Cryptology - Unofficial St. Mary's College of California Web Site
Cryptology - Unofficial St. Mary's College of California Web Site
Cryptology - Unofficial St. Mary's College of California Web Site
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
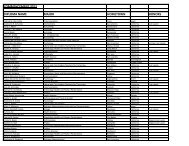
4.5. BREAKING DECIMATION AND LINEAR CIPHERS 65<br />
(4) Decipher JWNIC G. It was enciphered with the Linear Cipher 13m + 4<br />
modulo 33.<br />
Ok, now we do need Euclid’s algorithm:<br />
q<br />
r<br />
c<br />
33<br />
0<br />
2<br />
13<br />
1<br />
1<br />
7<br />
−2<br />
1<br />
6<br />
3<br />
6<br />
1<br />
−5<br />
0<br />
Since −5%33 = 28 the inverse <strong>of</strong> 13 is 28.<br />
subtracting by 4 and multiplying by 28. 5<br />
Now we may proceed by<br />
⋄ ⋄ ⋄ ⋄ ⋄ ⋄ ⋄ ⋄ ⋄ ⋄ ⋄ ⋄<br />
As one last example, recall from Chapter 3 that the Kid-RSA cipher has<br />
as public information an enciphering key e and modulus n. In order for this<br />
cipher to be worthwhile, it must be infeasible for an adversary to compute the<br />
secret deciphering key d from the public keys e and n. Because <strong>of</strong> the Euclidean<br />
Algorithm, not only is computing d not infeasible, it is simple.<br />
To illustrate, if Albert has published e = 893 and n = 8106 as his public<br />
keys, we simply compute gcd(8106, 893):<br />
q<br />
r<br />
c<br />
8106<br />
0<br />
9<br />
893<br />
1<br />
12<br />
69<br />
−9<br />
1<br />
65<br />
109<br />
16<br />
4<br />
−118<br />
4<br />
1<br />
1997<br />
0<br />
So in a very few steps, the “secret” deciphering key is d = 1997. Even though<br />
there is no real security in Koblitz’s system, it did allow us to introduce the<br />
important concepts related to public keys.<br />
4.5 Breaking Decimation and Linear Ciphers<br />
Earlier we saw that decimation and linear ciphers cause letters which are adjacent<br />
in the plaintext alphabet to be separated in the ciphertext alphabet. How<br />
much does this improve security Consider the ciphertext from Section 3.5 that<br />
was enciphered with a linear cipher.<br />
UQESF YFTGW SGPVS PPVQX QEDGR PMQFP YJSFG EORVQ DQBQF PVQWO<br />
MRTQW PUOTT SPPOM QWOFE TIXQS FIMLQ DYJUY FXQDO FCW<br />
It has the following letter frequency table.<br />
5 cipher.<br />
0 1 1 4 4 9 4 0 2 2 0 1 4 0 6 9 13 3 6 5 3 4 5 3 4 0<br />
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z