Deze scriptie is geschreven door beide op persoonlijke titel
IT-control framework voor de Douanevereenvoudiging Self ... - Vurore
IT-control framework voor de Douanevereenvoudiging Self ... - Vurore
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
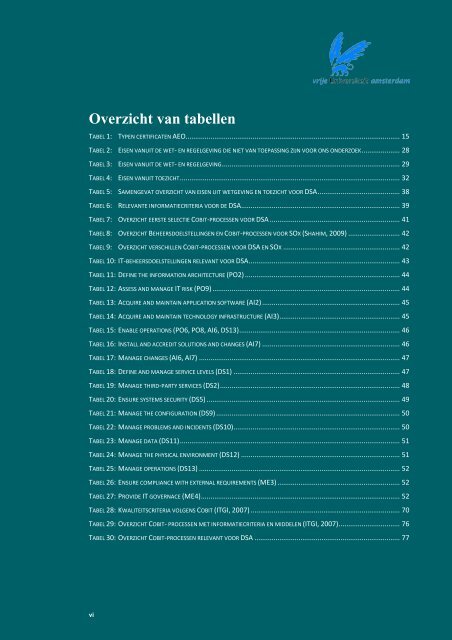
Overzicht van tabellenTABEL 1: TYPEN CERTIFICATEN AEO................................................................................................................ 15TABEL 2: EISEN VANUIT DE WET- EN REGELGEVING DIE NIET VAN TOEPASSING ZIJN VOOR ONS ONDERZOEK .................... 28TABEL 3: EISEN VANUIT DE WET- EN REGELGEVING ............................................................................................. 29TABEL 4: EISEN VANUIT TOEZICHT ................................................................................................................... 32TABEL 5: SAMENGEVAT OVERZICHT VAN EISEN UIT WETGEVING EN TOEZICHT VOOR DSA ........................................... 38TABEL 6: RELEVANTE INFORMATIECRITERIA VOOR DE DSA................................................................................... 39TABEL 7: OVERZICHT EERSTE SELECTIE COBIT-PROCESSEN VOOR DSA .................................................................... 41TABEL 8: OVERZICHT BEHEERSDOELSTELLINGEN EN COBIT-PROCESSEN VOOR SOX (SHAHIM, 2009) ........................... 42TABEL 9: OVERZICHT VERSCHILLEN COBIT-PROCESSEN VOOR DSA EN SOX ............................................................. 42TABEL 10: IT-BEHEERSDOELSTELLINGEN RELEVANT VOOR DSA ............................................................................... 43TABEL 11: DEFINE THE INFORMATION ARCHITECTURE (PO2) ................................................................................. 44TABEL 12: ASSESS AND MANAGE IT RISK (PO9) .................................................................................................. 44TABEL 13: ACQUIRE AND MAINTAIN APPLICATION SOFTWARE (AI2) ........................................................................ 45TABEL 14: ACQUIRE AND MAINTAIN TECHNOLOGY INFRASTRUCTURE (AI3)............................................................... 45TABEL 15: ENABLE OPERATIONS (PO6, PO8, AI6, DS13) .................................................................................... 46TABEL 16: INSTALL AND ACCREDIT SOLUTIONS AND CHANGES (AI7) ........................................................................ 46TABEL 17: MANAGE CHANGES (AI6, AI7) ......................................................................................................... 47TABEL 18: DEFINE AND MANAGE SERVICE LEVELS (DS1) ....................................................................................... 47TABEL 19: MANAGE THIRD-PARTY SERVICES (DS2).............................................................................................. 48TABEL 20: ENSURE SYSTEMS SECURITY (DS5) ..................................................................................................... 49TABEL 21: MANAGE THE CONFIGURATION (DS9) ................................................................................................ 50TABEL 22: MANAGE PROBLEMS AND INCIDENTS (DS10)....................................................................................... 50TABEL 23: MANAGE DATA (DS11)................................................................................................................... 51TABEL 24: MANAGE THE PHYSICAL ENVIRONMENT (DS12) ................................................................................... 51TABEL 25: MANAGE OPERATIONS (DS13) ......................................................................................................... 52TABEL 26: ENSURE COMPLIANCE WITH EXTERNAL REQUIREMENTS (ME3) ................................................................ 52TABEL 27: PROVIDE IT GOVERNACE (ME4)........................................................................................................ 52TABEL 28: KWALITEITSCRITERIA VOLGENS COBIT (ITGI, 2007) .............................................................................. 70TABEL 29: OVERZICHT COBIT- PROCESSEN MET INFORMATIECRITERIA EN MIDDELEN (ITGI, 2007) ................................ 76TABEL 30: OVERZICHT COBIT-PROCESSEN RELEVANT VOOR DSA ............................................................................ 77vi