Webwasher 6.0.1 Anti-Malware User's Guide - McAfee
Webwasher 6.0.1 Anti-Malware User's Guide - McAfee
Webwasher 6.0.1 Anti-Malware User's Guide - McAfee
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
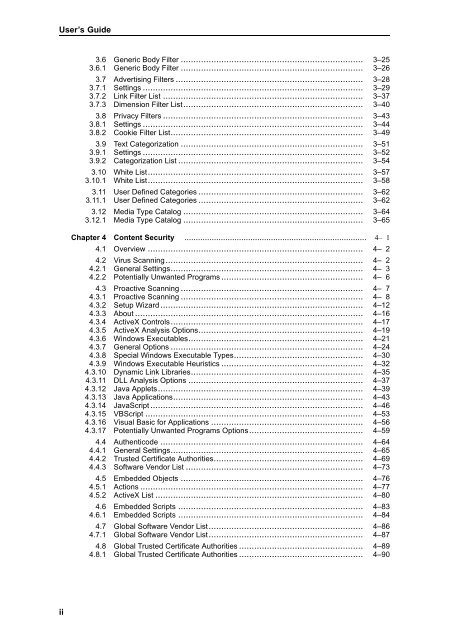
User’s <strong>Guide</strong><br />
ii<br />
3.6<br />
3.6.1<br />
Generic Body Filter ........................................................................<br />
Generic Body Filter ........................................................................<br />
3–25<br />
3–26<br />
3.7<br />
3.7.1<br />
3.7.2<br />
3.7.3<br />
Advertising Filters ..........................................................................<br />
Settings .......................................................................................<br />
Link Filter List ...............................................................................<br />
Dimension Filter List.......................................................................<br />
3–28<br />
3–29<br />
3–37<br />
3–40<br />
3.8<br />
3.8.1<br />
3.8.2<br />
Privacy Filters ...............................................................................<br />
Settings .......................................................................................<br />
Cookie Filter List............................................................................<br />
3–43<br />
3–44<br />
3–49<br />
3.9<br />
3.9.1<br />
3.9.2<br />
Text Categorization ........................................................................<br />
Settings .......................................................................................<br />
Categorization List .........................................................................<br />
3–51<br />
3–52<br />
3–54<br />
3.10<br />
3.10.1<br />
White List.....................................................................................<br />
White List.....................................................................................<br />
3–57<br />
3–58<br />
3.11<br />
3.11.1<br />
User Defined Categories .................................................................<br />
User Defined Categories .................................................................<br />
3–62<br />
3–62<br />
3.12<br />
3.12.1<br />
Media Type Catalog .......................................................................<br />
Media Type Catalog .......................................................................<br />
3–64<br />
3–65<br />
Chapter 4 Content Security ................................................................................ 4– 1<br />
4.1 Overview ..................................................................................... 4– 2<br />
4.2<br />
4.2.1<br />
4.2.2<br />
Virus Scanning..............................................................................<br />
General Settings............................................................................<br />
Potentially Unwanted Programs ........................................................<br />
4– 2<br />
4– 3<br />
4– 6<br />
4.3<br />
4.3.1<br />
4.3.2<br />
4.3.3<br />
4.3.4<br />
4.3.5<br />
4.3.6<br />
4.3.7<br />
4.3.8<br />
4.3.9<br />
4.3.10<br />
4.3.11<br />
4.3.12<br />
4.3.13<br />
4.3.14<br />
4.3.15<br />
4.3.16<br />
4.3.17<br />
Proactive Scanning ........................................................................<br />
Proactive Scanning ........................................................................<br />
Setup Wizard................................................................................<br />
About ..........................................................................................<br />
ActiveX Controls............................................................................<br />
ActiveX Analysis Options.................................................................<br />
Windows Executables.....................................................................<br />
General Options ............................................................................<br />
Special Windows Executable Types...................................................<br />
Windows Executable Heuristics ........................................................<br />
Dynamic Link Libraries....................................................................<br />
DLL Analysis Options .....................................................................<br />
Java Applets.................................................................................<br />
Java Applications...........................................................................<br />
JavaScript....................................................................................<br />
VBScript ......................................................................................<br />
Visual Basic for Applications ............................................................<br />
Potentially Unwanted Programs Options.............................................<br />
4– 7<br />
4– 8<br />
4–12<br />
4–16<br />
4–17<br />
4–19<br />
4–21<br />
4–24<br />
4–30<br />
4–32<br />
4–35<br />
4–37<br />
4–39<br />
4–43<br />
4–46<br />
4–53<br />
4–56<br />
4–59<br />
4.4<br />
4.4.1<br />
4.4.2<br />
4.4.3<br />
Authenticode ................................................................................<br />
General Settings............................................................................<br />
Trusted Certificate Authorities...........................................................<br />
Software Vendor List ......................................................................<br />
4–64<br />
4–65<br />
4–69<br />
4–73<br />
4.5<br />
4.5.1<br />
4.5.2<br />
Embedded Objects ........................................................................<br />
Actions ........................................................................................<br />
ActiveX List ..................................................................................<br />
4–76<br />
4–77<br />
4–80<br />
4.6<br />
4.6.1<br />
Embedded Scripts .........................................................................<br />
Embedded Scripts .........................................................................<br />
4–83<br />
4–84<br />
4.7<br />
4.7.1<br />
Global Software Vendor List.............................................................<br />
Global Software Vendor List.............................................................<br />
4–86<br />
4–87<br />
4.8<br />
4.8.1<br />
Global Trusted Certificate Authorities .................................................<br />
Global Trusted Certificate Authorities .................................................<br />
4–89<br />
4–90