Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
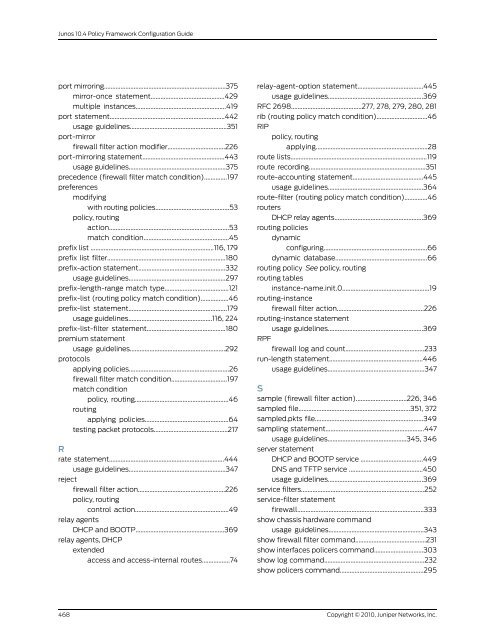
Junos 10.4 <strong>Policy</strong> <strong>Framework</strong> <strong>Configuration</strong> <strong>Guide</strong><br />
port mirroring..........................................................................375<br />
mirror-once statement.............................................429<br />
multiple instances.......................................................419<br />
port statement......................................................................442<br />
usage guidelines...........................................................351<br />
port-mirror<br />
firewall filter action modifier...................................226<br />
port-mirroring statement..................................................443<br />
usage guidelines...........................................................375<br />
precedence (firewall filter match condition)..............197<br />
preferences<br />
modifying<br />
with routing policies.............................................53<br />
policy, routing<br />
action.........................................................................53<br />
match condition....................................................45<br />
prefix list ...........................................................................116, 179<br />
prefix list filter........................................................................180<br />
prefix-action statement.....................................................332<br />
usage guidelines...........................................................297<br />
prefix-length-range match type.......................................121<br />
prefix-list (routing policy match condition).................46<br />
prefix-list statement............................................................179<br />
usage guidelines...................................................116, 224<br />
prefix-list-filter statement................................................180<br />
premium statement<br />
usage guidelines..........................................................292<br />
protocols<br />
applying policies.............................................................26<br />
firewall filter match condition..................................197<br />
match condition<br />
routing<br />
policy, routing.........................................................46<br />
applying policies...................................................64<br />
testing packet protocols.............................................217<br />
R<br />
rate statement......................................................................444<br />
reject<br />
usage guidelines...........................................................347<br />
firewall filter action.....................................................226<br />
policy, routing<br />
relay agents<br />
control action.........................................................49<br />
DHCP and BOOTP......................................................369<br />
relay agents, DHCP<br />
extended<br />
access and access-internal routes.................74<br />
relay-agent-option statement........................................445<br />
usage guidelines..........................................................369<br />
RFC 2698...........................................277, 278, 279, 280, 281<br />
rib (routing policy match condition)...............................46<br />
RIP<br />
policy, routing<br />
applying....................................................................28<br />
route lists...................................................................................119<br />
route recording.......................................................................351<br />
route-accounting statement...........................................445<br />
usage guidelines..........................................................364<br />
route-filter (routing policy match condition)..............46<br />
routers<br />
DHCP relay agents......................................................369<br />
routing policies<br />
dynamic<br />
configuring...............................................................66<br />
dynamic database........................................................66<br />
routing policy See policy, routing<br />
routing tables<br />
instance-name.init.0.....................................................19<br />
routing-instance<br />
firewall filter action.....................................................226<br />
routing-instance statement<br />
RPF<br />
usage guidelines..........................................................369<br />
firewall log and count................................................233<br />
run-length statement.........................................................446<br />
usage guidelines...........................................................347<br />
S<br />
sample (firewall filter action)...............................226, 346<br />
sampled file....................................................................351, 372<br />
sampled.pkts file..................................................................349<br />
sampling statement............................................................447<br />
usage guidelines................................................345, 346<br />
server statement<br />
DHCP and BOOTP service ......................................449<br />
DNS and TFTP service .............................................450<br />
usage guidelines..........................................................369<br />
service filters...........................................................................252<br />
service-filter statement<br />
firewall.............................................................................333<br />
show chassis hardware command<br />
usage guidelines..........................................................343<br />
show firewall filter command...........................................231<br />
show interfaces policers command..............................303<br />
show log command.............................................................232<br />
show policers command...................................................295<br />
468<br />
Copyright © 2010, <strong>Juniper</strong> <strong>Networks</strong>, Inc.