INDEXES register, 2-17, 2-18, 2-21, 2-22, 4-12,7-5thru 7-7, 9-1, 9-6, 9-7, 10-1ESCAPE instructions, 7-4, 12-1 thru 12-5EX (external) bit, 7-2. examples, 2-20 thru 2-26,3-1 thru 3-9, 3-15 thru3-21, 4-15, 5-8, 5-9, 5-13 thru 5-16, 10-3thru 10-15, 11-6 thru 11-8, 11-12 thru11-28exception, 1-7, 2-8, 2-10, 2-17, 4-3, 4-7, 5-5, 6-2,6-4, 6-9, Chapter 7, 9-1, 11-3, 13-3, 13-5handler, 6-7, Chapter 7, 9-2, 9-4, 11-3, 12-4,12-5recovery, Chapter 7, 12-3 thru 12-5EXECUTE, 11-9execute-only segment, 7-7, 13-4expand-down segment, 2-5, 11-11, 13-4expansion direction, 2-5, 5-3EXPORT,11-6export module, 11-6, 11-12, 11-13exports list, 11-4, 11-5extended segmentation controls, 11-4EXTERNAL, 3-6FAR,II-4fault, see exceptionFINIT, 12-5"first fit" algorithm, 3-1, 3-2flag word, 4-2 thru 4-4, 6-2, 6-4, 8-1, 8-2, 10-1FNINIT, 12-2, 12-5FORK,II-9fragmentation, 3-1, 3-2, 9-6FRSTOR,12-4FSAVE, 12-4, 12-5FSETPM, 12-2, 12-5gate, 2-8, 2-11, 11-6call, 2-8,2-10,2-12,2-14,2-15,2-21,3-9,4-13,5-7,5-12,6-1,6-2,8-7,11-3,11-12,11-14interrupt, 2-8, 2-15, 6-2, 6-4, 6-7name, 11-6task, 2-8, 2-14, 2-15, 4-3, 4-7, 6-2, 6-4, 7-5,10-3trap, 2-8, 2-15, 6-2, 6-4, 6-7see also descriptor, gateGATE,II-6GDT, see global descriptor tableGDT register, 2-15, 10-2general protection exception, 7"7, 8-2GEnACCESS$RIGHTS, 13-2GEnSEGMENnLIMIT, 3-6, 13-2global descriptor table (GDT), 1-3,2-12,2-14thru 2-19, 2-22, 3-3, 3-4, 3-7, 3-8, 4-1, 4-3,4-10 thru 4-12,5-1,5-7,5-10,6-7, 7-2, 8-7,10-2, 10-3, 11-2, 11-4, 11-5, 11-9 thru 11-12,13-5handler table, 6-7hashing algorithm, 5-3I bit (of error code), 7-2<strong>iAPX</strong> <strong>286</strong> Binder, 1-10, 11-3, 11-5, 11-6, 11-10,11-11<strong>iAPX</strong> <strong>286</strong> <strong>System</strong> Builder, 1-8 thru 1-11, 2-2,2-4, 2-12, 2-18, 3-1, 3-6, 8-2, 10-3, 11-3 thru11-6, 11-8, 11-10, 11-11<strong>iAPX</strong> 386, 2-3identifier, 5-7, 5-10, 8-7see also interrupt identifierIDT, see interrupt descriptor tableIDT register, 2-15, 6-2IF (interrupt-enable) flag, 4-6, 5.:6, 6-2, 6-4index field (of selector), 2-16,2-17,5-3,7-2INIT$REAL$MATH$UNIT,12-2initializationof 80287, 12-2see also system initializationinput/output (1/0),1-4 thru 1-7,2-18,4-5,4-7,4-10,5-10, Chapter 8, 9-2, 9-4, 9-8, 11-2,11-4, 11-9indirect, 8-3memory-mapped, 8-2IN,8-1INS, 7-7, 8-1INT, 2-7, 2-10, 2-15, 4-3, 6-1, 6-2, 7-3INT A cycles, 2-15INTO, 6-1, 6-2, 7-3INTR pin, 6-1, 6-2, 6-6interrupt, 1-4, 1-7,2-10,2-15,2-21,4-3,5-4 thru5-6, Chapter 6, 7-1, 7-6, 7-7, 8-4, 10-1,10-2distribution, 6-7 thru 6-9flag, see IFidentifier, 2-15, 6-1, 6-2handler, 2-15, 2-18, 4-6latency, see interrupt response timemask, 4-7, 12-4procedure, 4-4, 4-7, 4-11, 4-13, 6-2, 6-4 thru6-7, 7-1, 12-4response time, 4-3, 5-5, 6-5, 12-4scheduled task, see schedulingsoftware, 6-1task, 4-4, 4-7, 6-2, 6-4 thru 6-6, 7-1, 7-6, 9-4,12-4, 13-5interrupt descriptor table (IDT), 2-12, 2-15,2-16,2-18,4-3,4-5,4-7,6-2,6-4,6-5,6-7,7-2, 7-5, 10-2, 10-3, 11-11Index-2 121960-001
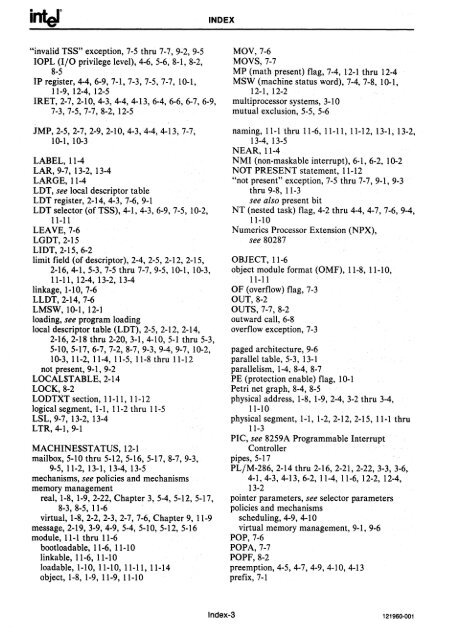
INDEX"invalid TSS" exception, 7-5 thru 7-7, 9-2, 9-510PL (I/O privilege level), 4-6, 5-6, 8-1, 8-2,8-5IP register, 4-4, 6-9, 7-1, 7-3, 7-5, 7-7, 10-1,11-9, 12-4, 12-5IRET, 2-7, 2-10, 4-3, 4-4, 4-13, 6-4, 6-6, 6-7, 6-9,7-3,7-5,7-7,8-2,12-5JMP, 2-5, 2-7, 2-9, 2-10, 4-3, 4-4, 4-13, 7-7,10-1, 10-3LABEL,11-4LAR, 9-7, 13-2, 13-4LARGE,11-4LDT, see local descriptor tableLDT register, 2-14, 4-3, 7-6, 9-1LDT selector (of TSS), 4-1, 4-3, 6-9, 7-5, 10-2,11-11LEAVE,7-6LGDT,2-15LIDT, 2-15, 6-2limit field (of descriptor), 2-4, 2-5, 2-12, 2-15,2-16,4-1,5-3,7-5 thru 7-7, 9-5, 10-1, 10-3,11-11,12-4,13-2,13-4linkage, 1-10, 7-6LLDT, 2-14, 7-6LMSW, 10-1,12-1loading, see program loadinglocal descriptor table (LDT), 2-5, 2-12, 2-14,2-16,2-18 thru 2-20, 3-1, 4-10, 5-1 thru 5-3,5-10,5-17,6-7,7-2,8-7,9-3,9-4,9-7,10-2,10-3, 11-2, 11-4, 11-5, 11-8 thru 11-12not present, 9-1, 9-2LOCAUTABLE,2-14LOCK,8-2LODTXT section, 11-11, 11-12logical segment, 1-1, 11-2 thru 11-5Lst, 9-7, 13-2, 13-4LTR, 4-1,9-1MACHINE$STATUS, 12-1mailbox, 5-10 thru 5-12, 5-16, 5-17, 8-7, 9-3,9-5, 11-2, 13-1, 13-4, 13-5mechanisms, see policies and mechanismsmemory managementreal, 1-8, 1-9,2-22, Chapter 3,5-4,5-12,5-17,8-3, 8-5, 11-6virtual, 1-8,2-2,2-3,2-7,7-6, Chapter 9, 11-9message, 2-19, 3-9, 4-9, 5-4, 5-10, 5-12, 5-16module, 11-1 thru 11-6bootloadable, 11-6, 11-10linkable, 11-6, 11-10load able, 1-10, 11-10, 11-11, 11-14object, 1-8, 1-9, 11-9, 11-10MOV, 7-6MOVS, 7-7MP (math present) flag, 7-4, 12-1 thru 12-4MSW (machine status word), 7-4, 7-8, 10-1,12-1, 12-2multiprocessor systems, 3-10mutual exclusion, 5-5, 5-6naming, 11-1 thru 11-6, 11-11, 11-12, 13-1, 13-2,13-4, 13-5NEAR,II-4NMI (non-maskable interrupt), 6-1, 6-2, 10-2NOT PRESENT statement, 11-12"not present" exception, 7-5 thru 7-7,9-1,9-3thru 9-8, 11-3see also present bitNT (nested task) flag, 4-2 thru 4-4, 4-7, 7-6, 9-4,11-10Numerics Processor Extension (NPX),see 80287OBJECT, 11-6object module format (OMF), 11-8, 11-10,11-11OF (overflow) flag, 7-3OUT,8-2OUTS, 7-7, 8-2outward call, 6-8overflow exception, 7-3paged architecture, 9-6parallel table, 5-3, 13-1parallelism. 1-4, 8-4, 8-7PE (protection enable) flag, 10-1Petri net graph, 8-4, 8-5physical address, 1-8, 1-9,2-4,3-2 thru 3-4,11-10physical segment, 1-1, 1-2,2-12,2-15, 11-1 thru11-3PIC, see 8259A Programmable InterruptControllerpipes, 5-17PL/M-<strong>286</strong>, 2-14 thru 2-16, 2-21, 2-22, 3-3, 3-6,4-1, 4c3, 4-13, 6-2, 11-4, 11-6, 12-2, 12-4,13-2pointer parameters, see selector parameterspolicies and mechanismsscheduling, 4-9, 4-10virtual memory management, 9-1, 9-6POP, 7-6POPA,7-7POPF,8-2preemption, 4-5, 4-7, 4-9, 4-10, 4-13prefix, 7-1Index-3 121960-001
- Page 2 and 3:
LITERATUREIn addition to the produc
- Page 4 and 5:
Intel Corporation makes no warranty
- Page 6 and 7:
PREFACEExternal LiteratureMany aspe
- Page 8:
Table of ContentsCHAPTER 1PageINTRO
- Page 11 and 12:
TABLE OF CONTENTSCHAPTER 9PageVIRTU
- Page 13 and 14:
TABLE OF CONTENTSLIST OF FIGURESFig
- Page 15:
Introduction to Protected 1Multitas
- Page 18 and 19:
INTRODUCTION TO PROTECTED MULTITASK
- Page 20 and 21:
inter INTRODUCTION TO PROTECTED MUL
- Page 22 and 23:
111'eI INTRODUCTION TO PROTECTED MU
- Page 24 and 25:
INTRODUCTION TO PROTECTED MULTITASK
- Page 26 and 27:
INTRODUCTION TO PROTECTED MULTITASK
- Page 29:
Using Hardware2Protection Features
- Page 32 and 33:
USING HARDWARE PROTECTION,FEATURESs
- Page 34 and 35:
interUSING HARDWARE PROTECTION FEAT
- Page 36 and 37:
USING HARDWARE PROTECTION FEATURES(
- Page 38 and 39:
USING HARDWARE PROTECTION FEATURES
- Page 40 and 41:
USING HARDWARE PROTECTION FEATUREST
- Page 42 and 43:
USING HARDWARE PROTECTION FEATURESo
- Page 44 and 45:
USING HARDWARE PROTECTION FEATURESL
- Page 46 and 47:
USING HARDWARE PROTECTION FEATUREST
- Page 48 and 49:
USING HARDWARE PROTECTION FEATURESE
- Page 50 and 51:
inl:el~USING HARDWARE PROTECTION FE
- Page 52 and 53:
IntelUSING HARDWARE PROTECTION FEAT
- Page 54 and 55:
IntelU~ING HARDWARE PROTECTION FEAT
- Page 56 and 57:
lSLDTFORMATRt;;SERV~~"O~iA~~.~ijij
- Page 59 and 60:
CHAPTER 3REAL MEMORY MANAGEMENTIn d
- Page 61 and 62:
REAL MEMORY MANAGEMENTIALLOCATEGATE
- Page 63 and 64:
interREAL MEMORY MANAGEMENTBEFOREAF
- Page 65 and 66:
REAL MEMORY MANAGEMENTGLOBAL DESCRI
- Page 67 and 68:
REAL MEMORY MANAGEMENTTable 3-1. Ac
- Page 69 and 70:
REAL MEMORY MANAGEMENTBEFOREI "FREE
- Page 71 and 72:
REAL MEMORY MANAGEMENTBEFOREI "FREE
- Page 73 and 74:
REAL MEMORY MANAGEMENTPL/M-286 COMP
- Page 75 and 76:
REAL MEMORY MANAGEMENTPL/M-286 COMP
- Page 77 and 78:
REAL MEMORY MANAGEMENTPL/M-286 COMP
- Page 79:
REAL MEMORY MANAGEMENTPL/M-286 COMP
- Page 82 and 83:
IIIIIIIIIIIIIIIIIIIIII
- Page 84 and 85:
II I telTASK MANAGEMENTCPUTASK REGI
- Page 86 and 87:
TASK MANAGEMENTIf the proc~sser, wh
- Page 88 and 89:
TASK MANAGEMENTUsually, termination
- Page 90 and 91:
TASK MANAGEMENTTASK XTSS TSS TSS TS
- Page 92 and 93:
TASK MANAGEMENTSCHEDULING POLICIEST
- Page 94 and 95:
TASK MANAGEMENTThe example in figur
- Page 96 and 97:
TASK MANAGEMENTREADY QUEUESBY PRIOR
- Page 98 and 99:
IIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIII
- Page 101 and 102:
CHAPTER 5DATA SHARING, ALIASING, AN
- Page 103 and 104:
DATA SHARING, ALIASING, AND SYNCHRO
- Page 105 and 106:
interDATA SHARING, ALIASING, AND SV
- Page 107 and 108:
DATA SHARING, ALIASING, AND SYNCHRO
- Page 109 and 110:
DATA SHARING, ALIASING, AND SYNCHRO
- Page 111 and 112:
DATA SHARING, ALIASING, AND SYNCHRO
- Page 113 and 114:
DATA SHARING, ALIASING, AND SYNCHRO
- Page 115 and 116:
DATA SHARING, ALIASING, AND SYNCHRO
- Page 117:
DATA SHARING, ALIASING, AND SYNCHRO
- Page 121 and 122:
CHAPTER 6SIGNALS AND INTERRUPTSInte
- Page 123 and 124:
interSIGNALS AND INTERRUPTSlOTGOTTS
- Page 125 and 126:
SIGNALS AND INTERRUPTSTable 6-1. In
- Page 127 and 128:
SIGNALS AND INTERRUPTSSend interrup
- Page 129 and 130:
SIGNALS AND INTERRUPTSprocedure suc
- Page 131:
Handling Exception Conditions 7
- Page 134 and 135:
HANDLING EXCEPTION CONDITIONSError
- Page 136 and 137:
HANDLING EXCEPTION CONDITIONSAn exc
- Page 138 and 139:
HANDLING EXCEPTION CONDITIONSA few
- Page 140 and 141:
HANDLING EXCEPTION CONDITIONSAn ins
- Page 143 and 144:
CHAPTER 8INPUT /OUTPUTMany of the c
- Page 145 and 146:
INPUT /OUTPUTYou can still take adv
- Page 147 and 148:
INPUT /OUTPUT• Only the operating
- Page 149:
INPUT /OUTPUTtask the I/0 procedure
- Page 153 and 154:
CHAPTER 9VIRTUAL MEMORYThe memory l
- Page 155 and 156:
VIRTUAL MEMORYthose segments that a
- Page 157 and 158:
VIRTUAL MEMORY• Return the RAM sp
- Page 159 and 160:
VIRTUAL MEMORYReplacementThe operat
- Page 161 and 162:
System Initialization10
- Page 163 and 164:
CHAPTER 10SYSTEM INITIALIZATIONThe
- Page 165 and 166:
SYSTEM INITIALIZATIONStarting the f
- Page 167 and 168:
iAPX286 "ACRO ASSEMBLERLOCOBJEnter
- Page 169 and 170:
iAPX286 MACRO ASSEMBLEtEnter Protec
- Page 171 and 172:
iAPX286 MACRO ASSEMBLER·· Enter ~
- Page 173 and 174:
iAPX286 'UCRO USE148LER Ente,. P,.o
- Page 175 and 176:
iAPX286 MACRO ASSEMBLEREnt9~ P~otec
- Page 177:
iAPX286 MACRO ASSEMBLE~ INITIAL TAS
- Page 181 and 182:
CHAPTER 11BINDING AND LOADINGBindin
- Page 183 and 184:
BINDING AND LOADINGNamingThe names
- Page 185 and 186:
BINDING AND LOADING$ COMPACT (NUCLE
- Page 187 and 188:
interBINDING AND LOADINGsystem-IDiA
- Page 189 and 190: BIND.ING AND LOADINGConverting a Pr
- Page 191 and 192: BINDING AND LOADINGThe OMF of each
- Page 193 and 194: interBINDING AND LOADINGsystem-IDiA
- Page 195 and 196: BINDING AND LOADINGPL/M-2B6 COMPILE
- Page 197 and 198: BINDING AND LOADI.NGPL/M-286 COMPIL
- Page 199 and 200: BINDING AND LOADINGPL/M-286 COMPILE
- Page 201 and 202: BINDING AND LOADINGPL/M-2B6 COMPILE
- Page 203 and 204: BINDING AND LOAD.INGPL/M-286 COMPIL
- Page 205 and 206: interBINDING AND LOADINGPL/M-286 CO
- Page 207 and 208: BINDING AND LOADINGPL/M-286 COMPILE
- Page 209: Numerics Processor Extension 12
- Page 212 and 213: NUMERICS PROCESSOR EXTENSIONMath Pr
- Page 214 and 215: interNUMERICS PROCESSOR EXTENSION
- Page 217: Extended Protection13
- Page 220 and 221: EXTENDED PROTECTIONIndirect NamingT
- Page 222 and 223: EXTENDED PROTECTIONanother procedur
- Page 225: Glossary
- Page 228 and 229: GLOSSARYbootloadable module: a modu
- Page 230 and 231: GLOSSARYexception: a processor-dete
- Page 232 and 233: GLOSSARYintersegment reference: a r
- Page 234 and 235: GLOSSARYoutward call: the attempt t
- Page 236 and 237: GLOSSARYscheduling state: one of se
- Page 238 and 239: GLOSSARYvirtual address: an address
- Page 242 and 243: INDEXpresent bit, 2-2, 2-3, 2-9, 5-
- Page 245 and 246: interu.s. SALES OFFICESALAIWIA IlEQ
- Page 247 and 248: interu.s. DISTRIBUTORSNEW YORK (C"n
- Page 249 and 250: intJINTEL INTERNATIONAL SALES OFFIC