Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
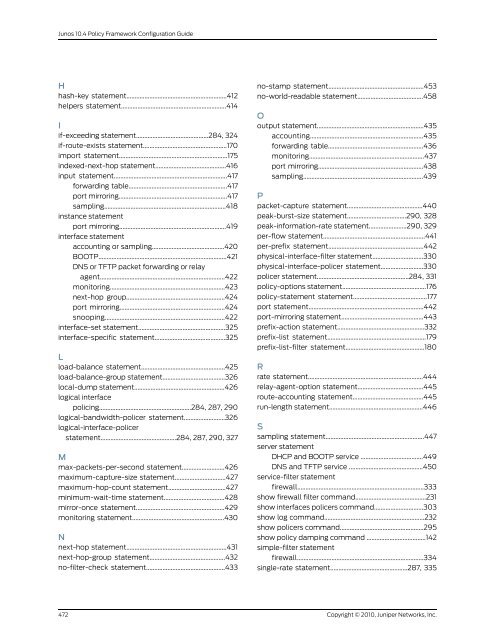
Junos 10.4 <strong>Policy</strong> <strong>Framework</strong> <strong>Configuration</strong> <strong>Guide</strong><br />
H<br />
hash-key statement.............................................................412<br />
helpers statement................................................................414<br />
I<br />
if-exceeding statement............................................284, 324<br />
if-route-exists statement...................................................170<br />
import statement..................................................................175<br />
indexed-next-hop statement...........................................416<br />
input statement.....................................................................417<br />
forwarding table............................................................417<br />
port mirroring..................................................................417<br />
sampling..........................................................................418<br />
instance statement<br />
port mirroring.................................................................419<br />
interface statement<br />
accounting or sampling............................................420<br />
BOOTP..............................................................................421<br />
DNS or TFTP packet forwarding or relay<br />
agent............................................................................422<br />
monitoring......................................................................423<br />
next-hop group............................................................424<br />
port mirroring................................................................424<br />
snooping.........................................................................422<br />
interface-set statement.....................................................325<br />
interface-specific statement...........................................325<br />
L<br />
load-balance statement...................................................425<br />
load-balance-group statement......................................326<br />
local-dump statement.......................................................426<br />
logical interface<br />
policing........................................................284, 287, 290<br />
logical-bandwidth-policer statement.........................326<br />
logical-interface-policer<br />
statement..............................................284, 287, 290, 327<br />
M<br />
max-packets-per-second statement..........................426<br />
maximum-capture-size statement...............................427<br />
maximum-hop-count statement...................................427<br />
minimum-wait-time statement.....................................428<br />
mirror-once statement......................................................429<br />
monitoring statement........................................................430<br />
N<br />
next-hop statement.............................................................431<br />
next-hop-group statement..............................................432<br />
no-filter-check statement................................................433<br />
no-stamp statement..........................................................453<br />
no-world-readable statement........................................458<br />
O<br />
output statement.................................................................435<br />
accounting.....................................................................435<br />
forwarding table..........................................................436<br />
monitoring......................................................................437<br />
port mirroring................................................................438<br />
sampling.........................................................................439<br />
P<br />
packet-capture statement..............................................440<br />
peak-burst-size statement....................................290, 328<br />
peak-information-rate statement.......................290, 329<br />
per-flow statement..............................................................441<br />
per-prefix statement..........................................................442<br />
physical-interface-filter statement...............................330<br />
physical-interface-policer statement..........................330<br />
policer statement........................................................284, 331<br />
policy-options statement...................................................176<br />
policy-statement statement.............................................177<br />
port statement......................................................................442<br />
port-mirroring statement..................................................443<br />
prefix-action statement.....................................................332<br />
prefix-list statement............................................................179<br />
prefix-list-filter statement................................................180<br />
R<br />
rate statement......................................................................444<br />
relay-agent-option statement........................................445<br />
route-accounting statement...........................................445<br />
run-length statement.........................................................446<br />
S<br />
sampling statement............................................................447<br />
server statement<br />
DHCP and BOOTP service ......................................449<br />
DNS and TFTP service .............................................450<br />
service-filter statement<br />
firewall.............................................................................333<br />
show firewall filter command...........................................231<br />
show interfaces policers command..............................303<br />
show log command.............................................................232<br />
show policers command...................................................295<br />
show policy damping command ....................................142<br />
simple-filter statement<br />
firewall.............................................................................334<br />
single-rate statement...............................................287, 335<br />
472<br />
Copyright © 2010, <strong>Juniper</strong> <strong>Networks</strong>, Inc.