My Reading on ASQ CQA HB Part I-IA~IE-s
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
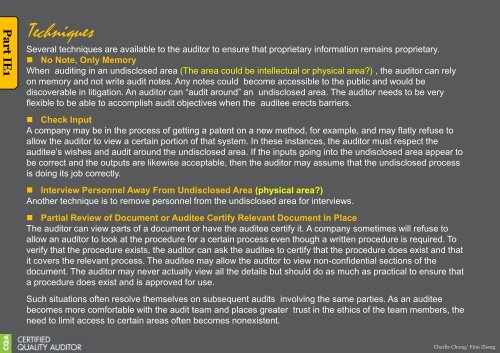
<strong>Part</strong> IE1<br />
Techniques<br />
Several techniques are available to the auditor to ensure that proprietary informati<strong>on</strong> remains proprietary.<br />
• No Note, Only Memory<br />
When auditing in an undisclosed area (The area could be intellectual or physical area?) , the auditor can rely<br />
<strong>on</strong> memory and not write audit notes. Any notes could become accessible to the public and would be<br />
discoverable in litigati<strong>on</strong>. An auditor can ―audit around‖ an undisclosed area. The auditor needs to be very<br />
flexible to be able to accomplish audit objectives when the auditee erects barriers.<br />
• Check Input<br />
A company may be in the process of getting a patent <strong>on</strong> a new method, for example, and may flatly refuse to<br />
allow the auditor to view a certain porti<strong>on</strong> of that system. In these instances, the auditor must respect the<br />
auditee’s wishes and audit around the undisclosed area. If the inputs going into the undisclosed area appear to<br />
be correct and the outputs are likewise acceptable, then the auditor may assume that the undisclosed process<br />
is doing its job correctly.<br />
• Interview Pers<strong>on</strong>nel Away From Undisclosed Area (physical area?)<br />
Another technique is to remove pers<strong>on</strong>nel from the undisclosed area for interviews.<br />
• <strong>Part</strong>ial Review of Document or Auditee Certify Relevant Document in Place<br />
The auditor can view parts of a document or have the auditee certify it. A company sometimes will refuse to<br />
allow an auditor to look at the procedure for a certain process even though a written procedure is required. To<br />
verify that the procedure exists, the auditor can ask the auditee to certify that the procedure does exist and that<br />
it covers the relevant process. The auditee may allow the auditor to view n<strong>on</strong>-c<strong>on</strong>fidential secti<strong>on</strong>s of the<br />
document. The auditor may never actually view all the details but should do as much as practical to ensure that<br />
a procedure does exist and is approved for use.<br />
Such situati<strong>on</strong>s often resolve themselves <strong>on</strong> subsequent audits involving the same parties. As an auditee<br />
becomes more comfortable with the audit team and places greater trust in the ethics of the team members, the<br />
need to limit access to certain areas often becomes n<strong>on</strong>existent.<br />
Charlie Ch<strong>on</strong>g/ Fi<strong>on</strong> Zhang