Cyber Primer
AEWhbF
AEWhbF
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Fundamentals of cyber<br />
cyber and cyberspace-dependent capabilities, 7 on the other hand, could<br />
have severe consequences, including loss of life and could equate to a kinetic<br />
attack.<br />
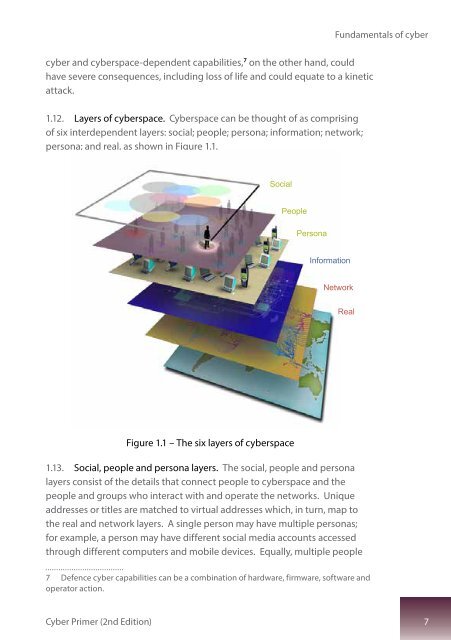
1.12. Layers of cyberspace. <strong>Cyber</strong>space can be thought of as comprising<br />
of six interdependent layers: social; people; persona; information; network;<br />
persona; and real, as shown in Figure 1.1.<br />
Social<br />
People<br />
Persona<br />
Information<br />
Network<br />
Real<br />
Figure 1.1 – The six layers of cyberspace<br />
1.13. Social, people and persona layers. The social, people and persona<br />
layers consist of the details that connect people to cyberspace and the<br />
people and groups who interact with and operate the networks. Unique<br />
addresses or titles are matched to virtual addresses which, in turn, map to<br />
the real and network layers. A single person may have multiple personas;<br />
for example, a person may have different social media accounts accessed<br />
through different computers and mobile devices. Equally, multiple people<br />
7 Defence cyber capabilities can be a combination of hardware, firmware, software and<br />
operator action.<br />
<strong>Cyber</strong> <strong>Primer</strong> (2nd Edition) 7