Getting Started with WebSphere Application Server
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Chapter 8 – Security 149<br />
8.3 Implementing security in a Java EE application<br />
In general, access to a secured Java EE resource requires the validation of credentials (user<br />
ID/password) against the user registry. The user registry by itself does not enforce any security policies or<br />
constraints (authorization); it simply validates the supplied user, group, and password information by the<br />
Java EE authentication mechanisms.<br />
Role-based security allows a developer to secure access to Java EE resources based on roles. Often a<br />
developer has no knowledge of the users and groups that will exist at runtime; by using roles, he can<br />
grant or revoke access to a specific artifact. Later, an administrator can map these roles to actual users<br />
and groups.<br />
Java EE has two forms of role-based security:<br />
• Declarative security, where the security rules are defined in the deployment descriptors and the<br />
Java EE runtime manages access to the Java EE artifact. A user will see all or none of a<br />
resource.<br />
• Programmatic security, where the program determines the role of a user and grants access to<br />
different resources depending on this role. The user may only see a subset of a resource<br />
depending on his role.<br />
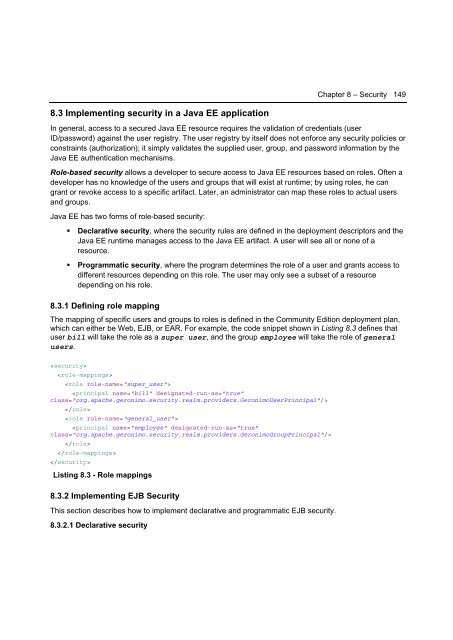
8.3.1 Defining role mapping<br />
The mapping of specific users and groups to roles is defined in the Community Edition deployment plan,<br />
which can either be Web, EJB, or EAR. For example, the code snippet shown in Listing 8.3 defines that<br />
user bill will take the role as a super user, and the group employee will take the role of general<br />
users.<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
Listing 8.3 - Role mappings<br />
8.3.2 Implementing EJB Security<br />
This section describes how to implement declarative and programmatic EJB security.<br />
8.3.2.1 Declarative security