Science & Engineer
- Page 94 and 95: B.Tech. Computer Science & Engineer
- Page 96 and 97: B.Tech. Computer Science & Engineer
- Page 98 and 99: B.Tech. Computer Science & Engineer
- Page 100 and 101: B.Tech. Computer Science & Engineer
- Page 102 and 103: B.Tech. Computer Science & Engineer