Security Protocols I - Information Security
Security Protocols I - Information Security
Security Protocols I - Information Security
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
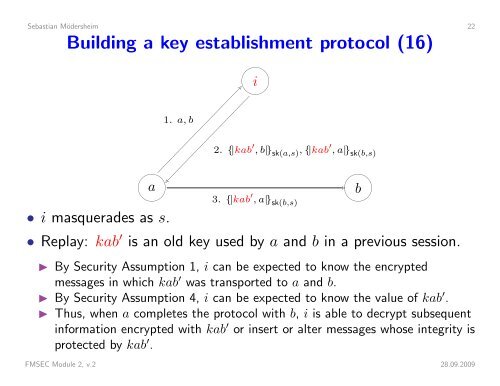
Sebastian Mödersheim 22Building a key establishment protocol (16)i 1. a, b2. {|kab ′ , b|} sk(a,s) , {|kab ′ , a|} sk(b,s) a• i masquerades as s. 3. {|kab ′ , a|} sk(b,s)• Replay: kab ′ is an old key used by a and b in a previous session.◮ By <strong>Security</strong> Assumption 1, i can be expected to know the encryptedmessages in which kab ′ was transported to a and b.◮ By <strong>Security</strong> Assumption 4, i can be expected to know the value of kab ′ .◮ Thus, when a completes the protocol with b, i is able to decrypt subsequentinformation encrypted with kab ′ or insert or alter messages whose integrity isprotected by kab ′ .FMSEC Module 2, v.2 28.09.2009b