BATTLEFIELD DIGITAL FORENSICS
BDF_Battlefield_Digital_Forensics_final
BDF_Battlefield_Digital_Forensics_final
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
e observed. However, solutions for preventing the enemy from pulling out an USB flash drive from the<br />
computer might be limited.<br />
7.6.3 USB Killer<br />
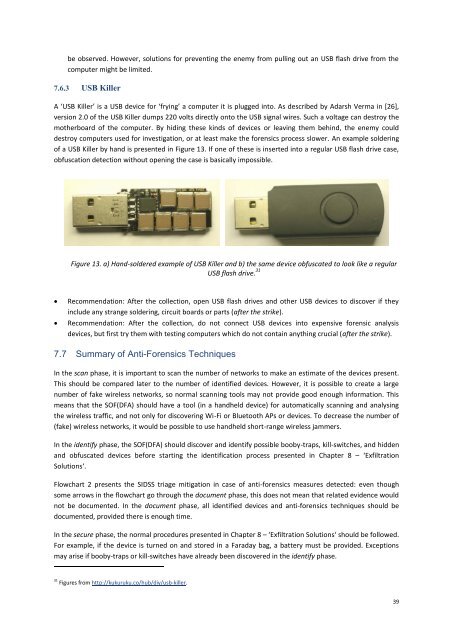
A ‘USB Killer’ is a USB device for ‘frying’ a computer it is plugged into. As described by Adarsh Verma in [26],<br />
version 2.0 of the USB Killer dumps 220 volts directly onto the USB signal wires. Such a voltage can destroy the<br />
motherboard of the computer. By hiding these kinds of devices or leaving them behind, the enemy could<br />
destroy computers used for investigation, or at least make the forensics process slower. An example soldering<br />
of a USB Killer by hand is presented in Figure 13. If one of these is inserted into a regular USB flash drive case,<br />
obfuscation detection without opening the case is basically impossible.<br />
Figure 13. a) Hand-soldered example of USB Killer and b) the same device obfuscated to look like a regular<br />
USB flash drive. 31<br />
<br />
<br />
Recommendation: After the collection, open USB flash drives and other USB devices to discover if they<br />
include any strange soldering, circuit boards or parts (after the strike).<br />
Recommendation: After the collection, do not connect USB devices into expensive forensic analysis<br />
devices, but first try them with testing computers which do not contain anything crucial (after the strike).<br />
7.7 Summary of Anti-Forensics Techniques<br />
In the scan phase, it is important to scan the number of networks to make an estimate of the devices present.<br />
This should be compared later to the number of identified devices. However, it is possible to create a large<br />
number of fake wireless networks, so normal scanning tools may not provide good enough information. This<br />
means that the SOF(DFA) should have a tool (in a handheld device) for automatically scanning and analysing<br />
the wireless traffic, and not only for discovering Wi-Fi or Bluetooth APs or devices. To decrease the number of<br />
(fake) wireless networks, it would be possible to use handheld short-range wireless jammers.<br />
In the identify phase, the SOF(DFA) should discover and identify possible booby-traps, kill-switches, and hidden<br />
and obfuscated devices before starting the identification process presented in Chapter 8 – ‘Exfiltration<br />
Solutions‘.<br />
Flowchart 2 presents the SIDSS triage mitigation in case of anti-forensics measures detected: even though<br />
some arrows in the flowchart go through the document phase, this does not mean that related evidence would<br />
not be documented. In the document phase, all identified devices and anti-forensics techniques should be<br />
documented, provided there is enough time.<br />
In the secure phase, the normal procedures presented in Chapter 8 – ‘Exfiltration Solutions‘ should be followed.<br />
For example, if the device is turned on and stored in a Faraday bag, a battery must be provided. Exceptions<br />
may arise if booby-traps or kill-switches have already been discovered in the identify phase.<br />
31 Figures from http://kukuruku.co/hub/diy/usb-killer.<br />
39