Installation and configuration manual - Alcatel-Lucent Eye-box Support
Installation and configuration manual - Alcatel-Lucent Eye-box Support
Installation and configuration manual - Alcatel-Lucent Eye-box Support
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Chapter 6 <br />
synchronization.<br />
This operation will retrieve the user information from Active Directory <strong>and</strong> create the users in<br />
the Extended Communication Server base group. The retrieved information are:<br />
- User login<br />
- User first name<br />
- User last name<br />
- Phone number<br />
- Mobile phone number<br />
- Email addresses<br />
Once the first synchronization is done, you can activate the daily synchronization process<br />
which will repeat the operation described above.<br />
6.3.2.4 Deactivated Account<br />
This list presents user accounts deleted or deactivated in the external directory. They have<br />
been deactivated on the Extended Communication Server server. They will be activated again<br />
if the account is reactivated or recreated in the external directory. They are available in this<br />
interface so that they can be deleted by the administrator.<br />
6.3.3 User Connection<br />
6.3.3.1 User Authentication<br />
Users authenticate to the Extended Communication Server services by using their usual Active<br />
Directory login/password.<br />
The first time, the Extended Communication Server forwards the authentication request to the<br />
Active Directory server <strong>and</strong> saves locally the encrypted password.<br />
If the user is successfully authenticated, any following requests are h<strong>and</strong>le directly by the<br />
Extended Communication Server until the user password is changed.<br />
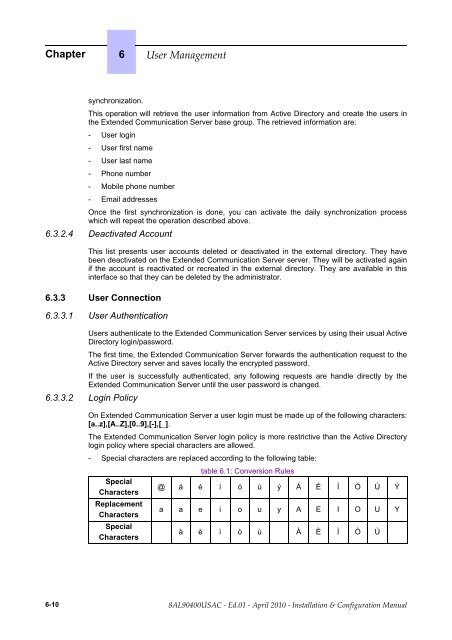
6.3.3.2 Login Policy<br />
On Extended Communication Server a user login must be made up of the following characters:<br />
[a..z],[A..Z],[0..9],[-],[_].<br />
The Extended Communication Server login policy is more restrictive than the Active Directory<br />
login policy where special characters are allowed.<br />
- Special characters are replaced according to the following table:<br />
Special<br />
Characters<br />
Replacement<br />
Characters<br />
Special<br />
Characters<br />
table 6.1: Conversion Rules<br />
@ á é í ó ú ý Á É Í Ó Ú Ý<br />
a a e i o u y A E I O U Y<br />
à è ì ò ù À È Ì Ò Ù<br />
6-10