Draft27-12
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
News<br />
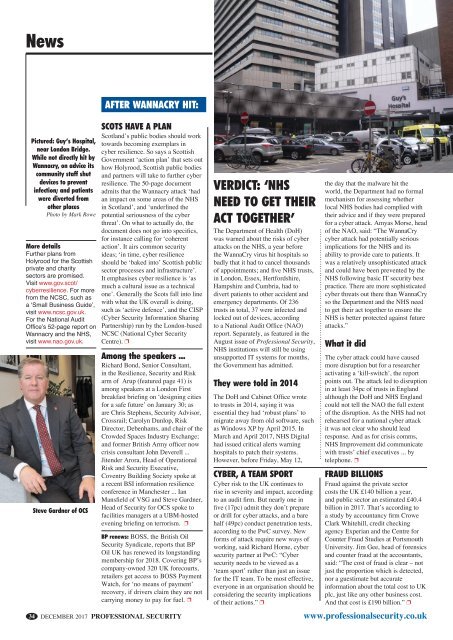
Pictured: Guy’s Hospital,<br />
near London Bridge.<br />
While not directly hit by<br />
Wannacry, on advice its<br />
community staff shut<br />
devices to prevent<br />
infection; and patients<br />
were diverted from<br />
other places<br />
Photo by Mark Rowe<br />
More details<br />
Further plans from<br />
Holyrood for the Scottish<br />
private and charity<br />
sectors are promised.<br />
Visit www.gov.scot/<br />
cyberresilience. For more<br />
from the NCSC, such as<br />
a ‘Small Business Guide’,<br />
visit www.ncsc.gov.uk.<br />
For the National Audit<br />
Office’s 52-page report on<br />
Wannacry and the NHS,<br />
visit www.nao.gov.uk.<br />
Steve Gardner of OCS<br />
after wannacry hit:<br />
SCOTS HAVE A PLAN<br />
Scotland’s public bodies should work<br />
towards becoming exemplars in<br />
cyber resilience. So says a Scottish<br />
Government ‘action plan’ that sets out<br />
how Holyrood, Scottish public bodies<br />
and partners will take to further cyber<br />
resilience. The 50-page document<br />
admits that the Wannacry attack ‘had<br />
an impact on some areas of the NHS<br />
in Scotland’, and ‘underlined the<br />
potential seriousness of the cyber<br />
threat’. On what to actually do, the<br />
document does not go into specifics,<br />
for instance calling for ‘coherent<br />
action’. It airs common security<br />
ideas; ‘in time, cyber resilience<br />
should be ‘baked into’ Scottish public<br />
sector processes and infrastructure’.<br />
It emphasises cyber resilience is ‘as<br />
much a cultural issue as a technical<br />
one’. Generally the Scots fall into line<br />
with what the UK overall is doing,<br />
such as ‘active defence’, and the CISP<br />
(Cyber Security Information Sharing<br />
Partnership) run by the London-based<br />
NCSC (National Cyber Security<br />
Centre). p<br />
Among the speakers ...<br />
Richard Bond, Senior Consultant,<br />
in the Resilience, Security and Risk<br />
arm of Arup (featured page 41) is<br />
among speakers at a London First<br />
breakfast briefing on ‘designing cities<br />
for a safe future’ on January 30; as<br />
are Chris Stephens, Security Advisor,<br />
Crossrail; Carolyn Dunlop, Risk<br />
Director, Debenhams, and chair of the<br />
Crowded Spaces Industry Exchange;<br />
and former British Army officer now<br />
crisis consultant John Deverell ...<br />
Jitender Arora, Head of Operational<br />
Risk and Security Executive,<br />
Coventry Building Society spoke at<br />
a recent BSI information resilience<br />
conference in Manchester ... Ian<br />
Mansfield of VSG and Steve Gardner,<br />
Head of Security for OCS spoke to<br />
facilities managers at a UBM-hosted<br />
evening briefing on terrorism. p<br />
BP renews: BOSS, the British Oil<br />
Security Syndicate, reports that BP<br />
Oil UK has renewed its longstanding<br />
membership for 2018. Covering BP’s<br />
company-owned 320 UK forecourts,<br />
retailers get access to BOSS Payment<br />
Watch, for ‘no means of payment’<br />
recovery, if drivers claim they are not<br />
carrying money to pay for fuel. p<br />
VERDICT: ‘NHS<br />
NEED TO GET THEIR<br />
ACT TOGETHER’<br />
The Department of Health (DoH)<br />
was warned about the risks of cyber<br />
attacks on the NHS, a year before<br />
the WannaCry virus hit hospitals so<br />
badly that it had to cancel thousands<br />
of appointments; and five NHS trusts,<br />
in London, Essex, Hertfordshire,<br />
Hampshire and Cumbria, had to<br />
divert patients to other accident and<br />
emergency departments. Of 236<br />
trusts in total, 37 were infected and<br />
locked out of devices, according<br />
to a National Audit Office (NAO)<br />
report. Separately, as featured in the<br />
August issue of Professional Security,<br />
NHS institutions will still be using<br />
unsupported IT systems for months,<br />
the Government has admitted.<br />
They were told in 2014<br />
The DoH and Cabinet Office wrote<br />
to trusts in 2014, saying it was<br />
essential they had ‘robust plans’ to<br />
migrate away from old software, such<br />
as Windows XP by April 2015. In<br />
March and April 2017, NHS Digital<br />
had issued critical alerts warning<br />
hospitals to patch their systems.<br />
However, before Friday, May <strong>12</strong>,<br />
CYBER, A TEAM SPORT<br />
Cyber risk to the UK continues to<br />
rise in severity and impact, according<br />
to an audit firm. But nearly one in<br />
five (17pc) admit they don’t prepare<br />
or drill for cyber attacks, and a bare<br />
half (49pc) conduct penetration tests,<br />
according to the PwC survey. New<br />
forms of attack require new ways of<br />
working, said Richard Horne, cyber<br />
security partner at PwC: “Cyber<br />
security needs to be viewed as a<br />
‘team sport’ rather than just an issue<br />
for the IT team. To be most effective,<br />
everyone in an organisation should be<br />
considering the security implications<br />
of their actions.” p<br />
the day that the malware hit the<br />
world, the Department had no formal<br />
mechanism for assessing whether<br />
local NHS bodies had complied with<br />
their advice and if they were prepared<br />
for a cyber attack. Amyas Morse, head<br />
of the NAO, said: “The WannaCry<br />
cyber attack had potentially serious<br />
implications for the NHS and its<br />
ability to provide care to patients. It<br />
was a relatively unsophisticated attack<br />
and could have been prevented by the<br />
NHS following basic IT security best<br />
practice. There are more sophisticated<br />
cyber threats out there than WannaCry<br />
so the Department and the NHS need<br />
to get their act together to ensure the<br />
NHS is better protected against future<br />
attacks.”<br />
What it did<br />
The cyber attack could have caused<br />
more disruption but for a researcher<br />
activating a ‘kill-switch’, the report<br />
points out. The attack led to disruption<br />
in at least 34pc of trusts in England<br />
although the DoH and NHS England<br />
could not tell the NAO the full extent<br />
of the disruption. As the NHS had not<br />
rehearsed for a national cyber attack<br />
it was not clear who should lead<br />
response. And as for crisis comms,<br />
NHS Improvement did communicate<br />
with trusts’ chief executives ... by<br />
telephone. p<br />
Fraud billions<br />
Fraud against the private sector<br />
costs the UK £140 billion a year,<br />
and public sector an estimated £40.4<br />
billion in 2017. That’s according to<br />
a study by accountancy firm Crowe<br />
Clark Whitehill, credit checking<br />
agency Experian and the Centre for<br />
Counter Fraud Studies at Portsmouth<br />
University. Jim Gee, head of forensics<br />
and counter fraud at the accountants,<br />
said: “The cost of fraud is clear – not<br />
just the proportion which is detected,<br />
nor a guestimate but accurate<br />
information about the total cost to UK<br />
plc, just like any other business cost.<br />
And that cost is £190 billion.” p<br />
34 DECEMBER 2017 PROFESSIONAL SECURITY www.professionalsecurity.co.uk<br />
p34 News 27-<strong>12</strong>.indd 1 18/11/2017 14:43