BATTLEFIELD DIGITAL FORENSICS
BDF_Battlefield_Digital_Forensics_final
BDF_Battlefield_Digital_Forensics_final
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
1<br />
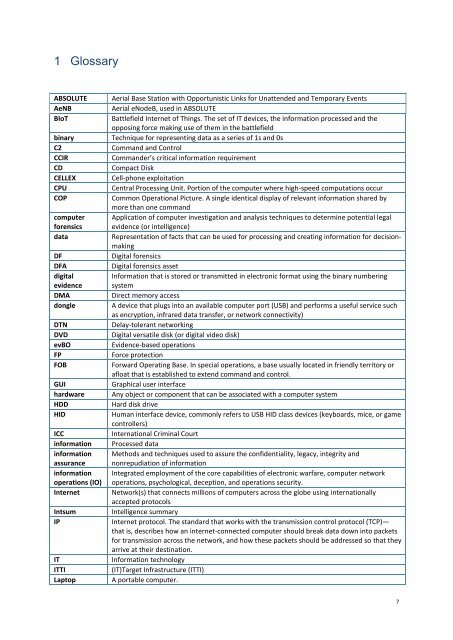
Glossary<br />
ABSOLUTE<br />
AeNB<br />
BIoT<br />
binary<br />
C2<br />
CCIR<br />
CD<br />
CELLEX<br />
CPU<br />
COP<br />
computer<br />
forensics<br />
data<br />
DF<br />
DFA<br />
digital<br />
evidence<br />
DMA<br />
dongle<br />
DTN<br />
DVD<br />
evBO<br />
FP<br />
FOB<br />
GUI<br />
hardware<br />
HDD<br />
HID<br />
ICC<br />
information<br />
information<br />
assurance<br />
information<br />
operations (IO)<br />
Internet<br />
Intsum<br />
IP<br />
IT<br />
ITTI<br />
Laptop<br />
Aerial Base Station with Opportunistic Links for Unattended and Temporary Events<br />
Aerial eNodeB, used in ABSOLUTE<br />
Battlefield Internet of Things. The set of IT devices, the information processed and the<br />
opposing force making use of them in the battlefield<br />
Technique for representing data as a series of 1s and 0s<br />
Command and Control<br />
Commander’s critical information requirement<br />
Compact Disk<br />
Cell-phone exploitation<br />
Central Processing Unit. Portion of the computer where high-speed computations occur<br />
Common Operational Picture. A single identical display of relevant information shared by<br />
more than one command<br />
Application of computer investigation and analysis techniques to determine potential legal<br />
evidence (or intelligence)<br />
Representation of facts that can be used for processing and creating information for decisionmaking<br />
Digital forensics<br />
Digital forensics asset<br />
Information that is stored or transmitted in electronic format using the binary numbering<br />
system<br />
Direct memory access<br />
A device that plugs into an available computer port (USB) and performs a useful service such<br />
as encryption, infrared data transfer, or network connectivity)<br />
Delay-tolerant networking<br />
Digital versatile disk (or digital video disk)<br />
Evidence-based operations<br />
Force protection<br />
Forward Operating Base. In special operations, a base usually located in friendly territory or<br />
afloat that is established to extend command and control.<br />
Graphical user interface<br />
Any object or component that can be associated with a computer system<br />
Hard disk drive<br />
Human interface device, commonly refers to USB HID class devices (keyboards, mice, or game<br />
controllers)<br />
International Criminal Court<br />
Processed data<br />
Methods and techniques used to assure the confidentiality, legacy, integrity and<br />
nonrepudiation of information<br />
Integrated employment of the core capabilities of electronic warfare, computer network<br />
operations, psychological, deception, and operations security.<br />
Network(s) that connects millions of computers across the globe using internationally<br />
accepted protocols<br />
Intelligence summary<br />
Internet protocol. The standard that works with the transmission control protocol (TCP)—<br />
that is, describes how an internet-connected computer should break data down into packets<br />
for transmission across the network, and how these packets should be addressed so that they<br />
arrive at their destination.<br />
Information technology<br />
(IT)Target Infrastructure (ITTI)<br />
A portable computer.<br />
7