Cryptology - Unofficial St. Mary's College of California Web Site
Cryptology - Unofficial St. Mary's College of California Web Site
Cryptology - Unofficial St. Mary's College of California Web Site
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
3.3. DECIMATION CIPHERS 41<br />
previous about face example shows that decimation ciphers apparently will<br />
not have this weakness. The adjacent letters ef and tu were enciphered to YD<br />
and VA, respectively, and the adjacent triple abc to EJO. In fact, if we go ahead<br />
and encipher the entire alphabet with key k = 5 we find the following cipher<br />
alphabet:<br />
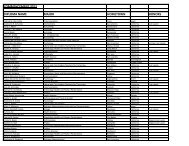
plaintext<br />
ciphertext<br />
a b c d e f g h i j k l m n o p q r s t u v w x y z<br />
E J O T Y D I N S X C H M R W B G L Q V A F K P U Z<br />
None <strong>of</strong> the letters are next to their former neighbors. 9 Decimation ciphers<br />
destroy letter ordering!<br />
We have not explained how to “properly” choose our keynumbers, but to see<br />
that there must be some care taken consider enciphering anna or bob using a<br />
decimation cipher with k = 2. The ciphertexts are BBBB and DDD, respectively.<br />
How would anyone decipher BBBB It is impossible to tell which B is an a and<br />
which is an n. So no one would be able to decipher a message whose enciphering<br />
key was 2. Hence, only certain keys can be used to multiply. In this chapter<br />
you will be given only proper keys, so we can safely put <strong>of</strong>f solving this problem<br />
until Chapter 4.<br />
Thus far we have enciphered letters and only letters. What if we wish to<br />
keep spacing Or to add punctuation in our messages The next examples will<br />
do that.<br />
Examples:<br />
(1) Work modulo 28 with key k = 5 to encipher a space here. Use the usual<br />
plainnumbers with the addition that = 27, where the symbol means<br />
“space”.<br />
We do this as we did before, being careful to find the remainders using 28<br />
rather than 26.<br />
plaintext a s p a c e h e r e<br />
plain numbers 1 27 19 16 1 3 5 27 8 5 18 5<br />
multiplied numbers 5 135 95 80 5 15 25 135 40 25 90 25<br />
%28 5 23 11 24 5 15 25 23 12 25 6 25<br />
ciphertext E W K X E O Y W L Y F Y<br />
The answer is EQAXE OYWLY FY.<br />
(2) Encipher no one here using the same method with key k = 9.<br />
9 The careful reader may notice an oddity in the last plaintext–ciphertext alphabet pair.<br />
(If you didn’t, try enciphering zzz using any key before reading further.) Since we think <strong>of</strong><br />
a as the first letter <strong>of</strong> the alphabet, z is the 26th. But 26 times any keynumber will be a<br />
multiple <strong>of</strong> 26, and so when divided by 26 it will have a remainder <strong>of</strong> 0. Since 0 is just before<br />
1, 0 must represent Z. Hence, z will always be enciphered into Z. Fortunately z is uncommon<br />
enough that this doesn’t really threaten the security <strong>of</strong> this cipher.