Security Protocols I - Information Security
Security Protocols I - Information Security
Security Protocols I - Information Security
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
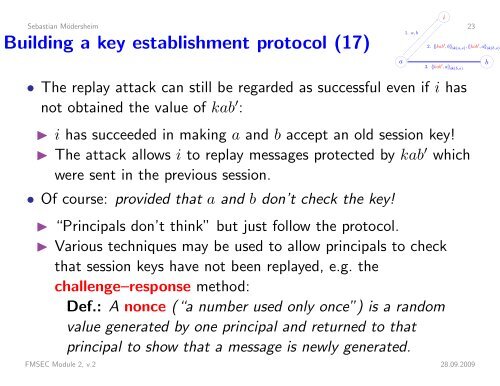
iSebastian Mödersheim 23Building a key establishment protocol (17)a 1. a, b 2. {|kab ′ , b|} sk(a,s) , {|kab ′ , a|} sk(b,s)3. {|kab ′ , a|} sk(b,s)• The replay attack can still be regarded as successful even if i hasnot obtained the value of kab ′ :◮ i has succeeded in making a and b accept an old session key!◮ The attack allows i to replay messages protected by kab ′ whichwere sent in the previous session.• Of course: provided that a and b don’t check the key!◮ “Principals don’t think” but just follow the protocol.◮ Various techniques may be used to allow principals to checkthat session keys have not been replayed, e.g. thechallenge–response method:Def.: A nonce (“a number used only once”) is a randomvalue generated by one principal and returned to thatprincipal to show that a message is newly generated.FMSEC Module 2, v.2 28.09.2009b