Security Protocols I - Information Security
Security Protocols I - Information Security
Security Protocols I - Information Security
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
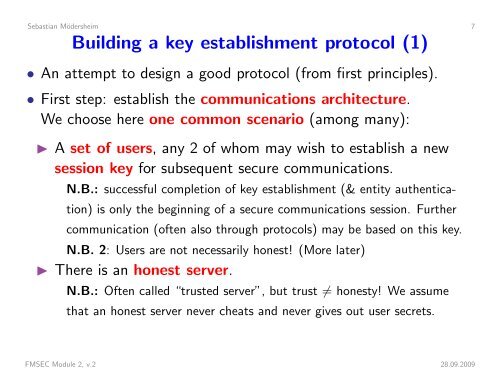
Sebastian Mödersheim 7Building a key establishment protocol (1)• An attempt to design a good protocol (from first principles).• First step: establish the communications architecture.We choose here one common scenario (among many):◮ A set of users, any 2 of whom may wish to establish a newsession key for subsequent secure communications.N.B.: successful completion of key establishment (& entity authentication)is only the beginning of a secure communications session. Furthercommunication (often also through protocols) may be based on this key.N.B. 2: Users are not necessarily honest! (More later)◮ There is an honest server.N.B.: Often called “trusted server”, but trust ≠ honesty! We assumethat an honest server never cheats and never gives out user secrets.FMSEC Module 2, v.2 28.09.2009