Security Protocols I - Information Security
Security Protocols I - Information Security
Security Protocols I - Information Security
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
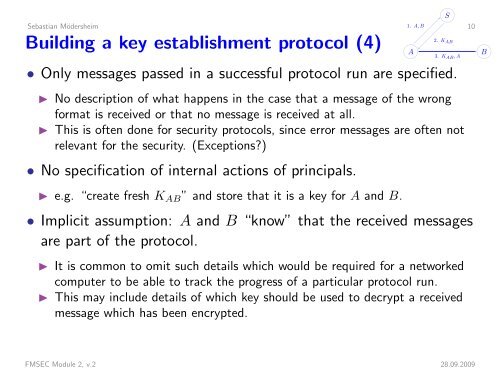
Sebastian Mödersheim 1. A, B10Building a key establishment protocol (4)AS2. K AB 3. K AB , A• Only messages passed in a successful protocol run are specified.◮ No description of what happens in the case that a message of the wrongformat is received or that no message is received at all.◮ This is often done for security protocols, since error messages are often notrelevant for the security. (Exceptions?)• No specification of internal actions of principals.◮ e.g. “create fresh K AB ” and store that it is a key for A and B.• Implicit assumption: A and B “know” that the received messagesare part of the protocol.◮ It is common to omit such details which would be required for a networkedcomputer to be able to track the progress of a particular protocol run.◮ This may include details of which key should be used to decrypt a receivedmessage which has been encrypted. BFMSEC Module 2, v.2 28.09.2009