Security Protocols I - Information Security
Security Protocols I - Information Security
Security Protocols I - Information Security
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
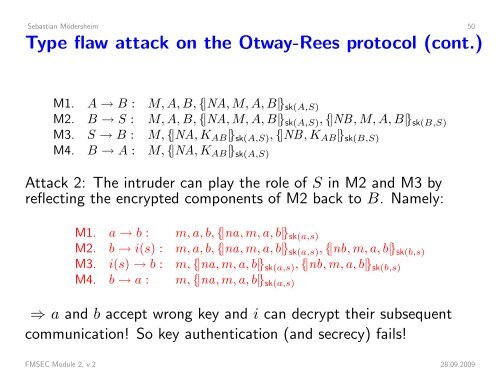
Sebastian Mödersheim 50Type flaw attack on the Otway-Rees protocol (cont.)M1. A → B : M, A, B, {|NA, M, A, B|} sk(A,S)M2. B → S : M, A, B, {|NA, M, A, B|} sk(A,S) , {|NB, M, A, B|} sk(B,S)M3. S → B : M, {|NA, K AB |} sk(A,S) , {|NB, K AB |} sk(B,S)M4. B → A : M, {|NA, K AB |} sk(A,S)Attack 2: The intruder can play the role of S in M2 and M3 byreflecting the encrypted components of M2 back to B. Namely:M1. a → b : m, a, b, {|na, m, a, b|} sk(a,s)M2. b → i(s) : m, a, b, {|na, m, a, b|} sk(a,s) , {|nb, m, a, b|} sk(b,s)M3. i(s) → b : m, {|na, m, a, b|} sk(a,s) , {|nb, m, a, b|} sk(b,s)M4. b → a : m, {|na, m, a, b|} sk(a,s)⇒ a and b accept wrong key and i can decrypt their subsequentcommunication! So key authentication (and secrecy) fails!FMSEC Module 2, v.2 28.09.2009