Cryptology - Unofficial St. Mary's College of California Web Site
Cryptology - Unofficial St. Mary's College of California Web Site
Cryptology - Unofficial St. Mary's College of California Web Site
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
116 CHAPTER 7.<br />
VIGENÈRE CIPHERS<br />
2. Each ambassador, messenger and spy could have their own key that could<br />
be changed easily if stolen or lost. (Generally the keywords were phrases,<br />
i.e., “God save the Queen”.)<br />
It did, however, have the reputation for being cumbersome and prone to error,<br />
which meant it was used less than one would otherwise expect. Even so, it<br />
served as a prototype for many ciphers used by pr<strong>of</strong>essionals.<br />
7.5 Variants and Beaufort<br />
In 1857 Admiral Sir Francis Beaufort <strong>of</strong> the Royal Navy (known for his scale <strong>of</strong><br />
wind speed) and his brother published what they thought was a new cipher. 10<br />
They put their Beaufort Tableaux (Figure 7.2) on 4×5-inch cards and sold these<br />
as a new way <strong>of</strong> secret writing “adapted for telegrams and postcards” (postcards<br />
having recently been invented).<br />
To use the card, they wrote<br />
Let the key for the foregoing [message] be a line <strong>of</strong> poetry or the name<br />
<strong>of</strong> some memorable person or place, which cannot easily be forgotten ...<br />
Now look in the side column for the first letter <strong>of</strong> the text (t) and run<br />
the eye across the table until it comes to the first letter <strong>of</strong> the key (v),<br />
then at the top <strong>of</strong> the column in which v stands will be found the letter<br />
c. ([Kahn], page 202.)<br />
So the plainletter t is enciphered by V to give the cipherletter C. (Actually, one<br />
can look either up or down to find the ciphertext.) Clearly this cipher method<br />
is very closely related to the Vigenère cipher. It does have one small advantage:<br />
deciphering is exactly the same process as enciphering.<br />
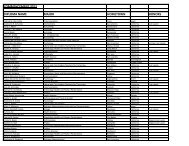
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z<br />
B C D E F G H I J K L M N O P Q R S T U V W X Y Z A<br />
C D E F G H I J K L M N O P Q R S T U V W X Y Z A B<br />
D E F G H I J K L M N O P Q R S T U V W X Y Z A B C<br />
E F G H I J K L M N O P Q R S T U V W X Y Z A B C D<br />
F G H I J K L M N O P Q R S T U V W X Y Z A B C D E<br />
G H I J K L M N O P Q R S T U V W X Y Z A B C D E F<br />
H I J K L M N O P Q R S T U V W X Y Z A B C D E F G<br />
I J K L M N O P Q R S T U V W X Y Z A B C D E F G H<br />
J K L M N O P Q R S T U V W X Y Z A B C D E F G H I<br />
K L M N O P Q R S T U V W X Y Z A B C D E F G H I J<br />
L M N O P Q R S T U V W X Y Z A B C D E F G H I J K<br />
M N O P Q R S T U V W X Y Z A B C D E F G H I J K L<br />
N O P Q R S T U V W X Y Z A B C D E F G H I J K L M<br />
O P Q R S T U V W X Y Z A B C D E F G H I J K L M N<br />
P Q R S T U V W X Y Z A B C D E F G H I J K L M N O<br />
Q R S T U V W X Y Z A B C D E F G H I J K L M N O P<br />
R S T U V W X Y Z A B C D E F G H I J K L M N O P Q<br />
S T U V W X Y Z A B C D E F G H I J K L M N O P Q R<br />
T U V W X Y Z A B C D E F G H I J K L M N O P Q R S<br />
U V W X Y Z A B C D E F G H I J K L M N O P Q R S T<br />
V W X Y Z A B C D E F G H I J K L M N O P Q R S T U<br />
W X Y Z A B C D E F G H I J K L M N O P Q R S T U V<br />
X Y Z A B C D E F G H I J K L M N O P Q R S T U V W<br />
Y Z A B C D E F G H I J K L M N O P Q R S T U V W X<br />
Z A B C D E F G H I J K L M N O P Q R S T U V W X Y<br />
Figure 7.2: Beaufort’s Tableaux<br />
10 It had already been studied by Giovanni Sestri in 1710.