Cryptology - Unofficial St. Mary's College of California Web Site
Cryptology - Unofficial St. Mary's College of California Web Site
Cryptology - Unofficial St. Mary's College of California Web Site
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
118 CHAPTER 7.<br />
VIGENÈRE CIPHERS<br />
unbreakable. So how finally was the Vigenère Cipher broken By turning the<br />
power <strong>of</strong> the keyword against the cipher.<br />
Let’s start by backing up. What enabled us to decrypt a Caesar cipher<br />
We knew that every letter in the message was enciphered using the same key<br />
letter. And we could detect this key letter from the frequency habits <strong>of</strong> normal<br />
English. Why can’t we do this with a Vigenère cipher Because not all <strong>of</strong> the<br />
letters are enciphered using the same key letter. In other words, a Caesar cipher<br />
is monoalphabetic, a Vigenère cipher is polyalphabetic.<br />
Now suppose we did know which letters were enciphered by the same letters<br />
<strong>of</strong> the keyword. Then we could split up the ciphertext into groups in such a way<br />
that all the letters in each group would be enciphered with the same keyletter.<br />
Each group <strong>of</strong> letters would be like a (different) Caesar cipher. And we know<br />
how to break Caesar ciphers. Since we could decrypt each <strong>of</strong> these groups <strong>of</strong><br />
letters, then we could decrypt all <strong>of</strong> the letters in the ciphertext, thus breaking<br />
the message.<br />
So (perhaps) we don’t actually need to know the keyword, but we do need to<br />
determine which ciphertext letters have been enciphered with the same letter <strong>of</strong><br />
the keyword. How can we do this Imagine rewriting the ciphertext downward<br />
into columns, with as many letters per column as there are letters in the keyword.<br />
Of course, we’d need to know how many letters there are in the keyword,<br />
but pretend for a moment we know that. Then the letters in the first row <strong>of</strong> our<br />
re-written ciphertext would all have been enciphered using the first letter <strong>of</strong> the<br />
keyword. And the letters in the second row <strong>of</strong> the re-written ciphertext would<br />
all have been enciphered using the second letter <strong>of</strong> the keyword. Similarly for<br />
the other rows. We would be left with several Caesar ciphers to break.<br />
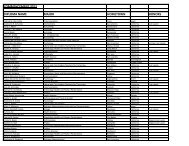
To make this a bit less abstract, let’s suppose the keyword contained 5<br />
letters, and we number them k 1 k 2 k 3 k 4 k 5 , and similarly number the ciphertext<br />
letters ct 1 ct 2 ct 3 · · · . Then the complex <strong>of</strong> rows and columns from the previous<br />
paragraph takes the form<br />
k 1 ct 1 ct 6 ct 11 ct 16 . . .<br />
k 2 ct 2 ct 7 ct 12 ct 17 . . .<br />
k 3 ct 3 ct 8 ct 13 ct 18 . . .<br />
k 4 ct 4 ct 9 ct 14 ct 19 . . .<br />
k 5 ct 5 ct 0 ct 15 ct 10 . . .<br />
The letters ct 1 , ct 6 , ct 11 , ct 16 , . . . all have been enciphered by the key k 1 . So we<br />
can treat ct 1 ct 6 ct 11 ct 16 . . . as a Caesar cipher with unknown key k 1 . Likewise,<br />
ct 2 , ct 7 , ct 12 , ct 17 , . . . all have been enciphered by k 2 , so ct 2 ct 7 ct 12 ct 17 . . . can<br />
be treated as a Caesar cipher.<br />
So to decrypt a Vigenère-enciphered message, assuming we know the length<br />
<strong>of</strong> the keyword, first rewrite the ciphertext in columns with as many letters per<br />
column as letters in the keyword. Then the letters <strong>of</strong> each row will constitute a<br />
Caesar cipher that can be broken with our techniques from Chapter 1.<br />
To summarize, from what does the Vigenère cipher get its security Ob-