BATTLEFIELD DIGITAL FORENSICS
BDF_Battlefield_Digital_Forensics_final
BDF_Battlefield_Digital_Forensics_final
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
4<br />
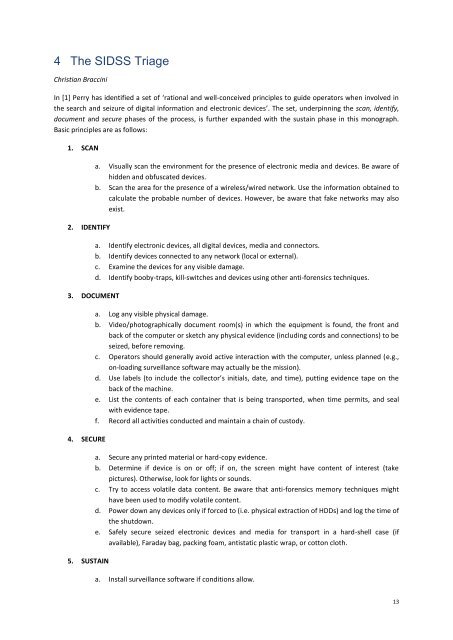
The SIDSS Triage<br />
Christian Braccini<br />
In [1] Perry has identified a set of ‘rational and well-conceived principles to guide operators when involved in<br />
the search and seizure of digital information and electronic devices’. The set, underpinning the scan, identify,<br />
document and secure phases of the process, is further expanded with the sustain phase in this monograph.<br />
Basic principles are as follows:<br />
1. SCAN<br />
2. IDENTIFY<br />
3. DOCUMENT<br />
4. SECURE<br />
5. SUSTAIN<br />
a. Visually scan the environment for the presence of electronic media and devices. Be aware of<br />
hidden and obfuscated devices.<br />
b. Scan the area for the presence of a wireless/wired network. Use the information obtained to<br />
calculate the probable number of devices. However, be aware that fake networks may also<br />
exist.<br />
a. Identify electronic devices, all digital devices, media and connectors.<br />
b. Identify devices connected to any network (local or external).<br />
c. Examine the devices for any visible damage.<br />
d. Identify booby-traps, kill-switches and devices using other anti-forensics techniques.<br />
a. Log any visible physical damage.<br />
b. Video/photographically document room(s) in which the equipment is found, the front and<br />
back of the computer or sketch any physical evidence (including cords and connections) to be<br />
seized, before removing.<br />
c. Operators should generally avoid active interaction with the computer, unless planned (e.g.,<br />
on-loading surveillance software may actually be the mission).<br />
d. Use labels (to include the collector’s initials, date, and time), putting evidence tape on the<br />
back of the machine.<br />
e. List the contents of each container that is being transported, when time permits, and seal<br />
with evidence tape.<br />
f. Record all activities conducted and maintain a chain of custody.<br />
a. Secure any printed material or hard-copy evidence.<br />
b. Determine if device is on or off; if on, the screen might have content of interest (take<br />
pictures). Otherwise, look for lights or sounds.<br />
c. Try to access volatile data content. Be aware that anti-forensics memory techniques might<br />
have been used to modify volatile content.<br />
d. Power down any devices only if forced to (i.e. physical extraction of HDDs) and log the time of<br />
the shutdown.<br />
e. Safely secure seized electronic devices and media for transport in a hard-shell case (if<br />
available), Faraday bag, packing foam, antistatic plastic wrap, or cotton cloth.<br />
a. Install surveillance software if conditions allow.<br />
13