Security Protocols I - Information Security
Security Protocols I - Information Security
Security Protocols I - Information Security
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
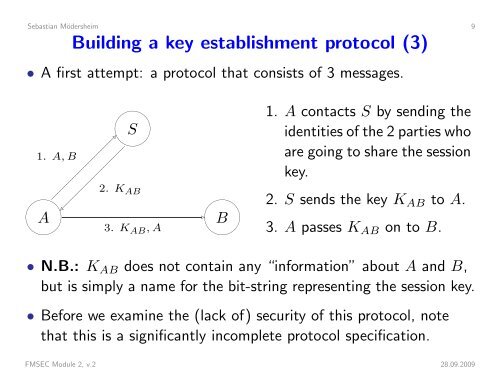
Sebastian Mödersheim 9Building a key establishment protocol (3)• A first attempt: a protocol that consists of 3 messages.1. A, B AS2. K AB 3. K AB , A B1. A contacts S by sending theidentities of the 2 parties whoare going to share the sessionkey.2. S sends the key K AB to A.3. A passes K AB on to B.• N.B.: K AB does not contain any “information” about A and B,but is simply a name for the bit-string representing the session key.• Before we examine the (lack of) security of this protocol, notethat this is a significantly incomplete protocol specification.FMSEC Module 2, v.2 28.09.2009