Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
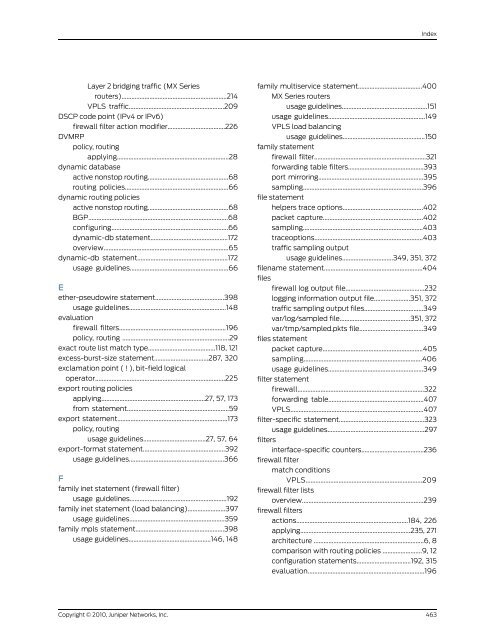
Index<br />
Layer 2 bridging traffic (MX Series<br />
routers)................................................................214<br />
VPLS traffic..........................................................209<br />
DSCP code point (IPv4 or IPv6)<br />
DVMRP<br />
firewall filter action modifier...................................226<br />
policy, routing<br />
applying....................................................................28<br />
dynamic database<br />
active nonstop routing.................................................68<br />
routing policies...............................................................66<br />
dynamic routing policies<br />
active nonstop routing.................................................68<br />
BGP.....................................................................................68<br />
configuring.......................................................................66<br />
dynamic-db statement...............................................172<br />
overview............................................................................65<br />
dynamic-db statement.......................................................172<br />
usage guidelines............................................................66<br />
E<br />
ether-pseudowire statement..........................................398<br />
usage guidelines...........................................................148<br />
evaluation<br />
firewall filters.................................................................196<br />
policy, routing .................................................................29<br />
exact route list match type.........................................118, 121<br />
excess-burst-size statement.................................287, 320<br />
exclamation point ( ! ), bit-field logical<br />
operator...............................................................................225<br />
export routing policies<br />
applying...............................................................27, 57, 173<br />
from statement..............................................................59<br />
export statement...................................................................173<br />
policy, routing<br />
usage guidelines......................................27, 57, 64<br />
export-format statement..................................................392<br />
usage guidelines..........................................................366<br />
F<br />
family inet statement (firewall filter)<br />
usage guidelines...........................................................192<br />
family inet statement (load balancing).......................397<br />
usage guidelines..........................................................359<br />
family mpls statement......................................................398<br />
usage guidelines..................................................146, 148<br />
family multiservice statement.......................................400<br />
MX Series routers<br />
usage guidelines....................................................151<br />
usage guidelines...........................................................149<br />
VPLS load balancing<br />
usage guidelines..................................................150<br />
family statement<br />
firewall filter....................................................................321<br />
forwarding table filters..............................................393<br />
port mirroring................................................................395<br />
sampling.........................................................................396<br />
file statement<br />
helpers trace options.................................................402<br />
packet capture.............................................................402<br />
sampling.........................................................................403<br />
traceoptions..................................................................403<br />
traffic sampling output<br />
usage guidelines...............................349, 351, 372<br />
filename statement............................................................404<br />
files<br />
firewall log output file................................................232<br />
logging information output file......................351, 372<br />
traffic sampling output files....................................349<br />
var/log/sampled file...........................................351, 372<br />
var/tmp/sampled.pkts file.......................................349<br />
files statement<br />
packet capture.............................................................405<br />
sampling........................................................................406<br />
usage guidelines..........................................................349<br />
filter statement<br />
firewall.............................................................................322<br />
forwarding table..........................................................407<br />
VPLS.................................................................................407<br />
filter-specific statement....................................................323<br />
usage guidelines...........................................................297<br />
filters<br />
interface-specific counters......................................236<br />
firewall filter<br />
match conditions<br />
VPLS.......................................................................209<br />
firewall filter lists<br />
overview..........................................................................239<br />
firewall filters<br />
actions....................................................................184, 226<br />
applying...................................................................235, 271<br />
architecture ...................................................................6, 8<br />
comparison with routing policies ........................9, 12<br />
configuration statements.................................192, 315<br />
evaluation.......................................................................196<br />
Copyright © 2010, <strong>Juniper</strong> <strong>Networks</strong>, Inc.<br />
463